
En mediados de marzo 2019 pirata informático que se conoce como Laboratorio Dookhtengan publicado en herramientas telegrama del grupo APT34 iraní (aka Oilrig y HelixKitten) así como información acerca de los hackers y sus supuestos supervisores del Ministerio de Información y Seguridad Nacional de Irán.
jLos periodistas de ZDNet se comunicaron con Lab Dookhtegan e informan que confirma su participación en la campaña de espionaje de DNS y fue miembro de APT34.. sin embargo, él no proporciona ninguna evidencia y puede ser, de lejos, un miembro del servicio de inteligencia iraní..ZDNet argumenta que muchas empresas de seguridad de Internet están investigando la participación de Lab Dookhtegan. La autenticidad de los códigos proporcionados por él ya lo confirmaron especialistas de Chronicle, que es el departamento de ciberseguridad de Alphabet Holding..
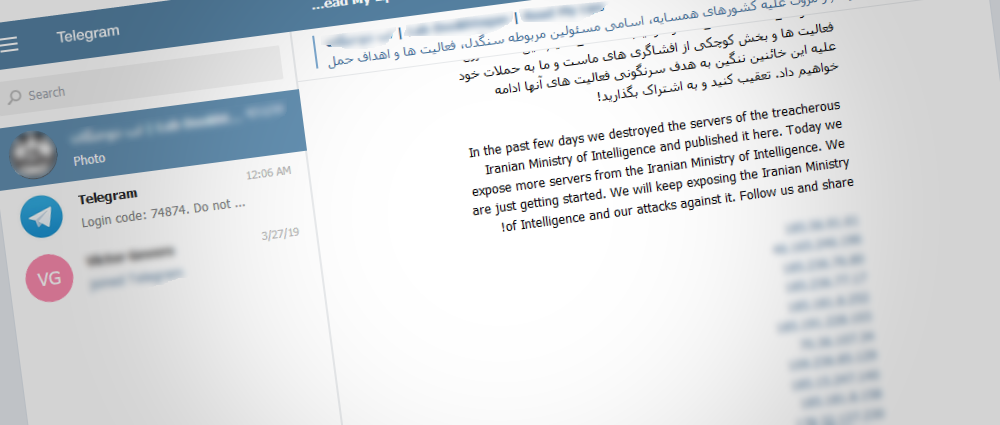
Información de Lab Dookhtegan en el telegrama
Aparte de los códigos iniciales, Lab Dookhtegan también publicó en acceso abierto información sobre 66 Víctimas APT34 que se almacenaron en el servidor de gobierno del grupo. Entre otros datos publicados también se encontraban las credenciales de los servidores internos y las direcciones IP de los usuarios.. Principalmente, esta lista incluye empresas y organizaciones de Oriente Medio., África, Sudeste de Asia y Europa. Las dos compañías más grandes que sufrieron ataques son Etihad Airways y Emirates National Oil..
Lab Dookhtegan también filtró datos sobre la actividad previa de los grupos., incluyendo listas de direcciones IP y dominios donde el grupo vende web alojada y otros datos operativos.
Adicionalmente, el expositor anónimo pasó mucho tiempo engañando a los empleados del Ministerio de Información y Seguridad Nacional iraní que participaron en las operaciones APT34. Para algunos oficiales, Lab Dookhtegan creó carpetas PDF especiales con "expedientes" donde revela sus nombres., posiciones, fotos adjuntas, números de teléfono, correos electrónicos y enlaces de sus perfiles de redes sociales. Los periodistas argumentan que es difícil no notar la postura negativa de Lab Dookhtegan hacia estas personas, ya que en estos dossieres los llama "criminales despiadados"..
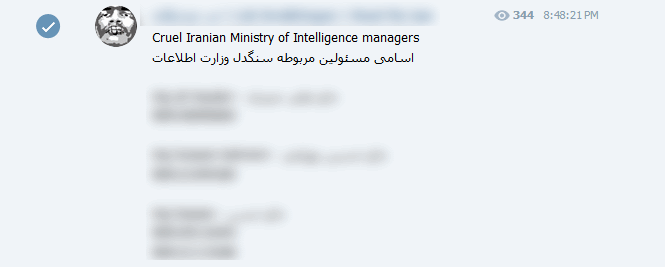
Lista de Lab Dookhtegan
Además de lo mencionado anteriormente, en Telegram se publicaron capturas de pantalla que demuestran la demolición de los paneles de control APT34 y la limpieza completa de los servidores del grupo que supuestamente cometió Lab Dookhtegan.
Los analistas de Chronicle sugieren que ahora APT34 tendrá que cambiar sus instrumentos y tomará tiempo restaurar la preparación para el combate..
Fuente: www.zdnet.com
