
Cybereason specialisten bestudeerde de Phoenix malware, die deze zomer arriveerde en een hybride presenteert van een keylogger en een infostealer. Onderzoekers hebben ontdekt dat Phoenix meer kan uitschakelen dan 80 beveiligingsproducten.
The malware spreads according to the MaaS model ("Malware als service") en is al verantwoordelijk voor 10,000 infecties.Aangezien Phoenix wordt verkocht als abonnementsproduct, prices range from $14.99 a month to $78.99 for a lifetime subscription. Cybereason analysts write that Phoenix is a development of an experienced malware author. Blijkbaar, the author of the Alpha Keylogger malware, who died earlier this year, was originally behind his creation.
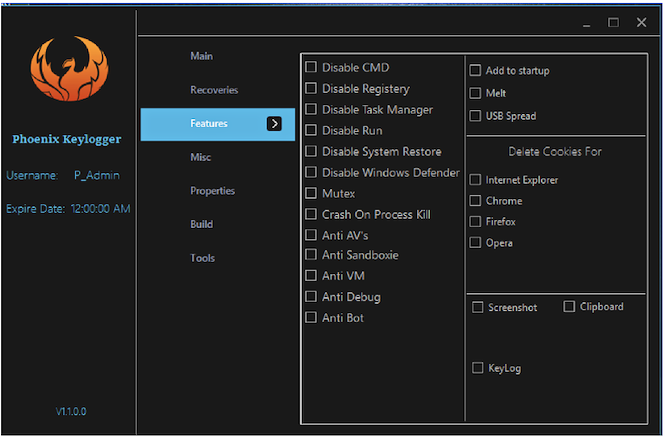
“Phoenix is more than just a keylogger, it has broad information-stealing capabilities and self-defense mechanisms, which include an anti-AV module that attempts to stop over 80 beveiligingsproducten, and the ability to exfiltrate data through Telegram”, - schrijven Cybereason specialists.
Indeed, over the past few months, Phoenix has evolved from a simple keylogger into a multifunctional trojan designed to steal information (Infostealer). If in the first version the malicious version was provided only for the ability to intercept keystrokes, then newer versions of the malware steal passwords from almost twenty different browsers, four email clients, FTP clients and instant messengers. In aanvulling op, the malware can steal data from the clipboard, take screenshots and download additional malware.
Information stolen from victims is transmitted to malware operators via SMTP, FTP or Telegram.
Lees ook: Criminelen geven links naar RAT trojan in WebEx uitnodigingen
Phoenix also acquired aggressive modules against anti-viruses and VMs that try to prevent detection and analysis of malware. Both modules work the same way: they try to shut down a number of processes before the malware continues to work, voor deze, referring to a predefined list of names. This list includes the names of more than 80 well-known security products and virtual machines, which are often used for reverse engineering and analysis of malware.
Analysts say that Phoenix could use its capabilities to achieve a permanent presence in the system, but its operators have little interest in it. Volgens de onderzoekers, more often malware is used as a one-time solution for data theft and is not used for long-term monitoring of victims. A few seconds after infection, Phoenix steals all the necessary confidential data, and on this its function finishes. Criminals most often sale information stolen in this way on the darknet.
