Symantec analisten gedeeld interessante observaties.
EENs it discovered, some Chinese cybercriminal group used NSA tools a year before hackers from Shadow Brokers leaked it into network.Deze Chinese groep wordt opgespoord onder verschillende namen, met inbegrip van Buckeye, APT3, UPS Team, Gothic Panda en TG-0110.
Researchers link its activity with PRC’s Ministry of State Security. Buckeye was noted with cyberattacks on such corporations as Siemens, Trimble and Moody’s Analytics.
In their cyberoperations group used several malware programs, among them was famous backdoor DoublePulsar.
Also researchers noted presence in the Buckeye arsenal Bemstour exploit that was responsible for backdoor delivery on the targeted computer.
It is worth reminding that DoublePulsar became famous in April 2017, just after publication of NSA tools by Shadow Brokers. This leakage was one the most significant events in the history of cybersecurity in the recent years.
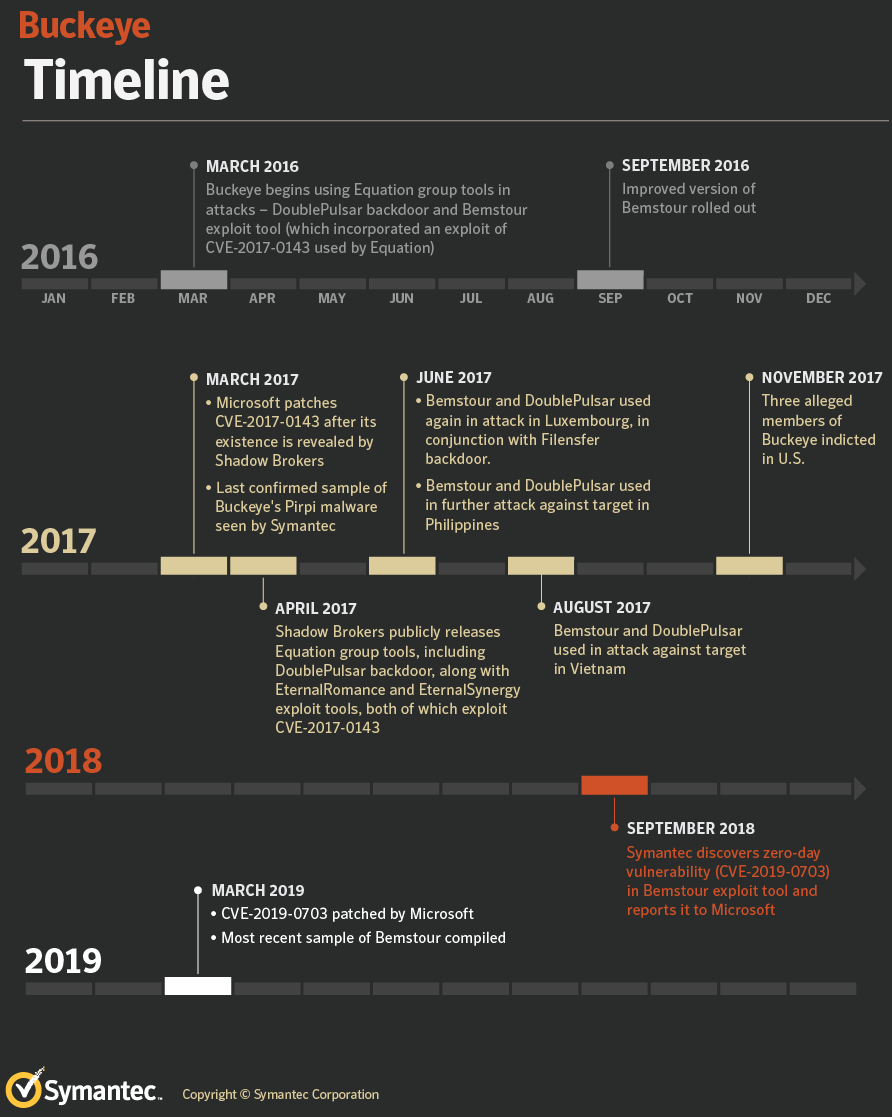
As say Symantec specialists, they managed to find evidence that Buckeye applied DoublePulsar in March 2016. daarom, it is evident that Chinese hackers used NSA tool more than year before its official leakage.
The earliest famous instance of NSA’s espionage tools application was in March 2016, with the attack on aim in Hong Kong. In this attack exploit’s instrument Bemstour was delivered to victims through famous Buckeye malware (Backdoor.Pirpi). An hour later Bemstour was used against educational institution in Belgium.
“Variants of NSA tools used by Buckeye appear to be different from those released by Shadow Brokers, potentially indicating that they didn’t originate from that leak”, — reported in Symantec.
Buckeye disappeared in mid-2017 and three alleged members of the group were indicted in the U.S. in November 2017. Echter, while activity involving known Buckeye tools ceased in mid-2017, the Bemstour exploit tool and the DoublePulsar variant used by Buckeye continued to be used until at least September 2018 in conjunction with different malware.