Trend Micro experts discovered a new botnet, attacking mobile devices through the open debug ports of the Android Debug Bridge (ADB), as well as using SSH and the list of known_hosts.
Although ADB is disabled by default on most Android devices, some gadgets still sold with enabled ADB (most often on port 5555).“This attack takes advantage of the way open ADB ports don’t have authentication by default”, — report Trend Micro experts.
As a result, unauthenticated attackers are able to remotely connect to a vulnerable device and get access to ADB command shell, which is usually used to install and debug applications.
Recalling, experts have previously found similar botnets Trinity, Fbot and ADB.Miner, which also abused ADB functionality.
Now Trend Micro researchers are writing that the new mobile botnet has already spread to 21 countries around the world, but the majority of affected users are from South Korea.
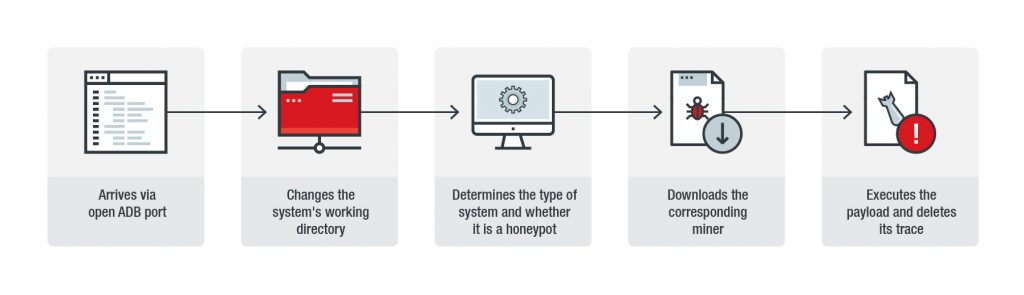
During the first phase of the attack, malware connects to devices on which ADB is available, and changes working directory to data/local/tmp. Next, malware will check if it has got into a controlled environment and whether security experts are studying it. If everything is in order, malware downloads payload using wget or curl.
Payload in this case is one of the three miners, which malware selects based on who is the manufacturer of the system, which architecture is used in it, the type of processor and what hardware. Moreover, in order to optimize the mining activity, the malware also “pumps” the memory of the victim machine, including HugePages.
Worse, the malware has the potential of a worm and spreads via SSH. That is, any system that connected to the original victim system via SSH was likely saved as a “known device”.
“Being a “known device” means that system can communicate with the other system without any further authentication after the initial key exchange, i.e., each system considered to be safe. Presence of a spreading mechanism may mean that this malware can abuse the widely used process of making SSH connections”, – reported in Trend Micro.
Although ADB is a useful feature for administrators and developers, it is important to remember that an enabled ADB might expose the device and those connected to it to threats.
Users can also follow other best practices for defending against illicit cryptocurrency-mining activities and botnets, such as:
- Checking and changing default settings when necessary to increase security
- Updating device firmware and applying available patches
- Being aware of methods attackers use to spread these types of malware and tailoring defenses against them
Source: https://blog.trendmicro.com
