
Als onderdeel van de "dinsdagupdates" van mei, Microsoft heeft de kritieke kwetsbaarheid CVE-2019-0708 opgelost (ook bekend als BlueKeep) gerelateerd aan de werking van Remote Desktop Services (RDS) en RDP.
EENHoewel de technische details van het probleem niet bekend zijn gemaakt vanwege het hoge dreigingsniveau, het is bekend dat aanvallers met behulp van deze bug willekeurige code zonder toestemming kunnen uitvoeren en hun malware als een worm kunnen verspreiden, zoals, Bijvoorbeeld, het was beroemd WannaCry En NietPetya malware.De kwestie is gevaarlijk voor Windows Server 2008, ramen 7, ramen 2003 en Windows XP, voor deze versies zijn uitgebracht beveiligingsupdates.
Microsoft-experts hebben al twee keer voor dit probleem gewaarschuwd, en experts van verschillende informatiebeveiligingsbedrijven (inclusief Zerodium, McAfee, check Point En Kaspersky Lab) en onafhankelijke onderzoekers hebben het concept van exploits voor BlueKeep bewezen.
De code voor deze exploits is niet openbaar gemaakt vanwege een hoog risico. In aanvulling op, voor de kwetsbaarheid is al een module gemaakt Metasploit (ook niet beschikbaar in het publieke domein).
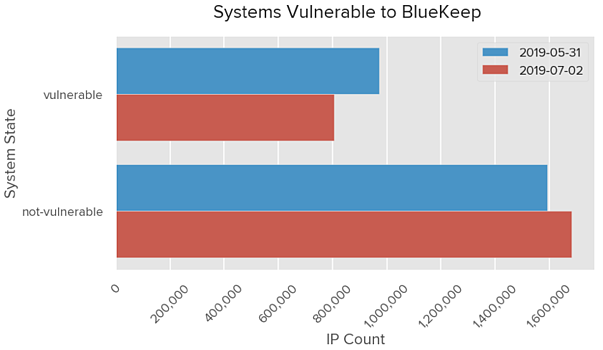
Vorige week, BitSight experts gepubliceerd weer een deprimerende statistiek: op basis van hun data, wat betreft 800,000 apparaten zijn nog steeds kwetsbaar voor BlueKeep. Blijkbaar, gebruikers van deze apparaten moeten nadenken over het zo snel mogelijk installeren van patches, sinds gisteren op GitHub was een presentatie gepubliceerd waarin het gebruik van de kwetsbaarheid en het maken van een exploit worden beschreven.
Dia's van deze presentatie bijna volledig in het Chinees geschreven. Op hen vermeld 2019 Security Development Conference en naam van het beroemde Chinese bedrijf Tencent KeenLab. Op de twee dia's staat ook het woord “demo”.
ArsTechnica journalisten gevraagd informatiebeveiligingsspecialisten over de presentatie, het interviewen van een onafhankelijke deskundige Marcus Hutchins en Rendition Infosec mede-oprichter en voormalig ontwikkelaar van exploits voor de NSA, Jakke Williams.
"Een van de weinige dingen die aanvallen in de echte wereld in de weg staan, is de expertise die nodig is om exploits te schrijven die op afstand code uitvoeren zonder eerst de computer te laten crashen", - zei Marcus Hutchins.
In het algemeen, beide specialisten zijn het erover eens dat de situatie zeer ernstig is, aangezien het publiceren van een gedetailleerde presentatie de kans op het maken van RCE-exploits voor BlueKeep aanzienlijk verkleint. Feit is dat de dia's in detail laten zien hoe heap spraying moet worden geïmplementeerd, Dat is, volgens de presentatie, is een van de moeilijkste taken tijdens het maken van een exploit.
“Het is de meest gedetailleerde openbaar beschikbare technische documentatie die we tot nu toe hebben gezien”, - legde Jake Williams uit.
Hij suggereerde ook dat Tencent KeenLab-experts duidelijk een RCE-exploit voor BlueKeep hebben gemaakt en op de conferentie hebben gedemonstreerd., hoewel de PoC zelf niet is gepubliceerd.
Eerder, beveiligingsexperts waren van mening dat de exploits van BlueKeep rond half augustus algemeen beschikbaar zouden zijn, na het einde van Zwarte hoed En Defcon conferenties in Las Vegas. Echter, nu zijn ze geneigd te veronderstellen dat dit eerder zal gebeuren.
