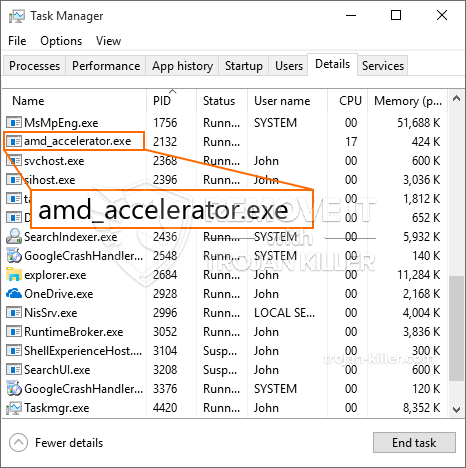
Een nieuw, Echt gevaarlijk cryptocurrency-mijnwerkervirus is gevonden door veiligheids- en beveiligingswetenschappers. de malware, riep Amd_accelerator.exe kunnen besmetten doel patiënten met behulp van een verscheidenheid van manieren. Het belangrijkste idee achter de Amd_accelerator.exe-mijnwerker is om cryptocurrency-mijnwerkeractiviteiten in te zetten op de computersystemen van slachtoffers om Monero-symbolen te verkrijgen tegen de kosten van de slachtoffers. The end result of this miner is the raised electrical power expenses and if you leave it for longer amount of times Amd_accelerator.exe may also harm your computer systems elements.
Amd_accelerator.exe: distributiemethoden
De Amd_accelerator.exe malware toepassingen 2 voorkeursmethoden die worden gebruikt om computerdoelen te infecteren:
- Payload Levering via Prior Infecties. If an older Amd_accelerator.exe malware is released on the sufferer systems it can immediately update itself or download and install a more recent version. Dit is mogelijk door middel van het geïntegreerde update-commando dat de lancering verkrijgt. Dit wordt gedaan door verbinding te maken met een bepaalde vooraf gedefinieerde, door een hacker bestuurde server die de malwarecode geeft. De gedownloade infectie krijgt zeker de naam van een Windows-oplossing en wordt in het “%systeem% temp” Gebied. Important residential or commercial properties and operating system configuration documents are transformed in order to allow a relentless and also quiet infection.
- Software Application Vulnerability Exploits. The newest variation of the Amd_accelerator.exe malware have been located to be caused by the some ventures, bekend om te worden gebruikt in de ransomware strikes. De infecties worden gedaan door zich te richten geopend oplossingen met behulp van de TCP-poort. De aanvallen worden geautomatiseerd door een hacker gecontroleerd kader dat bedoeld indien de poort open. If this condition is satisfied it will certainly check the service and retrieve info regarding it, including any variation and configuration data. Ventures en prominente gebruikersnaam en ook wachtwoordcombinaties kunnen worden gedaan. When the make use of is caused versus the at risk code the miner will certainly be released together with the backdoor. Dit zal zeker presenteren een dubbele infectie.
Naast deze technieken kunnen ook andere benaderingen worden gebruikt. Miners can be dispersed by phishing e-mails that are sent in bulk in a SPAM-like fashion and also depend on social engineering tricks in order to perplex the sufferers right into thinking that they have received a message from a legitimate service or firm. The virus documents can be either straight affixed or placed in the body components in multimedia content or text links.
The bad guys can also create destructive landing web pages that can pose vendor download and install pages, software application download sites as well as other often accessed places. When they use similar sounding domain names to genuine addresses and safety and security certificates the customers may be persuaded into interacting with them. In sommige gevallen kan het simpelweg openen ervan de mijnwerker-infectie veroorzaken.
One more strategy would be to utilize haul service providers that can be spread out utilizing the above-mentioned methods or through file sharing networks, BitTorrent behoort tot een van de meest populaire. It is often used to disperse both legit software application and also files and also pirate material. Twee van de meest geprefereerde ladingdragers zijn de volgende::
Other approaches that can be taken into consideration by the lawbreakers include making use of internet browser hijackers -harmful plugins which are made suitable with the most popular web browsers. They are posted to the appropriate repositories with phony individual testimonials and designer credentials. Vaak de beschrijvingen bestaan uit schermafbeeldingen, video clips as well as intricate summaries encouraging fantastic attribute improvements and also performance optimizations. Nevertheless upon installment the habits of the affected browsers will certainly alter- individuals will certainly locate that they will be redirected to a hacker-controlled landing page as well as their setups may be modified – de standaard startpagina, zoekmachine op internet, evenals gloednieuwe tabs pagina.

Amd_accelerator.exe: Analyse
The Amd_accelerator.exe malware is a traditional instance of a cryptocurrency miner which depending upon its arrangement can create a wide variety of hazardous activities. Het belangrijkste doel is om ingewikkelde wiskundige taken uit te voeren die zeker zullen profiteren van de aangeboden systeembronnen: processor, GPU, geheugen evenals harde schijf ruimte. De methode die ze gebruiken, is door verbinding te maken met een unieke server genaamd mining pool van waaruit de vereiste code wordt gedownload. Zodra een van de banen wordt gedownload zal worden gestart op hetzelfde moment, meerdere instanties kunnen tegelijkertijd worden uitgevoerd. Wanneer een bepaalde taak is voltooid, wordt er nog één op zijn locatie gedownload en loopt de lus door totdat het computersysteem is uitgeschakeld, de infectie wordt verwijderd of een andere vergelijkbare gebeurtenis vindt plaats. Cryptogeld zal zeker beloond worden naar de correctionele controllers (hacken groep of een enkele cyberpunk) rechtstreeks naar hun begrotingen.
Een onveilige kwaliteit van deze categorie malware is dat voorbeelden zoals deze alle systeembronnen kunnen gebruiken en het doelcomputersysteem praktisch zinloos kunnen maken totdat de bedreiging volledig is geëlimineerd. De meeste hebben een permanente installatie waardoor ze moeilijk te verwijderen zijn. Deze opdrachten zullen aanpassingen aan alternatieven te starten maken, arrangement files as well as Windows Registry values that will certainly make the Amd_accelerator.exe malware begin immediately as soon as the computer is powered on. De toegang tot herstelmenu's en ook keuzes kunnen worden belemmerd, waardoor talloze handmatige verwijderingsoverzichten praktisch nutteloos zijn.
Deze specifieke infectie zal opstelling een Windows-service voor zichzelf, Door te voldoen aan de uitgevoerde veiligheids- en beveiligingsevaluatie zijn de volgende acties daadwerkelijk nageleefd:
. Tijdens de miner-procedures kan de aangesloten malware linken naar reeds lopende Windows-oplossingen en door derden geïnstalleerde applicaties. Hierdoor zien de systeembeheerders mogelijk niet dat de bronbelasting afkomstig is van een andere procedure.
| Naam | Amd_accelerator.exe |
|---|---|
| Categorie | Trojaans |
| Sub-categorie | cryptogeld Miner |
| gevaren | Hoog CPU-gebruik, Internet snelheidsreductie, PC crashes en bevriest en etc. |
| Hoofddoel | Om geld te verdienen voor cybercriminelen |
| Distributie | torrents, Gratis spellen, Cracked Apps, E-mail, dubieuze websites, exploits |
| Verwijdering | Installeren GridinSoft Anti-Malware to detect and remove Amd_accelerator.exe |

Dit soort malware-infecties zijn bijzonder efficiënt bij het uitvoeren van geavanceerde commando's, indien zo ingesteld. They are based on a modular structure enabling the criminal controllers to manage all kinds of harmful behavior. Onder de geprefereerde gevallen is het aanpassen van het Windows register – alterations strings associated by the operating system can cause serious performance disruptions and the failure to access Windows services. Depending upon the scope of adjustments it can likewise make the computer system completely pointless. On the various other hand adjustment of Registry worths belonging to any type of third-party set up applications can undermine them. Sommige applicaties werken mogelijk niet meer om volledig te introduceren, terwijl andere plotseling kunnen stoppen met werken.
This certain miner in its existing variation is concentrated on extracting the Monero cryptocurrency containing a changed version of XMRig CPU mining engine. If the projects prove successful then future versions of the Amd_accelerator.exe can be launched in the future. Als de malware maakt gebruik van software kwetsbaarheden te misbruiken doelhosts infecteren, het kan zijn onderdeel van een schadelijke co-infectie met ransomware en Trojaanse paarden.
Elimination of Amd_accelerator.exe is highly advised, because you take the chance of not only a large electrical energy costs if it is operating on your PC, however the miner may also do various other unwanted tasks on it and even damage your COMPUTER permanently.
Amd_accelerator.exe removal process
STAP 1. Allereerst, je moet downloaden en te installeren GridinSoft Anti-Malware.
STAP 2. Dan moet je kiezen “Snelle scan” of “Volledige scan”.
STAP 3. Ren naar uw computer te scannen
STAP 4. Nadat de scan is voltooid, je nodig hebt om te klikken op “Van toepassing zijn” button to remove Amd_accelerator.exe
STAP 5. Amd_accelerator.exe Removed!
video Guide: How to use GridinSoft Anti-Malware for remove Amd_accelerator.exe
Hoe te voorkomen dat uw pc wordt geïnfecteerd met “Amd_accelerator.exe” in de toekomst.
Een krachtige antivirus oplossing die kan detecteren en blokkeren fileless malware is wat je nodig hebt! Traditionele oplossingen voor het detecteren van malware op basis van virusdefinities, en vandaar dat zij vaak niet kunnen detecteren “Amd_accelerator.exe”. GridinSoft Anti-Malware biedt bescherming tegen alle vormen van malware, waaronder fileless malware zoals “Amd_accelerator.exe”. GridinSoft Anti-Malware biedt cloud-gebaseerde gedrag analyzer om alle onbekende bestanden met inbegrip van zero-day malware te blokkeren. Deze technologie kan detecteren en volledig te verwijderen “Amd_accelerator.exe”.







