Un nuevo, muy perjudicial virus de la minera criptomoneda ha sido identificado por los científicos de seguridad. el software malicioso, llamado Z-enemy.exe puede contaminar víctimas diana usando una gama de métodos. La esencia detrás de la minera Z-enemy.exe es utilizar actividades criptomoneda minero en los ordenadores de las víctimas con el fin de obtener símbolos Monero a un costo objetivos. The end result of this miner is the raised electrical energy costs and if you leave it for longer amount of times Z-enemy.exe may even harm your computer systems components.
Z-enemy.exe: Métodos de distribución de
los Z-enemy.exe utiliza de malware 2 métodos populares que se utilizan para contaminar los objetivos del sistema informático:
- Entrega de carga útil a través de infecciones previas. If an older Z-enemy.exe malware is deployed on the victim systems it can instantly update itself or download a more recent variation. Esto es posible mediante el comando de actualización integrado en el que se pone la liberación. Esto se realiza mediante la conexión a un servidor pirata informático controlado particular predefinida que suministra el código de malware. The downloaded infection will certainly get the name of a Windows solution as well as be put in the “%sistema% temp” zona. Vital buildings as well as operating system setup documents are altered in order to allow a persistent and quiet infection.
- El aprovechamiento de vulnerabilidades de software. The most recent version of the Z-enemy.exe malware have been found to be caused by the some ventures, entiende comúnmente para ser utilizado en las huelgas ransomware. Las infecciones se llevan a cabo por la orientación soluciones abiertas utilizando el puerto TCP. Los asaltos son automatizados por una estructura pirata informático controlado que busca determinar si el puerto está abierto. Si se cumple esta condición, verificará la solución y obtendrá información al respecto., including any version and configuration data. Exploits and prominent username as well as password combinations might be done. When the make use of is activated versus the at risk code the miner will be released in addition to the backdoor. Esto sin duda proporcionará la doble infección.
Aside from these approaches various other techniques can be made use of too. Miners can be distributed by phishing emails that are sent in bulk in a SPAM-like way and depend upon social design tricks in order to confuse the targets right into thinking that they have received a message from a reputable solution or firm. The infection files can be either straight connected or inserted in the body components in multimedia content or message links.
The wrongdoers can additionally develop harmful touchdown pages that can pose vendor download web pages, software program download portals and also various other frequently accessed locations. When they use similar seeming domain names to legitimate addresses and security certificates the users might be pushed into engaging with them. En algunos casos, simplemente abrirlos pueden desencadenar la infección minero.
An additional technique would certainly be to make use of haul providers that can be spread out using the above-mentioned techniques or through documents sharing networks, BitTorrent es uno de los más prominentes. It is regularly utilized to disperse both legitimate software application and files and also pirate content. 2 de los proveedores de acarreo más destacados son los siguientes:
Various other approaches that can be thought about by the crooks include using browser hijackers -dangerous plugins which are made suitable with one of the most preferred web browsers. They are uploaded to the appropriate repositories with phony individual testimonials and also programmer qualifications. En la mayoría de los casos, los resúmenes podrían consistir en imágenes, video clips and also fancy summaries encouraging fantastic function enhancements and also efficiency optimizations. Nevertheless upon installment the behavior of the impacted internet browsers will certainly transform- customers will certainly discover that they will be redirected to a hacker-controlled touchdown page and their setups could be altered – la página web por defecto, motor de búsqueda de Internet y también nuevas pestañas página Web.
Z-enemy.exe: Análisis
The Z-enemy.exe malware is a traditional case of a cryptocurrency miner which depending upon its setup can create a wide variety of dangerous actions. Its major goal is to do complex mathematical jobs that will certainly benefit from the offered system sources: UPC, GPU, memoria y también el espacio del disco duro. The means they function is by connecting to an unique server called mining pool where the required code is downloaded. Tan pronto como uno de los puestos de trabajo se descarga que se pondrá en marcha a la vez, numerosos casos se pueden realizar en cuanto. When a given job is finished another one will be downloaded and install in its location and also the loop will certainly continue up until the computer is powered off, la infección se ha librado de uno o más ocasión similar se lleva a cabo. Criptomoneda sin duda será recompensado a los controladores criminales (un grupo de hackers o cyberpunk solitario) directamente a sus bolsillos.
An unsafe quality of this group of malware is that examples similar to this one can take all system sources and virtually make the victim computer pointless till the hazard has actually been completely removed. A lot of them include a consistent setup which makes them truly tough to remove. Estos comandos harán ajustes para arrancar opciones, setup files and Windows Registry values that will make the Z-enemy.exe malware beginning instantly once the computer system is powered on. Accessibility to recovery menus and also choices may be obstructed which renders lots of manual elimination overviews virtually useless.
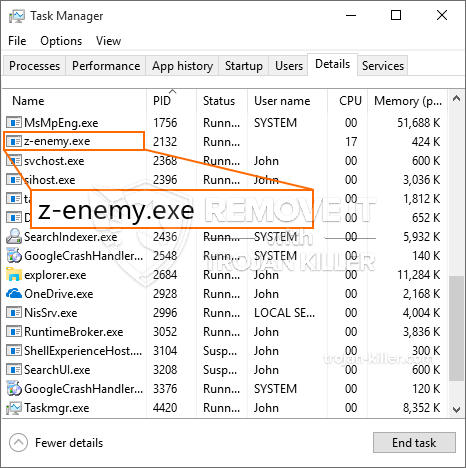
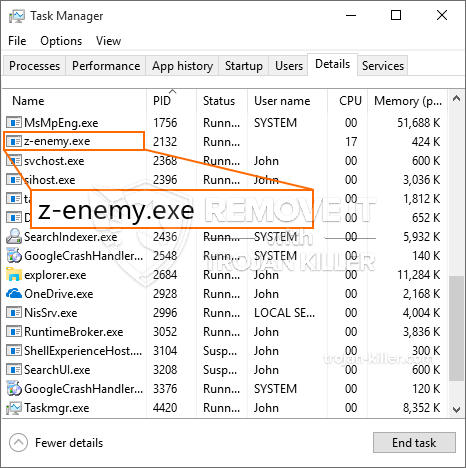
Esta infección particular, será sin duda disposición una solución de Windows por sí mismo, adhering to the conducted safety analysis ther complying with actions have been observed:
During the miner operations the associated malware can connect to currently running Windows solutions and also third-party installed applications. Al hacerlo, es posible que los administradores del sistema no se den cuenta de que la carga de origen se origina en un proceso separado.
| Nombre | Z-enemy.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware para detectar y eliminar Z-enemy.exe |

Este tipo de infecciones de malware son particularmente fiable en el cumplimiento de órdenes innovadoras caso de estar configurada. They are based on a modular structure permitting the criminal controllers to coordinate all sort of hazardous behavior. Entre los casos destacados es la alteración del registro de Windows – adjustments strings connected by the operating system can cause serious performance interruptions and also the lack of ability to gain access to Windows services. Basándose en el alcance de los cambios que, además, puede hacer que el equipo totalmente inutilizable. On the other hand adjustment of Registry worths coming from any type of third-party set up applications can undermine them. Some applications may stop working to launch entirely while others can suddenly stop working.
This particular miner in its current version is focused on mining the Monero cryptocurrency including a customized variation of XMRig CPU mining engine. If the campaigns prove successful then future versions of the Z-enemy.exe can be introduced in the future. A medida que el malware utiliza vulnerabilidades programa de software para contaminar los hosts de destino, que puede ser componente de un co-infección peligrosa con ransomware y troyanos.
Eliminación de la Z-enemy.exe es muy recomendable, because you take the chance of not only a large electrical power costs if it is working on your PC, yet the miner may likewise perform various other unwanted activities on it and also even damage your PC completely.
proceso de eliminación de Z-enemy.exe
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” botón para quitar Z-enemy.exe
PASO 5. Z-enemy.exe Eliminado!
Guía de vídeo: Cómo utilizar GridinSoft anti-malware para quitar Z-enemy.exe
Cómo evitar que su PC de reinfección con “Z-enemy.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “Z-enemy.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “Z-enemy.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “Z-enemy.exe”.







