
ESET 전문가는 해커가 5 년 동안 숨기기로 관리하는 Turla 무기고 새로운 강력한 악기에서 발견, 적어도 이후 2014.
비ackdoor named LightNeuron compromises Microsoft mailing servers and functions as mail transfer agent, (MTA) 그와 같은 악성 코드에 대한 일반적이지 않습니다.연구자 노트, 그, 이들 데이터에 따라, LightNeuron 특별히에 지향하는 fisrt 백도어입니다 마이크로소프트 익스체인지. Earlier Turla applied Neuron malware (aka DarkNeuron), that has nothing similar with LightNeuron and was developed with the focus on Microsoft Exchange.
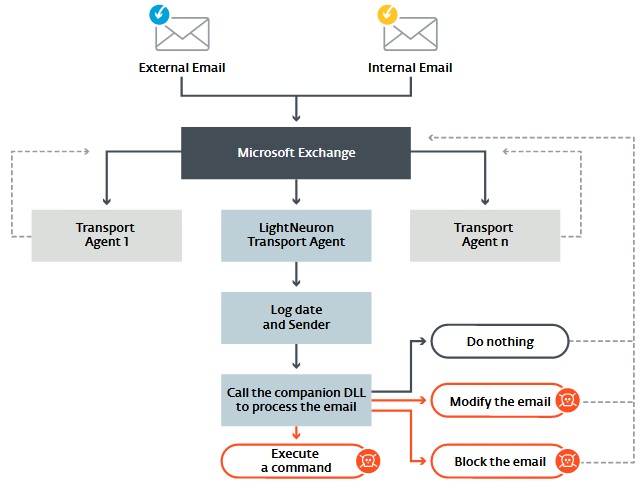
LightNeuron not just allows attackers to trace events on mailing server, but to integrate in its work and control virtually anything.
“In architecture of mailing server, backdoor can work on same level of trust, as security products, as spam filters. 따라서, this malware gives cybercriminals full control over mailing server, 과, by this, on all letters”, – explain ESET specialists.
Hackers can intercept and redirect all mails, edit content of sent and inbox messages or block receiving some mails for users. All these opportunities make LigthNeuron one of the most powerful tools in group’s arsenal.
게다가, backdoor differs as it uses one peculiar 기음&C mechanism. The case is that attackers never connected Microsoft servers directly.
대신, they use steganography and mails with attached PDF and JPG files. Inside these letters hackers from LightNeuron team hide commands for LightnNeuron that malware opens and performs. This way of communication with malware significantly complicates its detection, as commands for backdoor might come with ordinary spam that no one pays attention to and does not trace as filters weed it out.

As reported, LightNeuron is used for attacks until now. ESET experts have already identified three organizations that suffered from it. Analysts not disclose their names, but report that it is some of the Brazilian structures, Ministry of Foreign Affair from Easter Europe and one regional diplomatic organization on the Middle East.
