Een nieuw, uiterst gevaarlijk cryptogeld mijnwerker virus is gespot door onderzoekers bescherming. de malware, riep Dds.exe kunnen besmetten doel slachtoffers behulp van diverse middelen. De essentie achter de Dds.exe mijnwerker is om cryptogeld mijnwerker activiteiten te gebruiken op de computers van de patiënten met het oog op Monero symbolen bij slachtoffers kosten te verkrijgen. The outcome of this miner is the elevated power bills as well as if you leave it for longer periods of time Dds.exe might also damage your computers components.
Dds.exe: distributiemethoden
De Dds.exe malware maakt gebruik van 2 prominente technieken waarbij gebruik wordt gemaakt aan te besmetten computersysteem doelen:
- Payload Levering via Prior Infecties. If an older Dds.exe malware is released on the victim systems it can immediately upgrade itself or download a newer version. This is possible by means of the built-in update command which obtains the launch. Dit gebeurt door aan een bepaalde vooraf vastgestelde-hacker gecontroleerde server die de malware code biedt. De gedownloade infectie zal de naam van een Windows-service te verwerven, alsmede in de worden geplaatst “%systeem% temp” Gebied. Essential homes as well as operating system setup files are altered in order to allow a persistent and silent infection.
- Software Vulnerability Exploits. The latest variation of the Dds.exe malware have actually been found to be triggered by the some exploits, volksmond begrepen te worden gebruikt in de ransomware aanvallen. De infecties worden gedaan door zich te richten geopend oplossingen met behulp van de TCP-poort. De aanslagen worden geautomatiseerd door een hacker gecontroleerd kader die zoekt naar als de poort open. If this condition is satisfied it will certainly scan the service and also fetch details about it, including any version as well as setup information. Ventures en prominente gebruikersnaam en ook wachtwoordmixen kunnen worden gedaan. When the manipulate is caused versus the at risk code the miner will be released together with the backdoor. Dit zal zeker bieden een dubbele infectie.
In addition to these techniques various other strategies can be made use of too. Miners can be distributed by phishing e-mails that are sent out in bulk in a SPAM-like manner and depend on social engineering tricks in order to confuse the victims right into thinking that they have actually obtained a message from a legit solution or business. The infection files can be either directly attached or put in the body materials in multimedia material or message links.
The bad guys can additionally create destructive touchdown web pages that can pose vendor download web pages, software application download websites and various other often accessed locations. When they utilize similar sounding domain to legitimate addresses and also safety certificates the customers might be coerced right into communicating with them. In veel gevallen alleen het openen van hen kan de mijnwerker infectie activeren.
One more method would certainly be to utilize payload carriers that can be spread out using the above-mentioned techniques or using file sharing networks, BitTorrent is een van de meest geprefereerde. It is often made use of to distribute both genuine software program and also documents and pirate material. 2 van de meest prominente vervoerders zijn de volgende:
Various other techniques that can be thought about by the bad guys include making use of browser hijackers -harmful plugins which are made compatible with one of the most popular web internet browsers. They are posted to the pertinent databases with fake user testimonials and programmer credentials. In de meeste gevallen kunnen de samenvattingen screenshots bevatten, video clips as well as elaborate summaries encouraging wonderful feature improvements and efficiency optimizations. However upon installation the behavior of the impacted browsers will transform- individuals will certainly locate that they will be redirected to a hacker-controlled touchdown page as well as their setups could be altered – de standaard startpagina, zoekmachine op internet, alsmede nieuwe tabbladen pagina.

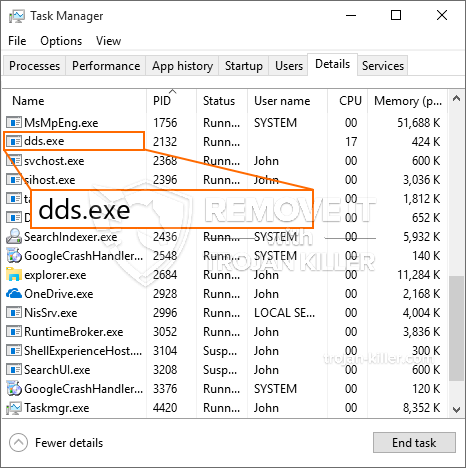
Dds.exe: Analyse
The Dds.exe malware is a classic instance of a cryptocurrency miner which depending upon its setup can cause a wide variety of hazardous activities. Its main goal is to execute intricate mathematical tasks that will certainly take advantage of the available system sources: processor, GPU, geheugen en schijfruimte. The method they operate is by attaching to a special server called mining pool where the needed code is downloaded and install. Zodra een van de banen is gedownload, wordt deze zeker meteen gestart, meerdere exemplaren kunnen worden gegaan want zodra. When a provided task is finished one more one will certainly be downloaded in its location as well as the loop will continue until the computer system is powered off, de infectie wordt verwijderd of er doet zich een andere vergelijkbare gebeurtenis voor. Cryptogeld zal zeker worden gecompenseerd naar de correctionele controllers (hacken groep of een eenzame hacker) rechtstreeks naar hun begrotingen.
A hazardous quality of this group of malware is that samples like this one can take all system sources as well as virtually make the victim computer system unusable till the risk has actually been entirely eliminated. A lot of them feature a persistent installation which makes them really challenging to eliminate. Deze commando's zullen zeker veranderingen ook opties maken, arrangement data and also Windows Registry values that will make the Dds.exe malware beginning instantly when the computer is powered on. Access to recovery menus and also options might be obstructed which makes many hands-on removal guides virtually worthless.
Deze specifieke infectie zal zeker een Windows-oplossing voor zichzelf configureren, following the performed protection evaluation ther following activities have been observed:
. During the miner operations the linked malware can hook up to currently running Windows services and also third-party installed applications. By doing so the system administrators may not discover that the resource load originates from a different process.
| Naam | Dds.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Dds.exe |

Dit soort malware-infecties zijn specifiek efficiënt in het uitvoeren van geavanceerde opdrachten, als ze zo zijn ingesteld. Ze zijn gebaseerd op een modulaire structuur waardoor de criminele controllers alle soorten gevaarlijk gedrag kunnen coördineren. Onder de geprefereerde gevallen is het aanpassen van het Windows register – Wijzigingenreeksen die door het besturingssysteem zijn verbonden, kunnen ernstige prestatieonderbrekingen veroorzaken en ook het onvermogen om Windows-oplossingen toegankelijk te maken. Afhankelijk van het bereik van de aanpassingen kan het ook de computer compleet zinloos maken. Aan de andere kant kan manipulatie van registerwaarden afkomstig van applicaties van derden deze saboteren. In sommige applicaties kan kort om helemaal los te vallen, terwijl anderen kunnen ineens stoppen met werken.
Deze specifieke mijnwerker in zijn bestaande versie is gericht op het minen van de Monero-cryptocurrency, bestaande uit een aangepaste versie van de XMRig CPU-mijnengine. If the campaigns confirm effective then future versions of the Dds.exe can be released in the future. Als de malware maakt gebruik van software applicatie kwetsbaarheden te misbruiken doelhosts infecteren, het kan een deel van een schadelijke co-infectie met ransomware zijn evenals Trojans.
Removal of Dds.exe is strongly recommended, aangezien u niet alleen het risico loopt van enorme elektriciteitskosten als het op uw pc werkt, toch kan de mijnwerker er bovendien verschillende andere ongewenste activiteiten op uitvoeren en uw pc volledig beschadigen.
Dds.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Dds.exe
STAP 5. Dds.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Dds.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Dds.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Dds.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Dds.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Dds.exe”.







