브랜드 새로운, 매우 유해한 암호 화폐 광부 감염은 보호 연구자들에 의해 발견되었습니다. 악성 코드, 라고 Zcash.exe 방법의 선택을 사용하여 대상 환자를 오염시킬. Zcash.exe 광부의 핵심은 목표 비용으로 Monero 기호를 획득하기 위해 환자의 컴퓨터에서 cryptocurrency 광부 작업을 사용하는 것입니다.. The outcome of this miner is the raised power costs and if you leave it for longer periods of time Zcash.exe may even harm your computer systems parts.
Zcash.exe: 배포 방법
그만큼 Zcash.exe 악성 코드를 사용합니다 2 컴퓨터 시스템 대상을 오염시키는 데 사용되는 널리 사용되는 방법:
- 이전 감염을 통해 페이로드 배달. If an older Zcash.exe malware is released on the target systems it can instantly upgrade itself or download a more recent variation. 이것은에 의해 가능하다 내장 된 릴리스를 얻을 업그레이드 명령. 이것은 악성 코드를 공급하는 특정 미리 정의 된 해커 제어 서버에 연결하여 이루어집니다. The downloaded and install virus will get the name of a Windows solution and also be positioned in the “%시스템 % 온도” 위치. Vital properties and also running system setup documents are altered in order to allow a consistent as well as quiet infection.
- 소프트웨어 취약점 악용. The latest variation of the Zcash.exe malware have actually been found to be triggered by the some exploits, 널리 랜섬웨어 공격에 사용 인정. 감염은 TCP 포트를 통해 공개 서비스를 대상으로 수행됩니다. 공격은 포트가 열려있는 경우 조회 해커 제어 구조에 의해 자동화. If this problem is satisfied it will certainly scan the solution and also obtain information regarding it, consisting of any version and setup data. 선호하는 사용자 이름과 암호 혼합뿐만 아니라 익스플로잇이 수행될 수 있습니다.. When the make use of is set off against the prone code the miner will be released in addition to the backdoor. 이것은 확실히 이중 감염을 선물 할 것이다.
Aside from these approaches other methods can be utilized too. Miners can be distributed by phishing e-mails that are sent wholesale in a SPAM-like fashion as well as depend on social engineering techniques in order to puzzle the targets into believing that they have obtained a message from a reputable solution or firm. The infection documents can be either directly connected or placed in the body components in multimedia material or message links.
The lawbreakers can likewise develop harmful touchdown web pages that can pose supplier download web pages, software program download websites and other frequently accessed locations. When they utilize similar sounding domain names to legitimate addresses and also protection certifications the individuals may be pushed right into connecting with them. 어떤 경우에는 단순히 광부 감염을 활성화 할 수 있습니다를 여는.
An additional approach would be to use haul service providers that can be spread out making use of the above-mentioned approaches or through data sharing networks, 비트 토런트는 가장 인기있는 것들 중 하나 하나에 불과. It is often used to distribute both legitimate software and files and pirate material. 2 가장 눈에 띄는 페이로드 서비스 제공 업체 중 하나의 다음과 같다:
Various other approaches that can be taken into consideration by the lawbreakers include the use of web browser hijackers -unsafe plugins which are made compatible with one of the most popular web internet browsers. They are posted to the relevant databases with fake user testimonials and also designer credentials. 때때로 설명 스크린 샷 구성 될 수 있습니다, video clips and also sophisticated descriptions promising great feature enhancements and also efficiency optimizations. 그러나 설치시 영향을 인터넷 브라우저의 행동은 확실히 변환됩니다- individuals will certainly locate that they will be redirected to a hacker-controlled touchdown page and also their settings may be changed – 기본 홈 페이지, 검색 엔진과 새로운 탭 페이지.

Zcash.exe: 분석
The Zcash.exe malware is a traditional situation of a cryptocurrency miner which depending on its arrangement can cause a wide range of harmful activities. Its main objective is to carry out complicated mathematical tasks that will take advantage of the offered system resources: CPU, GPU, 메모리뿐만 아니라 하드 디스크 공간. The means they function is by connecting to a special web server called mining pool from where the called for code is downloaded. 빨리 작업들로 동시에 시작됩니다 다운로드, 여러 상황이 한 번에 실행할 수 있습니다. When an offered job is completed another one will certainly be downloaded and install in its place as well as the loophole will certainly proceed till the computer system is powered off, 감염 제거 또는 다른 유사한 기회가 발생한다. 암호 화폐 확실히 범죄 컨트롤러에 보상한다 (해킹 팀 또는 하나의 사이버 펑크) 바로 자신의 지갑에.
An unsafe attribute of this classification of malware is that samples such as this one can take all system resources and virtually make the target computer unusable up until the hazard has actually been totally eliminated. A lot of them feature a persistent installation which makes them truly difficult to get rid of. 이 명령은 확실히 옵션도 조정을 할 것입니다, setup data and Windows Registry values that will make the Zcash.exe malware start instantly as soon as the computer system is powered on. Access to recuperation menus and choices may be obstructed which renders numerous manual elimination guides virtually useless.
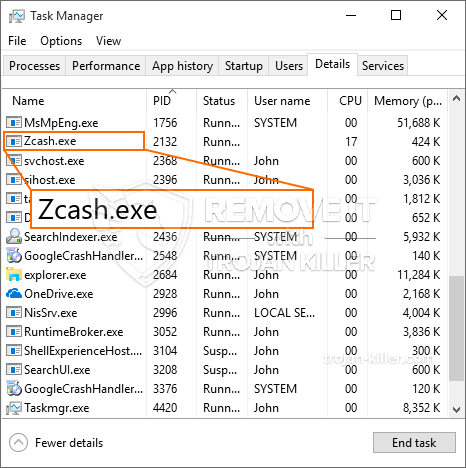
이 특정 감염 자체에 대한 Windows 서비스를 구성합니다, following the carried out security evaluation ther complying with activities have been observed:
. 광부 작업 중에 연결된 맬웨어는 이미 실행 중인 Windows 서비스 및 타사 탑재 응용 프로그램에 연결할 수 있습니다.. By doing so the system managers might not discover that the resource lots originates from a different procedure.
| 이름 | Zcash.exe |
|---|---|
| 범주 | 트로이 사람 |
| 하위 카테고리 | 암호 화폐 광부 |
| 위험 | 높은 CPU 사용, 인터넷 속도 감소, PC 충돌 및 정지 등. |
| 주목적 | 사이버 범죄자 돈을 만들려면 |
| 분포 | 급류, 무료 게임, 금이 앱, 이메일, 의심스러운 웹 사이트, 악용 |
| 제거 | 설치 GridinSoft 안티 멀웨어 to detect and remove Zcash.exe |

이러한 유형의 맬웨어 감염은 설정되어있는 경우 혁신적인 명령을 수행하는 데 특히 효과적입니다.. 그들은 범죄자 컨트롤러가 모든 종류의 유해한 습관을 조정할 수 있도록 모듈 식 구조를 기반으로합니다.. 인기있는 인스턴스 중 윈도우 레지스트리의 조정은 – 운영 체제로 연결된 조정 문자열은 심각한 효율성 장애 및 Windows 솔루션에 액세스 할 수 없음을 유발할 수 있습니다. 변화의 정도에 따라 그것은 또한 컴퓨터 시스템이 완전히 무의미 할 수있다. 다른 한편으로 모든 종류의 타사 설정 응용 프로그램에 속하는 레지스트리 가치를 조작하면 해당 값을 손상시킬 수 있습니다.. 일부 응용 프로그램은 완전히 릴리스하기에는 부족한 반면 다른 응용 프로그램은 모두 갑자기 작동을 멈출 수 있습니다.
기존 변형에서이 특정 광부는 XMRig CPU 마이닝 엔진의 수정 된 버전을 포함하여 Monero 암호 화폐 추출에 중점을 둡니다.. If the campaigns show successful after that future versions of the Zcash.exe can be launched in the future. 악성 코드가 만들어으로 소프트웨어 프로그램의 사용은 대상 호스트를 감염 susceptabilities, 이 랜섬웨어 및 트로이 목마와 안전하지 않은 공동 감염의 일부가 될 수 있습니다.
Elimination of Zcash.exe is highly advised, PC에서 작동하는 경우 막대한 전력 비용뿐만 아니라, 그러나 광부는 마찬가지로 다양한 다른 바람직하지 않은 활동을 수행하고 컴퓨터를 완전히 손상시킬 수 있습니다..
Zcash.exe removal process
단계 1. 가장 먼저, 당신은 GridinSoft 안티 악성 코드를 다운로드하고 설치해야.
단계 2. 그럼 당신은 선택해야 “빠른 검사” 또는 “전체 검사”.
단계 3. 컴퓨터를 스캔 실행
단계 4. 스캔이 완료되면, 당신은 클릭해야 “대다” button to remove Zcash.exe
단계 5. Zcash.exe Removed!
비디오 가이드: How to use GridinSoft Anti-Malware for remove Zcash.exe
방법으로 재감염되는 PC를 방지하기 위해 “Zcash.exe” 앞으로.
탐지하고 차단 fileless 악성 코드 수있는 강력한 안티 바이러스 솔루션은 당신이 필요하다! 기존의 솔루션은 바이러스 정의를 기반으로 악성 코드를 탐지, 따라서 그들은 종종 감지 할 수 없습니다 “Zcash.exe”. GridinSoft 안티 - 악성 코드는 다음과 같은 fileless 악성 코드를 포함한 모든 유형의 맬웨어에 대한 보호를 제공 “Zcash.exe”. GridinSoft 안티 - 악성 코드는 제로 데이 악성 코드를 포함한 모든 알 수없는 파일을 차단하는 클라우드 기반의 행동 분석을 제공합니다. 이러한 기술은 감지하고 완전히 제거 할 수 있습니다 “Zcash.exe”.







