Een gloednieuw, extreem gevaarlijk cryptogeld mijnwerker infectie daadwerkelijk is geïdentificeerd door onderzoekers bescherming. de malware, riep Hu.exe kan doelwit slachtoffers besmetten door gebruik te maken van een reeks methoden. De essentie achter de Hu.exe-mijnwerker is om cryptocurrency-mijnertaken te gebruiken op de computers van doelen om Monero-tokens te verkrijgen tegen de kosten van de slachtoffers. The result of this miner is the elevated electrical energy costs as well as if you leave it for longer amount of times Hu.exe may even harm your computers parts.
Hu.exe: distributiemethoden
De Hu.exe malware maakt gebruik 2 voorkeursmethoden waarbij gebruik wordt gemaakt aan te besmetten computersysteem doelen:
- Payload Levering via Prior Infecties. If an older Hu.exe malware is released on the victim systems it can instantly update itself or download a more recent variation. Dit is mogelijk door middel van de geïntegreerde upgrade commando dat de lancering krijgt. Dit gebeurt door het koppelen van een bepaalde vooraf gedefinieerde hacker gecontroleerde server die de malware code geeft. De gedownloade infectie zal zeker de naam van een Windows-service te verwerven en ook worden gepositioneerd in de “%systeem% temp” plaats. Vital gebouwen en het besturingssysteem configuratiebestanden worden omgezet om een meedogenloze en rustige infectie toestaan.
- Software Application Vulnerability Exploits. The most current variation of the Hu.exe malware have actually been discovered to be caused by the some ventures, volksmond begrepen te worden gebruikt in de ransomware aanslagen. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die zoekt naar als de poort open. Als aan deze voorwaarde wordt voldaan zal de oplossing te scannen en gegevens op te halen met betrekking tot deze, inbegrip van elke vorm van versie en opstelling informatie. Ventures en ook prominent gebruikersnaam en wachtwoord combinaties kan worden gedaan. Wanneer de exploit geactiveerd tegen de kwetsbare code mijnwerkers samen worden geïmplementeerd met de achterdeur. Dit zal het een dubbele infectie.
Afgezien van deze benaderingen andere methoden kan gebruik worden gemaakt van de eveneens. Mijnwerkers kunnen worden verspreid door phishing e-mails die in bulk in een SPAM-achtige manier over social design trucs worden verzonden evenals hangen om de lijders verwarren recht te laten geloven dat ze een boodschap hebben verkregen van een echte oplossing of bedrijf. De infectie bestanden kan direct worden bevestigd of geplaatst in het lichaam materialen in multimedia-inhoud of boodschap weblinks.
De oplichters kan eveneens produceren kwaadaardige landing pages die leverancier download kan imiteren en pagina's te installeren, softwaretoepassing download websites en ook andere regelmatig benaderd gebieden. Wanneer zij gebruik maken van vergelijkbare schijnbare domein legitieme adressen evenals de veiligheid en beveiligingscertificaten de klanten zouden kunnen worden overgehaald recht in te voeren met hen. Soms zijn ze gewoon te openen kan de mijnwerker infectie veroorzaken.
Een andere benadering zou zijn om payload dragers die kunnen worden verspreid gebruik te maken van die technieken of met behulp van het delen van gegevens netwerken te gebruiken, BitTorrent is slechts een van een van de meest populaire. Het wordt vaak gebruikt om zowel legitieme software en documenten en ook piraten inhoud verspreiden. Twee van één van de meest geprefereerde haul carriers zijn de volgende::
Andere methoden die in aanmerking door de overtreders kunnen worden genomen zijn het gebruik van internet browser hijackers -Schadelijk plugins die verenigbaar zijn gemaakt met één van de meest geprefereerde web internet browsers. Ze worden naar de juiste repositories ingediende reviews valse gebruikers en ook ontwikkelaarsaanmeldingsgegevens. In de meeste gevallen kan de beschrijvingen screenshots omvatten, video's en ingewikkelde beschrijvingen veelbelovende geweldige functie verbeteringen en efficiency optimalisaties. Maar bij de installatie van het gedrag van de getroffen internet browsers zal zeker transformeren- mensen zullen ontdekken dat ze zullen worden omgeleid naar een hacker gecontroleerde touchdown pagina en ook hun opstellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine en ook nieuwe tabbladen webpagina.

Hu.exe: Analyse
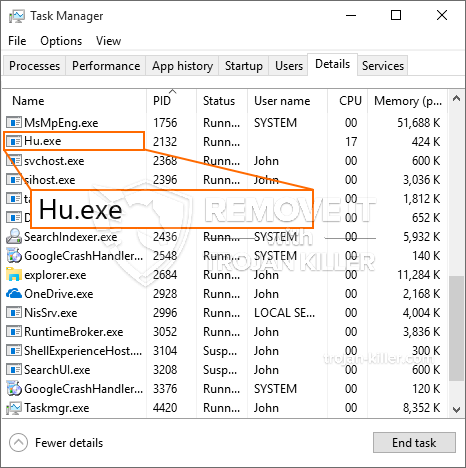
The Hu.exe malware is a traditional case of a cryptocurrency miner which depending upon its arrangement can cause a variety of dangerous actions. Its primary goal is to execute intricate mathematical tasks that will make the most of the offered system sources: processor, GPU, geheugen en ook de ruimte op de harde schijf. The method they operate is by attaching to a special server called mining swimming pool from where the needed code is downloaded. As quickly as one of the tasks is downloaded it will certainly be begun simultaneously, tal van omstandigheden kan worden gegaan voor zodra. When a given job is finished another one will be downloaded in its location and also the loophole will proceed until the computer system is powered off, the infection is eliminated or another comparable occasion happens. Cryptogeld zal worden toegekend aan de criminele controllers (hacken team of een eenzame cyberpunk) rechtstreeks naar hun begrotingen.
A hazardous quality of this classification of malware is that samples such as this one can take all system resources as well as virtually make the victim computer system pointless until the threat has been completely eliminated. A lot of them feature a persistent setup which makes them actually difficult to eliminate. Deze opdrachten zullen aanpassingen aan alternatieven te starten maken, setup data and Windows Registry values that will certainly make the Hu.exe malware start instantly once the computer is powered on. Access to recuperation food selections as well as choices may be obstructed which makes several hand-operated removal overviews practically worthless.
Deze bijzondere infectie zal zeker het opzetten van een Windows-service voor zichzelf, following the conducted protection analysis ther adhering to actions have actually been observed:
. Tijdens de mijnwerkeractiviteiten kan de bijbehorende malware verbinding maken met momenteel actieve Windows-services en geïnstalleerde applicaties van derden. By doing so the system managers may not discover that the resource lots comes from a different process.
| Naam | Hu.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Hu.exe |

These sort of malware infections are specifically effective at carrying out innovative commands if configured so. They are based upon a modular structure allowing the criminal controllers to orchestrate all sort of harmful actions. Onder de populaire gevallen is de aanpassing van het Windows-register – alterations strings related by the os can trigger serious performance interruptions as well as the inability to accessibility Windows solutions. Depending on the scope of adjustments it can additionally make the computer entirely pointless. On the various other hand manipulation of Registry worths coming from any type of third-party mounted applications can sabotage them. Sommige applicaties werken mogelijk niet meer om volledig te introduceren, terwijl andere plotseling kunnen stoppen met werken.
This certain miner in its present variation is concentrated on extracting the Monero cryptocurrency having a modified version of XMRig CPU mining engine. If the campaigns confirm successful then future versions of the Hu.exe can be released in the future. Als de malware maakt gebruik van software susceptabilities tot doel hosts te infecteren, het kan een deel van een gevaarlijke co-infectie met ransomware zijn evenals Trojans.
Elimination of Hu.exe is strongly suggested, because you risk not just a large electricity expense if it is working on your PC, but the miner may additionally execute other undesirable activities on it as well as also harm your COMPUTER completely.
Hu.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Hu.exe
STAP 5. Hu.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Hu.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Hu.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Hu.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Hu.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Hu.exe”.







