
Mitte März 2019 Hacker, bekannt als Lab Dookhtengan, veröffentlicht in Telegramm-Tools der iranischen APT34-Gruppe (aka Oilrig und HelixKitten) sowie Informationen über Hacker und ihre mutmaßlichen Vorgesetzten vom iranischen Ministerium für Information und nationale Sicherheit.
J.Unsere ZDNet-Analysten kommunizierten mit Lab Dookhtegan und berichteten, dass er die Teilnahme an der DNSpionage-Kampagne bestätigt und Mitglied von APT34 war. jedoch, Er liefert keine Beweise und kann bei weitem kein iranischer Geheimdienstler sein.ZDNet argumentiert, dass viele Internet-Sicherheitsunternehmen die Beteiligung von Lab Dookhtegan untersuchen. Die Echtheit der von ihm bereitgestellten Codes hat bereits Spezialisten von Chronicle bestätigt, der Abteilung für Cybersicherheit der Alphabet Holding.
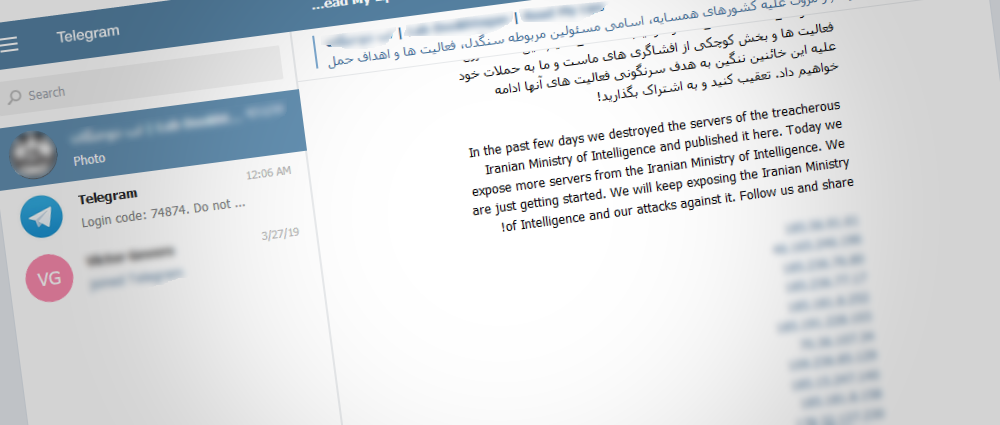
Informationen von Lab Dookhtegan im Telegramm
Abgesehen von den anfänglichen Codes, Lab Dookhtegan veröffentlichte auch in Open-Access-Informationen über 66 APT34-Opfer, die auf dem Server der Gruppe gespeichert wurden. Zu den veröffentlichten Daten gehörten auch Anmeldeinformationen für interne Server und die IP-Adressen der Benutzer. Diese Liste umfasst hauptsächlich Unternehmen und Organisationen aus dem Nahen Osten, Afrika, Südostasien und Europa. Zwei der größten Unternehmen, die unter Angriffen gelitten haben, sind Etihad Airways und Emirates National Oil.
Lab Dookhtegan hat auch Daten über frühere Aktivitäten der Gruppe veröffentlicht, einschließlich Listen von IP-Adressen und Domänen, in denen von Gruppen gehostete Web-Sells und andere Betriebsdaten verkauft werden.
In Ergänzung, Anonymer Exposer verbrachte viel Zeit damit, Mitarbeiter des iranischen Informationsministeriums und der nationalen Sicherheit, die an APT34-Operationen teilgenommen hatten, zu doxen. Für einige Beamte erstellte Lab Dookhtegan spezielle PDF-Ordner mit „Dossiers“, in denen er ihre Namen preisgibt, Positionen, angehängte Bilder, Telefonnummern, E-Mails und Links ihrer Social-Media-Profile. Journalisten argumentieren, dass es schwierig ist, Lab Dookhtegans negative Haltung gegenüber diesen Menschen nicht zu bemerken, da er sie in diesen Dossiers "gnadenlose Kriminelle" nennt..
Lab Dookhtegan Liste
Neben den oben genannten, In Telegram wurden Screenshots veröffentlicht, die den Abriss von APT34-Bedienfeldern und die vollständige Reinigung der Server der Gruppe zeigen, die angeblich von Lab Dookhtegan begangen wurden.
Chronik-Analysten schlagen vor, dass APT34 jetzt ihre Instrumente wechseln muss und es einige Zeit dauern wird, bis die Kampfbereitschaft wiederhergestellt ist.
Quelle: www.zdnet.com
