Un nuevo, extremadamente infección minero criptomoneda peligrosos ha sido descubierto por los científicos de seguridad. el software malicioso, llamado Pulse Extinguish.exe puede infectar a las víctimas de destino que utilizan una variedad de formas. La idea principal detrás del pulso Extinguish.exe minero es utilizar actividades criptomoneda minero en los sistemas informáticos de los enfermos con el fin de adquirir Monero fichas a expensas de las víctimas. The end result of this miner is the elevated electrical power costs and if you leave it for longer time periods Pulse Extinguish.exe may even damage your computers elements.
Pulse Extinguish.exe: Métodos de distribución de
los Pulse Extinguish.exe malware se hace uso de 2 enfoques prominentes que se hacen uso de infectar a los objetivos del sistema informático:
- Entrega de carga útil usando infecciones previas. If an older Pulse Extinguish.exe malware is released on the victim systems it can immediately update itself or download a newer version. Esto es factible mediante el comando integrado de actualización que adquiere el lanzamiento. Esto se realiza mediante la conexión a un determinado servidor web predefinido pirata informático controlado que suministra el código de malware. El virus descargado e instalado obtendrá el nombre de una solución de Windows y se colocará en el “%sistema% temp” zona. Essential residential or commercial properties and also operating system configuration data are changed in order to allow a relentless and also silent infection.
- El aprovechamiento de vulnerabilidades de software. The most recent version of the Pulse Extinguish.exe malware have actually been found to be caused by the some ventures, comúnmente conocido por ser utilizado en los ataques ransomware. Las infecciones se llevan a cabo por la orientación soluciones abiertas por medio del puerto TCP. Los asaltos son automatizados por un marco Hacker-controlada que mira hacia arriba si el puerto está abierto. If this condition is met it will certainly check the solution and retrieve details about it, including any version and arrangement information. Se pueden realizar exploits y también combinaciones preferidas de nombre de usuario y contraseña.. When the manipulate is set off against the prone code the miner will certainly be deployed along with the backdoor. Esto proporcionará la doble infección.
Besides these approaches other techniques can be made use of as well. Miners can be distributed by phishing emails that are sent wholesale in a SPAM-like way as well as rely on social design tricks in order to confuse the sufferers into thinking that they have actually gotten a message from a genuine service or firm. The infection documents can be either directly attached or inserted in the body materials in multimedia material or message web links.
The wrongdoers can additionally produce destructive landing web pages that can impersonate vendor download and install web pages, software download portals and also other often accessed places. When they make use of similar seeming domain names to genuine addresses as well as safety and security certificates the customers may be coerced right into interacting with them. En muchos casos simplemente abrirlos puede activar la infección minero.
An additional strategy would certainly be to use haul providers that can be spread using the above-mentioned approaches or through file sharing networks, BitTorrent es uno de uno de los más populares. It is regularly used to disperse both legitimate software application and data as well as pirate content. 2 de uno de los proveedores de acarreo más preferidos son los siguientes:
Other methods that can be taken into consideration by the bad guys consist of making use of web browser hijackers -hazardous plugins which are made compatible with one of the most prominent web internet browsers. They are submitted to the pertinent databases with fake customer reviews and programmer credentials. En muchos casos, las descripciones podrían incluir capturas de pantalla, video clips as well as intricate descriptions appealing fantastic attribute enhancements as well as efficiency optimizations. No obstante, tras la instalación, los hábitos de los navegadores afectados cambiarán.- los usuarios encontrarán que serán redirigidos a una página web de destino controlada por piratas informáticos y también se puede modificar su configuración – la página de inicio por defecto, motor de búsqueda en Internet y la nueva página de pestañas.

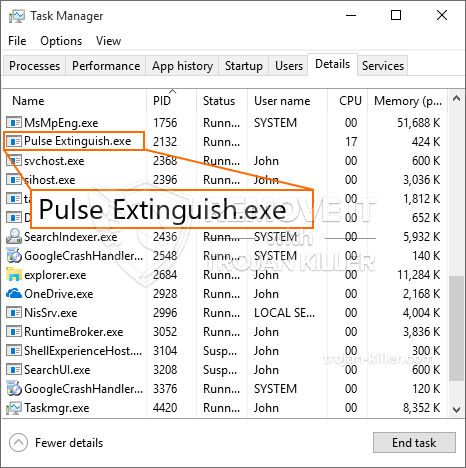
Pulse Extinguish.exe: Análisis
The Pulse Extinguish.exe malware is a timeless instance of a cryptocurrency miner which depending on its arrangement can trigger a wide variety of hazardous actions. Su objetivo principal es realizar trabajos matemáticos complejos que aprovechen las fuentes del sistema disponibles.: UPC, GPU, la memoria y también espacio en disco duro. La forma en que funcionan es mediante la conexión a un servidor especial llamado piscina minera donde se descarga el código necesario. Tan pronto como uno de los trabajos que se descarga se comenzará simultáneamente, varias circunstancias pueden llevar a cabo a la vez. Cuando se complete un trabajo proporcionado, se descargará e instalará uno adicional en su área y también el bucle continuará hasta que se apague la computadora, la infección se elimina o una ocasión comparables adicional se lleva a cabo. Criptomoneda será recompensado a los controladores criminales (piratería equipo o de un hacker solitario) directamente a sus bolsillos.
Un atributo inseguro de esta clasificación de malware es que ejemplos similares a este pueden tomar todos los recursos del sistema y casi hacer que el sistema informático objetivo sea inútil hasta que el peligro se haya eliminado por completo. La mayoría de ellos incluyen una instalación consistente que los hace realmente difíciles de eliminar.. Estos comandos sin duda hará ajustes a las opciones de arranque, configuration files and Windows Registry values that will make the Pulse Extinguish.exe malware beginning immediately as soon as the computer system is powered on. La accesibilidad a las selecciones de alimentos de recuperación y también las opciones pueden bloquearse, lo que hace que muchas descripciones de extracción manual sean casi inútiles.
Esta infección específica será sin duda disposición un servicio de Windows por sí mismo, Después de la evaluación de seguridad y protección realizada, se ha observado el cumplimiento de las actividades.:
. Durante las operaciones del minero, el malware vinculado puede conectarse a las soluciones de Windows que se ejecutan actualmente y a las aplicaciones montadas de terceros.. Al hacerlo, los administradores del sistema pueden no observar que las toneladas de origen provienen de un procedimiento separado.
| Nombre | Pulse Extinguish.exe |
|---|---|
| Categoría | Trojan |
| Subcategoría | criptomoneda Miner |
| peligros | alto uso de CPU, reducción de la velocidad de Internet, PC se bloquea y se congela y etc.. |
| Propósito principal | Para ganar dinero para los criminales cibernéticos |
| Distribución | torrentes, Juegos gratuitos, Aplicaciones Cracked, Email, los sitios web cuestionables, exploits |
| Eliminación | Instalar GridinSoft Anti-Malware to detect and remove Pulse Extinguish.exe |

These type of malware infections are specifically effective at performing advanced commands if configured so. Se basan en un marco modular que permite a los controladores criminales coordinar todo tipo de acciones peligrosas.. Uno de los ejemplos populares es el ajuste del registro de Windows – alterations strings associated by the operating system can create serious performance interruptions and also the failure to gain access to Windows services. Depending upon the range of modifications it can additionally make the computer totally unusable. On the other hand adjustment of Registry worths coming from any kind of third-party set up applications can undermine them. Some applications might stop working to launch completely while others can suddenly quit working.
This certain miner in its current variation is focused on mining the Monero cryptocurrency containing a changed version of XMRig CPU mining engine. If the campaigns show successful after that future versions of the Pulse Extinguish.exe can be released in the future. A medida que el malware utiliza vulnerabilidades de las aplicaciones de software para contaminar los hosts de destino, puede ser componente de una coinfección con ransomware perjudiciales, así como troyanos.
Elimination of Pulse Extinguish.exe is strongly advised, because you take the chance of not only a huge power costs if it is running on your PC, yet the miner might additionally perform various other undesirable activities on it and even harm your PC permanently.
Pulse Extinguish.exe removal process
PASO 1. Ante todo, es necesario descargar e instalar GridinSoft Anti-Malware.
PASO 2. Entonces usted debe elegir “Análisis rápido” o “Análisis completo”.
PASO 3. Corre a escanear su ordenador
PASO 4. Después de terminar el análisis, es necesario hacer clic en “Aplicar” button to remove Pulse Extinguish.exe
PASO 5. Pulse Extinguish.exe Removed!
Guía de vídeo: How to use GridinSoft Anti-Malware for remove Pulse Extinguish.exe
Cómo evitar que su PC de reinfección con “Pulse Extinguish.exe” en el futuro.
Una potente solución antivirus capaz de detectar el malware y el bloque sin archivo es lo que necesita! Las soluciones tradicionales de detectar malware basado en las definiciones de virus, y por lo tanto a menudo no pueden detectar “Pulse Extinguish.exe”. GridinSoft Anti-Malware ofrece protección contra todo tipo de malware incluyendo malware sin archivo como “Pulse Extinguish.exe”. GridinSoft Anti-Malware ofrece analizador de comportamiento basado en la nube para bloquear todos los archivos desconocidos, incluyendo malware de día cero. Dicha tecnología puede detectar y eliminar por completo “Pulse Extinguish.exe”.







