Ein neuer, sehr unsichere Kryptowährung Bergmann-Infektion wird von Sicherheitsexperten identifiziert tatsächlich worden. die Malware, namens Worker.exe Eine Auswahl an Methoden Ziel Opfer infizieren mit. Die Hauptidee hinter dem Worker.exe-Miner besteht darin, Cryptocurrency-Miner-Aufgaben auf den Computern der Opfer einzusetzen, um Monero-Token zu Zielkosten zu erhalten. Das Ergebnis dieses Bergmanns sind die erhöhten Stromkosten sowie die Tatsache, dass Worker.exe die Komponenten Ihres Computersystems beschädigen kann, wenn Sie es für längere Zeit verlassen.
Worker.exe: Verteilungsmethoden
Das Worker.exe Malware-Anwendungen 2 prominente Techniken, die verwendet werden, um Computersystemziele zu infizieren:
- Payload Lieferung durch Vor-Infektionen. Wenn eine ältere Worker.exe-Malware auf den Zielsystemen veröffentlicht wird, kann sie sich automatisch aktualisieren oder eine neuere Version herunterladen und installieren. Dies ist über den integrierten Update-Befehl möglich, der den Start erhält. Dies wird durch das Anbringen an einen bestimmten vordefinierten Hacker gesteuerten Webserver durchgeführt, die den Malware-Code liefern. Der heruntergeladene Virus erhält sicherlich den Namen einer Windows-Lösung und wird in die “%System% temp” Bereich. Wichtige Dokumente zu Haushalten und laufenden Systemanordnungen werden transformiert, um eine unerbittliche und leise Infektion zu ermöglichen.
- Software Application Vulnerability Exploits. Es wurde tatsächlich festgestellt, dass die neueste Variante der Worker.exe-Malware von einigen Unternehmen eingeführt wurde, weithin bekannt für die Verwendung bei Ransomware-Angriffen. Die Infektionen werden durch Targeting offene Lösungen mit Hilfe des TCP-Port erfolgen. Die Streiks werden von einem Hacker-kontrollierten Rahmen automatisiert die darauf abzielt, ob der Port offen ist. Wenn dieses Problem behoben ist, wird der Dienst gescannt und Informationen dazu abgerufen, Bestehend aus jeder Art von Variation und auch Setup-Daten. Exploits und auch bevorzugt, Benutzername und Passwort Mixes getan werden könnte. Wenn die Manipulation gegen den anfälligen Code aktiviert wird, der Bergmann wird neben der Hintertür freigegeben werden. Diese präsentiert sicherlich die eine Doppelinfektion.
Zusätzlich zu diesen können verschiedene andere Strategien Ansätze werden genutzt. Bergleute können durch Phishing-E-Mails verteilt werden, die SPAM-artig im Großhandel versendet werden, und sich auf Social-Engineering-Methoden verlassen, um die Ziele zu verwirren und zu glauben, dass sie tatsächlich eine Nachricht von einem echten Dienst oder Unternehmen erhalten haben. Die Infektionsdaten können entweder direkt verbunden oder in Multimedia-Inhalten oder Text-Weblinks in den Körperkomponenten platziert werden.
Die Kriminellen können ebenfalls zerstörerische Touchdown-Webseiten entwickeln, auf denen Lieferanten Seiten herunterladen und installieren können, Software-Download-Sites und verschiedene andere Bereiche, auf die regelmäßig zugegriffen wird. Wenn sie eine vergleichbar klingende Domäne mit seriösen Adressen und auch Sicherheitszertifizierungen verwenden, können die Benutzer gezwungen werden, direkt mit ihnen zu kommunizieren. Manchmal nur sie öffnen kann die Bergmann-Infektion auslösen.
Ein zusätzlicher Ansatz wäre die Verwendung von Nutzlastträgern, die unter Verwendung der oben genannten Verfahren oder mittels Datenaustauschnetzwerken verteilt werden können, BitTorrent ist nur eine der beliebtesten. Es wird häufig verwendet, um sowohl seriöses Softwareprogramm und Dateien als auch Pirateninhalte zu verbreiten. Zwei von einem der am meisten bevorzugten Streckendienstanbieter sind folgende:
Andere Techniken, über die die Gauner nachdenken können, sind die Verwendung von Webbrowser-Hijackern - unsicheren Plugins, die mit einem der bekanntesten Web-Internetbrowser kompatibel gemacht werden. Sie werden in den relevanten Datenbanken mit falschen Benutzerbewertungen und Programmiereranmeldeinformationen veröffentlicht. Oft können die Zusammenfassungen enthalten Screenshots, Videos und komplizierte Zusammenfassungen, die wunderbare Attributverbesserungen sowie Leistungsoptimierungen versprechen. Nach der Ratenzahlung wird sich das Verhalten der betroffenen Webbrowser jedoch sicherlich ändern- Benutzer werden feststellen, dass sie mit Sicherheit zu einer von Hackern gesteuerten Touchdown-Seite weitergeleitet werden und dass auch ihre Einstellungen geändert werden können – die Standard-Webseite, Suchmaschine sowie brandneue Registerkarten Seite.

Worker.exe: Analyse
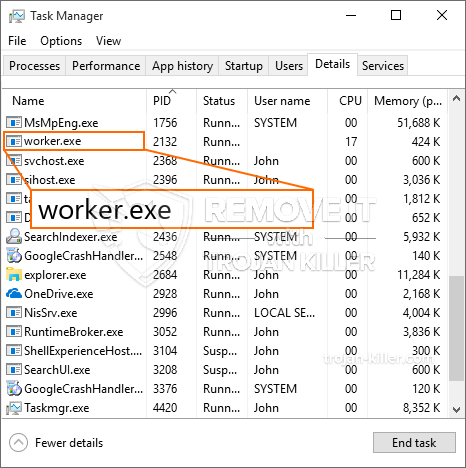
Die Malware Worker.exe ist eine zeitlose Instanz eines Cryptocurrency Miner, die je nach Konfiguration eine Vielzahl unsicherer Aktionen auslösen kann. Das Hauptziel besteht darin, komplexe mathematische Aufgaben auszuführen, die sicherlich von den leicht verfügbaren Systemressourcen profitieren: Zentralprozessor, GPU, Speicher und auch Festplattenspeicher. Sie arbeiten mit einer Verbindung zu einem einzigartigen Webserver namens Mining Swimming Pool, von dem der angeforderte Code heruntergeladen und installiert wird. Sobald bei den Arbeitsplätzen heruntergeladen wird es sicherlich gleichzeitig gestartet werden, mehrere Instanzen durchgeführt werden an, wenn. Wenn ein bestimmter Auftrag abgeschlossen ist, wird sicherlich ein anderer heruntergeladen und an seinem Speicherort installiert, und die Lücke wird fortgesetzt, bis der Computer ausgeschaltet wird, Die Infektion wird beseitigt oder ein weiteres ähnliches Ereignis tritt ein. Kryptowährung werden zu den kriminellen Controller kompensiert werden (Hacker-Team oder eine einzelne cyber) gerade auf ihren Geldbeutel.
Eine gefährliche Eigenschaft dieser Klassifizierung von Malware besteht darin, dass ähnliche Beispiele alle Systemressourcen beanspruchen und den Computer des Opfers praktisch unbrauchbar machen können, bis die Gefahr tatsächlich vollständig beseitigt ist. Die meisten von ihnen enthalten eine konsistente Rate, die es wirklich schwierig macht, sie zu eliminieren. Diese Befehle werden sicherlich Anpassungen auch Optionen machen, Arrangement-Dateien und Windows-Registrierungswerte, mit denen die Malware Worker.exe mit Sicherheit sofort gestartet wird, sobald der Computer eingeschaltet wird. Der Zugang zur Auswahl und Auswahl von Wiederherstellungsnahrungsmitteln kann behindert sein, was mehrere praktische Eliminierungsanleitungen praktisch wertlos macht.
Diese besondere Infektion wird sicherlich Anordnung ein Windows-Dienst für sich, Nach der durchgeführten Sicherheitsbewertung wurden tatsächlich die Einhaltung der Maßnahmen beobachtet:
. Während des Miner-Vorgangs kann die verknüpfte Malware eine Verbindung zu aktuell ausgeführten Windows-Lösungen sowie zu Einrichtungsanwendungen von Drittanbietern herstellen. Auf diese Weise stellen die Systemmanager möglicherweise nicht fest, dass die Ressourcenlose aus einem anderen Prozess stammen.
| Name | Worker.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware um Worker.exe zu erkennen und zu entfernen |

Diese Art von Malware-Infektionen ist besonders effizient bei der Ausführung anspruchsvoller Befehle, wenn sie so eingerichtet sind. Sie basieren auf einem modularen Aufbau, der es den kriminellen Kontrolleuren ermöglicht, alle Arten von schädlichen Gewohnheiten zu koordinieren. Eines der beliebtesten Beispiele ist die Modifikation der Windows-Registrierung – Durch das Betriebssystem verbundene Änderungszeichenfolgen können zu erheblichen Leistungsstörungen führen und auch dazu, dass kein Zugriff auf Windows-Dienste möglich ist. Je nach Änderungsumfang kann der Computer dadurch zusätzlich völlig sinnlos werden. Andererseits kann eine Anpassung der Registrierungswerte, die zu von Drittanbietern bereitgestellten Anwendungen gehören, diese untergraben. Einige Anwendungen funktionieren möglicherweise nicht mehr vollständig, während andere plötzlich nicht mehr funktionieren.
Dieser bestimmte Miner in seiner vorhandenen Variante konzentriert sich auf das Mining der Monero-Kryptowährung mit einer angepassten Variante der XMRig-CPU-Mining-Engine. Wenn sich die Projekte danach als erfolgreich erweisen, können zukünftige Versionen von Worker.exe in Zukunft veröffentlicht werden. Da die Malware nutzt Software-Schwachstellen Ziel-Hosts zu infizieren, es kann Teil eines gefährlichen Koinfektion mit Ransomware und Trojanern auch.
Die Beseitigung von Worker.exe wird dringend empfohlen, da Sie die Chance nutzen, nicht nur eine große Stromrechnung zu erstellen, wenn diese auf Ihrem COMPUTER funktioniert, Der Bergmann kann jedoch auch andere unerwünschte Aktivitäten ausführen und sogar Ihren COMPUTER vollständig beschädigen.
Worker.exe-Entfernungsprozess
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” Schaltfläche zum Entfernen von Worker.exe
SCHRITT 5. Worker.exe entfernt!
Video Guide: Verwendung von GridinSoft Anti-Malware zum Entfernen von Worker.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Worker.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Worker.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Worker.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Worker.exe”.







