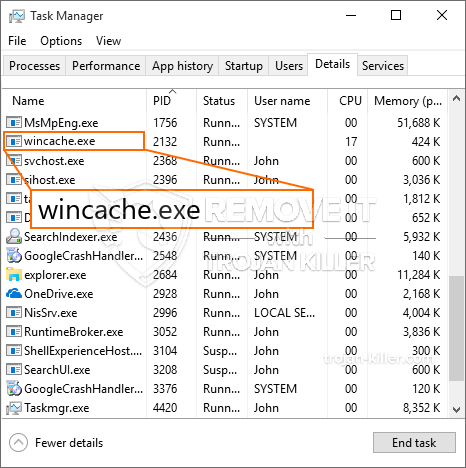
Ein neuer, sehr unsichere Kryptowährung miner Infektion wurde von Sicherheits Wissenschaftler entdeckt tatsächlich worden. die Malware, namens Wincache.exe können Ziel Erkrankten infizieren eine Auswahl an Verfahren unter Verwendung von. Das Wesentliche hinter dem Wincache.exe-Miner ist die Verwendung von Cryptocurrency-Miner-Aufgaben auf den Computern von Betroffenen, um Monero-Symbole auf Kosten der Opfer zu erwerben. Das Ergebnis dieses Miners sind erhöhte Stromrechnungen und wenn Sie es für längere Zeit verlassen, kann Wincache.exe sogar Ihre Computersystemkomponenten beschädigen.
Wincache.exe: Verteilungsmethoden
Das Wincache.exe Malware nutzt 2 prominente Techniken, die verwendet werden, um Computersystemziele zu kontaminieren:
- Payload Lieferung mit Vor-Infektionen. Wenn eine ältere Wincache.exe-Malware auf den betroffenen Systemen veröffentlicht wird, kann sie sich sofort selbst aktualisieren oder eine neuere Version herunterladen und installieren. Dies ist möglich durch den integrierten Erweiterungsbefehl, der den Start bekommt. Dies erfolgt durch Herstellen einer Verbindung zu einem bestimmten vordefinierten, von Hackern kontrollierten Server, der den Malware-Code bereitstellt. Der heruntergeladene Virus erhält den Namen einer Windows-Lösung und wird in die “%System% temp” Bereich. Wichtige Gebäude sowie laufende Systemanordnungsdateien werden geändert, um eine konsistente und leise Infektion zu ermöglichen.
- Software Ausnutzen von Sicherheitslücken. Es wurde tatsächlich entdeckt, dass die neueste Variante der Wincache.exe-Malware von einigen Unternehmungen ausgelöst wird, allgemein verstanden wird, die in den Ransomware Streiks verwendet wird. Die Infektionen werden durch Targeting offene Lösungen über den TCP-Port erfolgen. Die Streiks werden von einem Hacker gesteuerte Struktur automatisiert die oben schaut, ob der Port offen ist. Wenn dieses Problem auftritt, wird es mit Sicherheit die Lösung überprüfen und auch Informationen dazu erhalten, die aus jeder Art von Variation und auch Anordnungsdaten. Es können Unternehmungen und auch prominente Benutzernamen- und Passwortmischungen durchgeführt werden. Wenn der Exploit gegen den anfälligen Code verursacht wird, wird der Miner sicherlich zusätzlich zur Hintertür freigegeben. Dies bietet sicherlich die eine doppelte Infektion.
Abgesehen von diesen Methoden können andere Strategien erfolgen Verwendung auch. Bergleute können durch Phishing-E-Mails zerstreut werden, die in Spam-Form in großen Mengen versendet werden und auch von Tricks des sozialen Designs abhängen, um die Betroffenen zu der Annahme zu verwirren, dass sie eine Nachricht von einer legitimen Lösung oder einem Unternehmen erhalten haben. Die Infektionsdaten können entweder direkt verbunden oder in Multimedia-Material oder Text-Weblinks in die Körperkomponenten eingefügt werden.
Die Täter können ebenfalls böswillige Landing-Webseiten erstellen, die sich als Download- und Installationswebseiten von Anbietern ausgeben können, Download-Portale für Softwareanwendungen und andere Bereiche, auf die regelmäßig zugegriffen wird. Wenn sie vergleichbar erscheinende Domainnamen mit legitimen Adressen sowie Sicherheitszertifikaten verwenden, werden die Benutzer möglicherweise gezwungen, direkt mit ihnen zu kommunizieren. Manchmal nur sie öffnen kann die Bergmann-Infektion auslösen.
Eine zusätzliche Technik wäre sicherlich die Verwendung von Nutzlastdienstanbietern, die mit diesen Techniken oder über Filesharing-Netzwerke verbreitet werden können, BitTorrent ist nur eine der am meisten bevorzugt diejenigen,. Es wird regelmäßig verwendet, um sowohl legitime Softwareanwendungen als auch Daten sowie Piratenmaterial zu verbreiten. Zwei eines der beliebtesten Streckendienstanbieter sind folgende:
Andere Ansätze, die von den Tätern in Betracht gezogen werden können, umfassen die Verwendung von Browser-Hijackern - gefährliche Plugins, die mit den gängigsten Internetbrowsern kompatibel gemacht werden. Sie werden mit gefälschten Kundenreferenzen und Designerqualifikationen in die entsprechenden Datenbanken gestellt. Oft können die Zusammenfassungen enthalten Screenshots, Videoclips und ausgefeilte Beschreibungen versprechen hervorragende Funktionsverbesserungen sowie Leistungsoptimierungen. Trotzdem werden sich die Gewohnheiten der betroffenen Browser nach der Ratenzahlung sicherlich ändern- Einzelpersonen werden sicherlich feststellen, dass sie auf eine von Hackern kontrollierte Landing-Webseite weitergeleitet werden und auch ihre Einstellungen geändert werden können – die Standard-Startseite, Online-Suchmaschine und auch neue Registerkarten Webseite.

Wincache.exe: Analyse
Die Wincache.exe-Malware ist ein traditioneller Fall eines Kryptowährungsschürfers, der je nach Anordnung eine Vielzahl gefährlicher Aktionen ausführen kann. Sein Hauptziel ist es, komplexe mathematische Aufgaben auszuführen, die mit Sicherheit von den verfügbaren Systemressourcen profitieren: Zentralprozessor, GPU, Speicher und Festplattenspeicher. Die Methode, die sie verwenden, besteht darin, sich mit einem speziellen Webserver namens Mining Swimming Pool zu verbinden, von dem der erforderliche Code heruntergeladen und installiert wird. Sobald eine der Aufgaben heruntergeladen ist, wird sie sofort gestartet, mehrere Umstände können sofort ausgeführt werden. Wenn eine bereitgestellte Aufgabe abgeschlossen ist, wird eine weitere heruntergeladen und an ihrem Ort installiert, und die Schleife wird fortgesetzt, bis das Computersystem ausgeschaltet wird, die Infektion eliminiert wird oder ein weiterer ähnlicher Anlass eintritt. Kryptowährung werden zu den kriminellen Controller belohnt (Hacker-Gruppe oder eine einzelne cyber) direkt an ihre Budgets.
Eine unsichere Qualität dieser Klassifizierung von Malware ist, dass Beispiele wie dieses alle Systemquellen nehmen und das Computersystem des Opfers fast nutzlos machen können, bis die Gefahr tatsächlich vollständig beseitigt ist. Die meisten von ihnen beinhalten ein konsistentes Setup, das es wirklich schwierig macht, sie zu eliminieren. Diese Befehle werden sicherlich Anpassungen auch Optionen machen, Anordnungsdateien und auch Windows-Registrierungswerte, die die Wincache.exe-Malware mit Sicherheit automatisch starten lassen, sobald der Computer eingeschaltet wird. Der Zugang zu Nahrungsauswahl und Alternativen zur Wiederherstellung kann blockiert sein, was viele praktische Entfernungsanleitungen praktisch unwirksam macht.
Diese besondere Infektion wird das Setup eine Windows-Lösung für sich, die Einhaltung der durchgeführten Sicherheits- und Bewertung der Sicherheit von ther haben folgende Aktionen tatsächlich beobachtet worden:
. Während der Miner-Prozeduren kann sich die verknüpfte Malware mit bereits laufenden Windows-Diensten und installierten Anwendungen von Drittanbietern verbinden. Dadurch entdecken die Systemadministratoren möglicherweise nicht, dass die Ressource Tonnen aus einem separaten Prozess stammt.
| Name | Wincache.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware um Wincache.exe zu erkennen und zu entfernen |

Diese Art von Malware-Infektionen ist besonders effektiv bei der Ausführung anspruchsvoller Befehle, wenn sie so eingerichtet sind. Sie basieren auf einem modularen Rahmen, der es den kriminellen Kontrolleuren ermöglicht, alle Arten von schädlichem Verhalten zu orchestrieren. Eines der bevorzugten Beispiele ist die Änderung der Windows-Registrierung – Durch das Betriebssystem bedingte Anpassungszeichenfolgen können zu erheblichen Leistungsstörungen und auch zum Mangel an Zugriffsmöglichkeiten auf Windows-Dienste führen. Abhängig vom Umfang der Anpassungen kann es den Computer ebenfalls vollständig unbrauchbar machen. Andererseits können Anpassungen von Registry-Werten, die von gemounteten Anwendungen von Drittanbietern stammen, diese untergraben. Einige Anwendungen möglicherweise nicht vollständig freizugeben, während andere unerwartet Arbeits beenden können.
Dieser bestimmte Miner konzentriert sich in seiner aktuellen Version auf das Extrahieren der Monero-Kryptowährung, die eine geänderte Variante der XMRig-CPU-Mining-Engine enthält. Wenn sich die Projekte danach als erfolgreich erweisen, können zukünftige Versionen der Wincache.exe in Zukunft gestartet werden. Da die Malware machen Schwachstellen Einsatz von Software Ziel-Hosts zu infizieren, es kann als Trojaner auch mit Ransomware-Komponente eines unsicheren Koinfektion sein.
Die Beseitigung von Wincache.exe wird dringend empfohlen, da riskierst du nicht nur einen großen Stromaufwand, wenn es auf deinem COMPUTER läuft, Der Miner kann jedoch auch verschiedene andere unerwünschte Aktivitäten darauf ausführen und sogar Ihren PC dauerhaft beschädigen.
Wincache.exe-Entfernungsprozess
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” klicken, um Wincache.exe zu entfernen
SCHRITT 5. Wincache.exe entfernt!
Video Guide: So verwenden Sie GridinSoft Anti-Malware zum Entfernen von Wincache.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Wincache.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Wincache.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Wincache.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Wincache.exe”.







