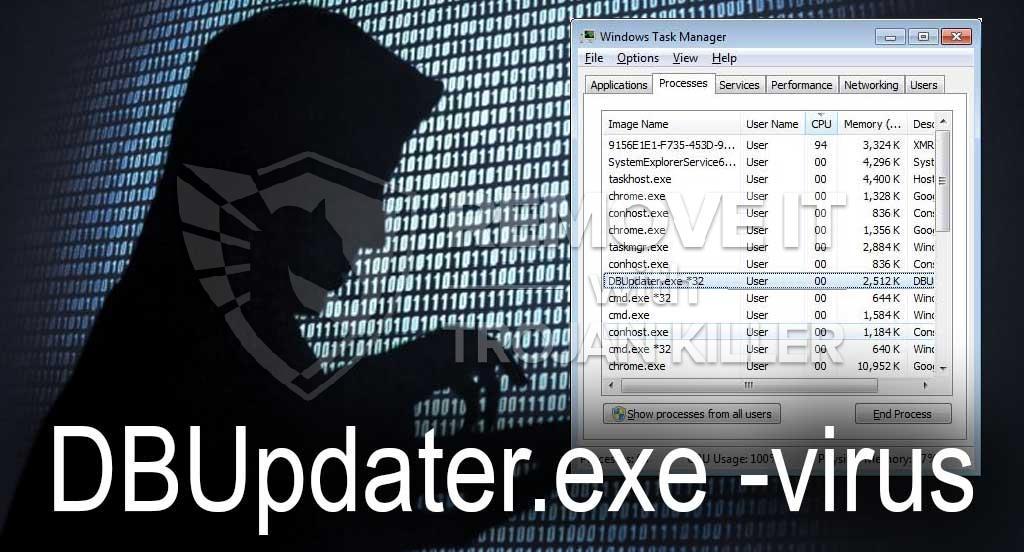
Een gloednieuw, echt gevaarlijk cryptocurrency mijnwerkervirus is geïdentificeerd door beveiligingsonderzoekers. de malware, riep DBUpdater.exe kunnen besmetten doel patiënten met behulp van een selectie van methoden. Het belangrijkste idee achter de DBUpdater.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computers van doelen om Monero-tokens bij patiënten te krijgen’ kosten. The outcome of this miner is the raised electrical energy costs and also if you leave it for longer periods of time DBUpdater.exe might even harm your computer system’s components.
DBUpdater.exe: distributiemethoden
De DBUpdater.exe malware maakt gebruik van 2 prominente technieken die worden gebruikt om computersysteemdoelen te besmetten:
- Payload Delivery gebruik Prior Infecties. If an older DBUpdater.exe malware is released on the sufferer systems it can immediately upgrade itself or download and install a more recent version. Dit is mogelijk door middel van de ingebouwde upgrade commando dat de lancering krijgt. Dit wordt gedaan door aansluiting op een speciaal vooraf bepaald hacker-gecontroleerde server die de malware code voorziet. Het gedownloade virus krijgt de naam van een Windows-oplossing en wordt in de “%systeem% temp” Gebied. Belangrijke gebouwen en actieve systeemindelingsbestanden worden gewijzigd om een consistente en stille infectie mogelijk te maken.
- Software Vulnerability Exploits. The latest variation of the DBUpdater.exe malware have actually been discovered to be triggered by the some ventures, algemeen duidelijk is voor toepassing in de ransomware strikes. De infecties worden gedaan door zich te richten geopend oplossingen via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die opgezocht als de poort open. Als aan dit probleem wordt voldaan, zal het zeker de oplossing controleren en ook informatie hierover krijgen, bestaande uit elk type variatie en ook arrangementgegevens. Ventures en ook prominente gebruikersnaam en wachtwoordmixen kunnen worden gedaan. Wanneer de exploit wordt veroorzaakt tegen de gevoelige code, zal de miner zeker worden vrijgegeven naast de achterdeur. Dit zal zeker bieden een dubbele infectie.
Naast deze methoden kunnen ook andere strategieën worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die in bulk worden verzonden op een SPAM-achtige manier en ook afhankelijk zijn van trucs voor sociale ontwerpen om de patiënten te verwarren met de overtuiging dat ze een bericht hebben ontvangen van een legitieme oplossing of bedrijf. De infectiegegevens kunnen rechtstreeks worden aangesloten of in de lichaamsonderdelen worden geplaatst in multimediamateriaal of tekstweblinks.
De daders kunnen ook kwaadaardige bestemmingswebpagina's produceren die de download van de leverancier kunnen imiteren en webpagina's kunnen installeren, portals voor het downloaden van softwaretoepassingen en andere regelmatig bezochte gebieden. Wanneer ze vergelijkbare verschijnende domeinnamen gebruiken voor legitieme adressen, evenals veiligheids- en beveiligingscertificaten, kunnen de gebruikers worden gedwongen rechtstreeks met hen te communiceren. Soms zijn ze alleen maar te openen kan verrekenen de mijnwerker infectie.
Een aanvullende techniek zou zeker zijn om gebruik te maken van aanbieders van payload-diensten die via die technieken of via netwerken voor het delen van bestanden kunnen worden verspreid, BitTorrent is slechts een van de meest geprefereerde. Er wordt regelmatig gebruik van gemaakt om zowel legitieme softwaretoepassingen als gegevens en piratenmateriaal te verspreiden. Twee van één van de meest populaire haul service providers zijn de volgende:
Andere benaderingen waarmee de overtreders rekening kunnen houden, zijn onder meer het gebruik van browserkapers - gevaarlijke plug-ins die compatibel zijn gemaakt met de meest populaire internetbrowsers. Ze worden in de juiste databases geplaatst met nepgetuigenissen van klanten en ook kwalificaties voor ontwerpers. Vaak is het zo samenvattingen kunnen screenshots omvatten, videoclips en geavanceerde beschrijvingen die uitstekende functieverbeteringen en prestatie-optimalisaties beloven. Desalniettemin zullen de gewoonten van de getroffen browsers tijdens de installatie zeker veranderen- individuen zullen zeker ontdekken dat ze worden omgeleid naar een door een hacker bestuurde bestemmingspagina en dat ook hun instellingen kunnen worden gewijzigd – de standaard startpagina, online zoekmachine en ook nieuwe tabbladen webpagina.
DBUpdater.exe: Analyse
The DBUpdater.exe malware is a traditional case of a cryptocurrency miner which relying on its configuration can cause a wide variety of hazardous activities. Its major objective is to perform complex mathematical jobs that will capitalize on the available system sources: processor, GPU, geheugen evenals harde schijf ruimte. The means they operate is by attaching to an unique server called mining pool where the needed code is downloaded and install. As quickly as one of the tasks is downloaded it will be started at the same time, meerdere exemplaren kan zo snel worden uitgevoerd bij. When a given job is completed another one will be downloaded in its place and the loop will certainly continue until the computer is powered off, de infectie wordt verwijderd of een andere vergelijkbare gebeurtenis vindt plaats. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken team of een eenzame hacker) direct naar hun begrotingen.
A hazardous attribute of this group of malware is that examples similar to this one can take all system sources and also virtually make the target computer pointless till the risk has been entirely gotten rid of. De meerderheid van hen zijn voorzien van een hardnekkige setup die hen echt moeilijk om zich te ontdoen van maakt. Deze commando's zullen zeker aanpassingen ook opties maken, configuration files and also Windows Registry values that will certainly make the DBUpdater.exe malware beginning instantly when the computer system is powered on. Accessibility to healing menus and alternatives may be blocked which provides many manual elimination overviews practically useless.
Deze bijzondere infectie zal het inrichten van een Windows-service voor zichzelf, naar aanleiding van de uitgevoerde security analysis ther volgende activiteiten zijn waargenomen:
| Naam | DBUpdater.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove DBUpdater.exe |
Dit soort malware-infecties zijn bijzonder betrouwbaar bij het uitvoeren van innovatieve opdrachten als ze zo zijn ingesteld. Ze zijn gebaseerd op een modulair kader waardoor de criminele controleurs allerlei onveilige handelingen kunnen beheren. Onder de voorkeursvoorbeelden is het aanpassen van het Windows register – Aanpassingsstrings die verband houden met het besturingssysteem kunnen aanzienlijke verstoringen in de efficiëntie en het niet openen van Windows-oplossingen veroorzaken. Afhankelijk van de omvang van de veranderingen kan het het computersysteem bovendien volledig zinloos maken. Aan de andere kant kan aanpassing van registerwaarden die behoren tot door derden ingestelde applicaties deze saboteren. Sommige applicaties kunnen mogelijk niet volledig worden gestart, terwijl andere plotseling kunnen stoppen met werken.
Deze bijzondere miner in zijn huidige variant is gericht op de winning Monero cryptogeld bestaande uit een gewijzigde variant van XMRig CPU mining engine. If the campaigns confirm effective after that future variations of the DBUpdater.exe can be released in the future. Als de malware gebruik maakt van software-applicatie susceptabilities te besmetten doelhosts, het kan een deel van een schadelijke co-infectie met ransomware zijn evenals Trojans.
Removal of DBUpdater.exe is highly recommended, omdat u niet alleen het risico loopt op enorme elektriciteitskosten als het op uw pc werkt, de mijnwerker kan er echter ook andere ongewenste taken op uitvoeren en zelfs uw pc permanent beschadigen.
DBUpdater.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove DBUpdater.exe
STAP 5. DBUpdater.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove DBUpdater.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “DBUpdater.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “DBUpdater.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “DBUpdater.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “DBUpdater.exe”.