
피델 사이버 보안 전문가들이 1 분기에 해커들 사이에서 가장 인기가 취약점을 연구 2019.
티hough value of vulnerabilities dramatically falls immediately after publication of patches for them, 침입자는 너무 빨리 버그의 착취로부터 거절하지 않는다. 사실로, 해커는 그들의 도움으로 어떤 가치있는 목표를 도달 할 때까지 취약점을 계속 사용.“In addition to staying current with new threat campaigns and techniques, our intelligence team feels it’s also imperative to ensure we don’t lose focus on previously identified and existing threats”, — consider in Fidelis Cybersecurity.
According to Fidelis Cybersecurity report, many of the most actual threats in the first quarterly of 2019 are old, well-known bugs, patches for them arrived few years ago.
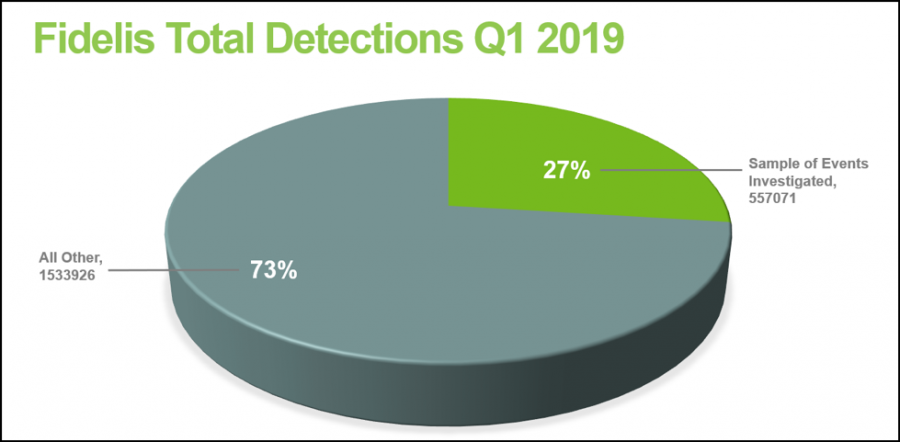
그래서, nearly one third of all detected in the first quarterly problems (악용, 취약점, 악성 코드) date 2017 이전.
예를 들면, the most active malwares were H-W0rm (Houdini) 과 njRAT, two Trojans of remote access (쥐) that exist at least since 2012. 그 위에, experts suggest that developers of these “tools” work together.
또한, analysts accounted that 약 27% of compromise attempts (이상 550 000 investigated incidents) were linked to vulnerabilities, detected in 2017 이전.
“Threat actors and campaigns not only are able to adjust to current trends and update capabilities, but also highlights the continued focus on pre-existing vulnerabilities and recurring tactics to carry out their campaigns and activity”, — emphasize in Fidelis Cybersecurity.
결과, top-5 most popular old issues look like this:
- CVE-2017-8570— RCE bug Composite Moniker, exploit is publicly available;
- CVE-2017-0143– problem that involves SMBv1, exploit is published by ShadowBrokers (Eternal Synergy) 그룹;
- CVE-2018-11776– RCE-vulnerability in Apache Struts, exploit is publicly available;
- CVE-2017-11882— RCE-vulnerability in Microsoft Office, exploit is publicly available;
- CVE-2009-3129– RCE-vulnerability in Microsoft Excel/Word, was used in Red October operation, exploit is publicly available.
