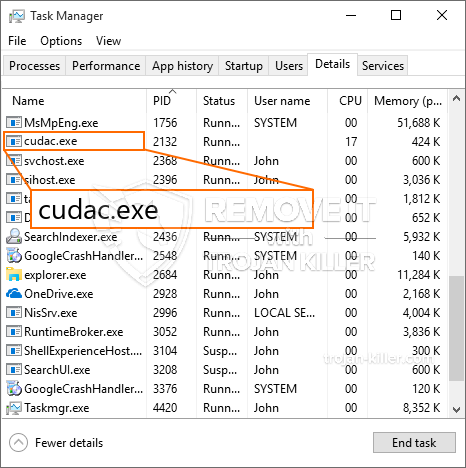
Een gloednieuw, echt schadelijk cryptogeld mijnwerker virus is ontdekt door veiligheid en beveiliging onderzoekers. de malware, riep Cudac.exe kan doelslachtoffers op verschillende manieren infecteren. Het belangrijkste idee achter de Cudac.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computers van patiënten om Monero-symbolen tegen doelkosten te krijgen. The result of this miner is the raised power costs and also if you leave it for longer time periods Cudac.exe might also harm your computers parts.
Cudac.exe: distributiemethoden
De Cudac.exe malware maakt gebruik van twee populaire technieken die worden gebruikt om computerdoelen te besmetten:
- Payload Levering door middel van Prior Infecties. If an older Cudac.exe malware is released on the victim systems it can automatically upgrade itself or download and install a newer variation. Dit is mogelijk met behulp van de geïntegreerde upgrade-opdracht die de lancering krijgt. Dit gebeurt door het koppelen van een bepaalde vooraf gedefinieerde hacker gecontroleerde server die de malware code voorziet. De gedownloade en geïnstalleerde infectie krijgt zeker de naam van een Windows-oplossing en wordt in het “%systeem% temp” plaats. Belangrijke residentiële eigendommen en ook configuratiegegevens van het besturingssysteem worden gewijzigd om een consistente en stille infectie mogelijk te maken.
- Software programma Kwetsbaarheid Exploits. The newest version of the Cudac.exe malware have actually been located to be triggered by the some ventures, beroemde erkend voor wordt gebruik gemaakt van in de ransomware aanslagen. De infecties worden gedaan door zich te richten geopend diensten via de TCP-poort. De slagen worden geautomatiseerd door een hacker bestuurde structuur die zoekt naar als de poort open. Als dit probleem zich voordoet, zal het de dienst controleren en informatie hierover verkrijgen, bestaande uit elke vorm van versie en configuratiegegevens. Zowel exploits als geprefereerde combinaties van gebruikersnaam en wachtwoord kunnen worden gedaan. Wanneer de manipulatie wordt uitgevoerd ten opzichte van de gevoelige code, zal de mijnwerker zeker samen met de achterdeur worden ingezet. Dit zal een dubbele infectie presenteren.
Naast deze methoden kunnen ook verschillende andere strategieën worden gebruikt. Mijnwerkers kunnen worden verspreid door phishing-e-mails die in bulk op een SPAM-achtige manier worden verzonden, en vertrouwen op social engineering-methoden om de doelwitten te verwarren door te denken dat ze een bericht hebben gekregen van een legitieme oplossing of bedrijf. De virusgegevens kunnen rechtstreeks worden aangesloten of in de lichaamscomponenten worden gestopt in multimedia-inhoud of berichtweblinks.
De boosdoeners kunnen bovendien schadelijke touchdown-pagina's ontwikkelen die download- en installatiepagina's van leveranciers kunnen opleveren, downloadsites van softwareprogramma's en andere regelmatig bezochte gebieden. Wanneer ze gebruik maken van domeinnamen die lijken op gerenommeerde adressen en ook van veiligheidscertificaten, kunnen de individuen worden gedwongen om met hen om te gaan. In sommige gevallen alleen het openen van hen kan de mijnwerker een infectie veroorzaken.
Een andere strategie zou zijn om gebruik te maken van ladingsdragers die kunnen worden verspreid door gebruik te maken van die benaderingen of door middel van netwerken voor het delen van bestanden, BitTorrent is een van de meest geprefereerde. Het wordt regelmatig gebruikt om zowel echte softwaretoepassingen als bestanden te verspreiden, en ook om webinhoud te kopiëren. Twee van de meest geprefereerde ladingsdragers zijn de volgende:
Andere technieken die door de criminelen kunnen worden overwogen, zijn het gebruik van webbrowser-hijackers - schadelijke plug-ins die compatibel zijn gemaakt met de meest geprefereerde webbrowsers. Ze worden in de juiste databases geplaatst met valse individuele recensies en ook met ontwikkelaarsreferenties. In veel gevallen kunnen de beschrijvingen screenshots bevatten, videoclips en ingewikkelde beschrijvingen die aansprekende fantastische verbeteringen van eigenschappen en efficiëntie-optimalisaties. Niettemin zal bij installatie het gedrag van de beïnvloede browsers zeker veranderen- individuen zullen zeker merken dat ze worden omgeleid naar een door hackers gecontroleerde bestemmingswebsite en dat hun instellingen kunnen worden gewijzigd – de standaard webpagina, zoekmachine evenals nieuwe tabbladen webpagina.

Cudac.exe: Analyse
The Cudac.exe malware is a classic situation of a cryptocurrency miner which depending upon its setup can create a wide array of unsafe actions. Its main goal is to do complex mathematical tasks that will certainly capitalize on the available system resources: processor, GPU, geheugen evenals harde schijf ruimte. The way they function is by connecting to an unique server called mining swimming pool where the required code is downloaded. Zo snel als een van de banen wordt gedownload zal tegelijkertijd worden begonnen, meerdere exemplaren kunnen worden gegaan want zodra. When a given task is completed one more one will certainly be downloaded and install in its place and also the loop will certainly proceed until the computer system is powered off, de infectie wordt weggedaan of een andere soortgelijke gebeurtenis plaatsvindt. Cryptogeld zal beloond worden naar de correctionele controllers (hacken groep of een enkele hacker) direct naar hun begrotingen.
An unsafe feature of this group of malware is that examples similar to this one can take all system sources and practically make the target computer system pointless till the danger has actually been completely eliminated. Most of them feature a persistent installation that makes them truly hard to eliminate. Deze commando's zullen zeker aanpassingen ook opties maken, configuration documents and also Windows Registry values that will certainly make the Cudac.exe malware beginning instantly as soon as the computer system is powered on. Access to recovery food selections and choices might be blocked which renders lots of hands-on elimination overviews almost pointless.
Dit bepaalde infectie zal een Windows-oplossing voor zichzelf de configuratie, adhering to the carried out safety evaluation ther adhering to activities have been observed:
. During the miner operations the associated malware can connect to currently running Windows solutions as well as third-party mounted applications. By doing so the system managers might not observe that the source lots originates from a separate process.
| Naam | Cudac.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Cudac.exe |

Dit soort malware-infecties zijn specifiek betrouwbaar bij het vervullen van geavanceerde commando's als zo opgezet. Ze zijn gebaseerd op een modulair kader waardoor de criminele controllers om allerlei onveilige handelingen beheren. Een van de prominente gevallen is de wijziging van het Windows-register – modificaties strings met elkaar verbonden door de os kan aanzienlijke efficiëntie verstoringen en ook het feit dat de toegang tot Windows-oplossingen krijgen veroorzaken. Zich baserend op het gebied van aanpassingen kan het ook de computer volledig zinloos. Aan de andere kant de controle over Registry waardes afkomstig van elke vorm van derden opgezet kunnen toepassingen hen ondermijnen. Sommige toepassingen kan mislukken om volledig te introduceren, terwijl anderen onverwacht werken kan stoppen.
Deze specifieke mijnwerker in de bestaande variatie is geconcentreerd op het extraheren van de Monero cryptogeld waaronder een aangepaste versie van XMRig CPU mijnbouw motor. If the projects verify successful after that future versions of the Cudac.exe can be launched in the future. Als de malware maakt gebruik van software programma susceptabilities tot doel gastheren besmetten, het kan een deel van een schadelijke co-infectie met ransomware zijn evenals Trojans.
Elimination of Cudac.exe is strongly advised, gezien het feit dat u het risico niet alleen een groot elektrisch vermogen kosten of het werkt op uw computer, maar de mijnwerker kan bovendien het uitvoeren van diverse andere ongewenste taken op en ook zelfs uw computer volledig schaden.
Cudac.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Cudac.exe
STAP 5. Cudac.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Cudac.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Cudac.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Cudac.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Cudac.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Cudac.exe”.







