Un nuevo, extremadamente peligrosos virus de la minera criptomoneda realidad ha sido encontrado por los investigadores de seguridad. el software malicioso, llamado Winime.exe puede infectar a las víctimas de destino que utilizan una variedad de métodos. La esencia detrás de la minera Winime.exe es utilizar tareas criptomoneda minero en los sistemas informáticos de las víctimas con el fin de obtener símbolos Monero a expensas de las víctimas. El resultado de este minero son las facturas de energía eléctrica elevadas y también si lo deja por períodos de tiempo más largos, Winime.exe incluso podría dañar las partes de sus sistemas informáticos..
Winime.exe: Métodos de distribución de
los Winime.exe marcas de malware uso de dos enfoques preferidos que se utilizan para los objetivos del sistema de ordenador Infect:
- Entrega de carga útil a través de infecciones previas. Si se lanza un malware Winime.exe más antiguo en los sistemas de destino, puede actualizarse instantáneamente o descargar una versión más reciente.. Esto es posible mediante el comando de actualización integrado que recibe el lanzamiento. Esto se hace mediante la vinculación a un servidor pirata informático controlado particular predefinida que suministra el código de malware. El virus descargado adquirirá el nombre de una solución de Windows y se coloca en el “%sistema% temp” ubicación. Crucial propiedades residenciales o comerciales y documentos de configuración del sistema operativo se cambian con el fin de permitir que una infección persistente y silencioso.
- El aprovechamiento de vulnerabilidades de software Programa. Se ha descubierto que la última variación del malware Winime.exe ha sido provocada por algunas empresas, ampliamente entendido para ser utilizado en los ataques ransomware. Las infecciones se llevan a cabo por la orientación soluciones abiertas utilizando el puerto TCP. Los asaltos son automatizados por una estructura Hacker-controlada que mira hacia arriba si el puerto está abierto. Si se cumple esta condición sin duda va a escanear el servicio y también recuperar la información sobre ella, que consiste en cualquier tipo de versión y la información de configuración. Exploits y también nombre de usuario preferido, así como mezclas de contraseña que se podría hacer. Cuando el exploit se activa en contra del código propensos al minero sin duda se dará a conocer junto con la puerta trasera. Esto ofrecerá la doble infección.
Aparte de estos métodos otras estrategias pueden utilizarse también. Los mineros se pueden dispersar por correos electrónicos de phishing que se envían a granel en forma de SPAM similares, así como las técnicas de diseño dependerá sociales con el fin de descifrar los enfermos haciéndoles creer que han obtenido un mensaje de una solución o de una empresa legítima. Los datos infección puede ser ya sea directamente unidos o colocados en los materiales del cuerpo en material multimedia o enlaces mensaje web.
Los delincuentes, además, puede producir páginas de destino maliciosos que pueden suponer descargar e instalar páginas proveedor, portales de descarga de software programa y también otros lugares que se accede regularmente. Cuando se utilizan dominio que suena similar a las direcciones de buena reputación y la seguridad y certificados de seguridad de los usuarios pueden ser persuadidos a la derecha en la conexión con ellos. A veces, sólo abrirlos puede desencadenar la infección minero.
Otro enfoque sería hacer uso de los proveedores de servicios de carga útil que se pueden propagar a cabo utilizando aquellas técnicas o por medio de redes de intercambio de datos, BitTorrent es una de las más preferidas. A menudo se utiliza para dispersar tanto de software legítimo y también archivos, así como el contenido web pirata. 2 de los proveedores de servicios de acarreo más preferidos son los siguientes:
Varios otros enfoques que se pueden tomar en consideración por los criminales incluyen el uso de secuestradores de navegador plugins -harmful que se hacen compatible con una de las mayoría de los navegadores de Internet prominentes. Se publican las bases de datos pertinentes con falsas evaluaciones individuales, así como las calificaciones de desarrolladores. En la mayoría de los casos, los resúmenes pueden incluir capturas de pantalla, vídeos, así como resúmenes sofisticados atractivos grandes mejoras de funciones y optimizaciones de rendimiento. Sin embargo durante la configuración de las acciones de los navegadores afectados alterarán- los usuarios no van a encontrar que sin duda serán desviados a una página de touchdown pirata informático controlado y sus configuraciones pueden ser modificados – la página web por defecto, motor de búsqueda en Internet y la página de pestañas nuevo.

Winime.exe: Análisis
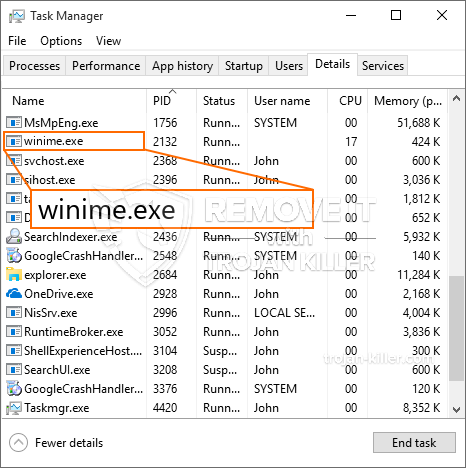
El software malicioso Winime.exe es una situación tradicional de un minero criptomoneda el que basándose en su disposición puede desencadenar una amplia variedad de actividades perjudiciales. Su principal objetivo es ejecutar tareas matemáticas complejas que sin duda aprovechar los recursos del sistema disponibles: UPC, GPU, la memoria y el área del disco duro. Los medios que trabajan es mediante la unión a un servidor llamado piscina minera especial donde se descarga el código necesario. Tan rápidamente como uno de los puestos de trabajo se descarga sin duda va a ser encendido al mismo tiempo, varios casos se puede ir por una vez. Cuando una tarea siempre se ha completado otra se descargará e instalar en su lugar, así como continuará la laguna hasta que el ordenador esté apagado, la infección se elimina o se produce un ocasión similar adicional. Criptomoneda ciertamente será compensado a los controladores criminales (piratería equipo o un solo pirata informático) directamente a sus bolsillos.
Una característica nociva de éste grupo de malware es que los ejemplos similares a éste puede tomar todos los recursos del sistema y también prácticamente inútil hacer que el ordenador de la víctima hasta que el riesgo ha sido totalmente librado de. La mayoría de ellos incluyen una serie persistente que los hace verdaderamente difícil de eliminar. Estos comandos harán modificaciones para arrancar opciones, los datos de disposición y también los valores del Registro de Windows que harán que el software malicioso Winime.exe comienzan instantáneamente cuando el ordenador está encendido. Accesibilidad a la curación de las selecciones de alimentos y alternativas puede ser bloqueada que hace que muchas guías de eliminación manual de casi inútil.
Esta infección particular, será sin duda una solución de configuración de Windows por sí mismo, cumplir con la evaluación de seguridad llevado a cabo allí la adhesión a las actividades se han observado:
. Durante las operaciones mineras, el malware conectado puede conectarse a los servicios de Windows que se ejecutan actualmente, así como a aplicaciones de configuración de terceros. Al hacerlo, los administradores del sistema pueden no ver que los lotes de origen provienen de un proceso separado.
| Nombre | Winime.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware para detectar y eliminar Winime.exe |

Este tipo de infecciones de malware son particularmente eficaces en la realización de comandos innovadoras caso de estar configurada. Se basan en una estructura modular que permite a los controladores criminales para orquestar todo tipo de acciones peligrosas. Entre los ejemplos populares es la modificación del registro de Windows – modificaciones cadenas asociadas por el sistema operativo pueden causar interrupciones importantes de rendimiento y la falta de acceso a soluciones de Windows. Dependiendo de la magnitud del movimiento también puede hacer que el sistema informático totalmente inutilizable. En los demás ajustes mano de los valores del registro que pertenece a ningún tercero configurar aplicaciones pueden sabotear ellas. Algunas aplicaciones pueden dejar de introducir por completo, mientras que otros pueden, de repente dejó de funcionar.
Este minero específico en su variación de corriente se concentra en la extracción de la criptomoneda Monero que contiene una variación cambiado de motor minería XMRig CPU. Si los proyectos tienen éxito, entonces las variaciones futuras de la Winime.exe pueden ser lanzados en el futuro. A medida que el malware utiliza vulnerabilidades de las aplicaciones de software para contaminar los hosts de destino, que puede ser parte de una co-infección peligrosa con ransomware y troyanos.
Se recomienda encarecidamente eliminación de Winime.exe, teniendo en cuenta que se corre el riesgo de no sólo un gran gasto de energía eléctrica si se está ejecutando en su ordenador, sin embargo, el minero podría asimismo hacer otras actividades no deseadas en él y también dañar el ordenador de forma permanente.
Proceso de eliminación de Winime.exe
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” botón para eliminar Winime.exe
PASO 5. Winime.exe eliminado!
Guía de vídeo: Cómo utilizar GridinSoft Anti-Malware para eliminar Winime.exe
Cómo evitar que su PC de reinfección con “Winime.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “Winime.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “Winime.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “Winime.exe”.







