
Great number of plugins for open instrument of uninterrupted integration by Jenkins software contain different bugs and vulnerabilities.
Vulnerabilities mainly connected with storing of passwords in non-encrypted form. Additionally, in Jenkins’ soft found CSRF-bugs that allow steaking credentials and committing CSRF-attacks.Viktor Gazdag, specialist of NCC Group that tested great number of Jenkins’ plugins, revealed these problems.
“These tests resulted in more than 100 plugins found vulnerable and several coordinated and responsible public disclosures”, — reports researcher.
As expert explained, though Jenkins encrypts passwords in credentials.xml file, some developers use other methods of data storage. In the majority of cases these decisions do not suggest are encryption. Moreover, some web-forms, where users input credentials, enable leakage of passwords or secret tokens.
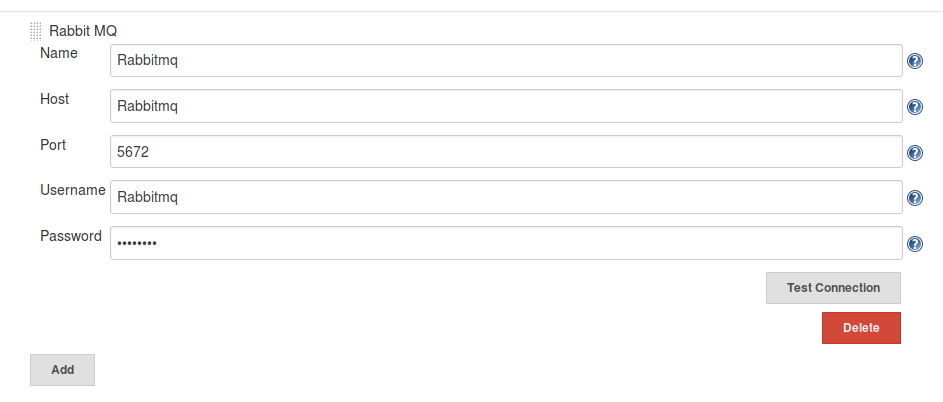
CSRF-vulnerabilities are connected with plugins’ functions, with the use of which users can check credentials and connect to a server. They mostly exist, as developers do not apply POST-requests that prevent attacks with the use of CSRF token.
In the last two years, Jenkins developers released several notifications that describe vulnerabilities in different plugins, including series of bugs, discovered by Gazdag.
Vulnerable plugins interact with a wide circle of services, including Twitter, AWS, VMware and Azure. In most cases software was created by side developers that is not connected to vendor, whose software exploits plugin.
As noted, authors of several plugins have already fixed bugs in their software, though many are still vulnerable. In their turn, Jenkins developers published a vast list of plugins that still are not fixed.
Source: https://www.nccgroup.trust
