Ein neuer, wirklich unsicher Kryptowährung Bergmann-Infektion wurde von Schutz Forscher entdeckt worden. die Malware, namens Emulation.exe kann Zielopfer infizieren, indem eine Auswahl von Möglichkeiten genutzt wird. Der Hauptpunkt hinter dem Emulation.exe-Miner ist die Verwendung von Cryptocurrency-Miner-Aktivitäten auf den Computersystemen von Opfern, um Monero-Symbole auf Ziele zu bringen’ Ausgaben. Das Ergebnis dieses Miners sind die erhöhten Stromrechnungen und auch wenn Sie es für längere Zeit verlassen, kann Emulation.exe sogar die Teile Ihres Computers beschädigen.
Emulation.exe: Verteilungsmethoden
Das Emulation.exe Malware nutzt 2 prominent Verfahren, die Computer-Targets werden verwendet, um verunreinigen:
- Payload Lieferung über Vor-Infektionen. Wenn eine ältere Emulation.exe-Malware auf den Zielsystemen bereitgestellt wird, kann sie sich sofort selbst aktualisieren oder eine neuere Version herunterladen. Dies ist mit dem eingebauten Update-Befehl möglich, der den Start erhält. Dies wird durch das Anbringen an einen bestimmten vordefinierten Hacker gesteuerten Web-Server durchgeführt, die den Malware-Code liefert. Die heruntergeladene und installieren Infektion wird den Namen eines Windows-Dienst erwerben und in die platziert werden “%System% temp” Platz. Wesentliche Eigenschaften und laufende Systemkonfigurationsdokumente werden transformiert, um eine anhaltende und auch leise Infektion zu ermöglichen.
- Software-Programm Ausnutzen von Sicherheitslücken. Es wurde festgestellt, dass die neueste Version der Emulation.exe-Malware durch einige Exploits verursacht wird, berühmt anerkannt für die Verwendung von in der Ransomware Angriffe gemacht werden. Die Infektionen werden durch Targeting offene Dienste über den TCP-Port erfolgen. Die Angriffe sind von einem Hacker-gesteuerte Struktur automatisiert, die für die Suche, wenn der Port offen ist. Wenn dieses Problem erfüllt ist, wird es sicherlich die Lösung scannen und Details dazu erhalten, Bestehend aus jeder Art von Variation und auch Setup-Daten. Ventures und prominente Benutzername und Passwort-Kombinationen getan werden könnten. Wenn die Manipulation im Vergleich zum anfälligen Code ausgelöst wird, wird der Miner sicherlich zusätzlich zur Hintertür freigelassen. Dies wird die eine doppelte Infektion bieten.
Zusätzlich zu diesen Ansätzen auch andere Techniken verwendet werden können,. Miner können durch Phishing-E-Mails, die en gros auf SPAM-ähnliche Weise verschickt werden, zerstreut werden und sind auf Social-Engineering-Methoden angewiesen, um die Betroffenen zu verwirren, dass sie tatsächlich eine Nachricht von einer legitimen Lösung oder einem legitimen Unternehmen erhalten haben. Die Infektionsdaten können entweder direkt verbunden oder in die Körperkomponenten in Multimedia-Inhalte oder Nachrichtenlinks eingefügt werden.
Die Bösen können auch destruktive Touchdown-Webseiten erstellen, die als Download-Webseiten von Lieferanten dienen können, Software-Download-Websites und auch andere regelmäßig zugegriffen Orte. Wenn sie mit echten Adressen vergleichbar erscheinende Domainnamen und auch Sicherheitszertifikate verwenden, können die Personen dazu gebracht werden, mit ihnen zu kommunizieren. In vielen Fällen öffnen sie nur können die Bergmann-Infektion aktivieren.
Eine weitere Technik wäre die Nutzung von Nutzlastträgern, die mit den oben genannten Techniken oder über Document-Sharing-Netzwerke verbreitet werden können, BitTorrent ist nur eine der beliebtesten. Es wird regelmäßig verwendet, um sowohl seriöse Software als auch Daten und raubkopierte Webinhalte zu verbreiten. 2 der am meisten bevorzugten Nutzlast Service-Provider sind die folgenden:
Andere Techniken, die von den Tätern in Betracht gezogen werden können, bestehen in der Verwendung von Browser-Hijackern – gefährlichen Plugins, die mit den bekanntesten Webbrowsern kompatibel gemacht werden. Sie werden mit gefälschten Kundenreferenzen und auch Entwicklerqualifikationen an die entsprechenden Repositories übermittelt. In vielen Fällen können die Zusammenfassungen von Screenshots aus, Videos und ausgefeilte Zusammenfassungen ansprechende hervorragende Funktionserweiterungen sowie Leistungsoptimierungen. Bei der Installation wird sich das Verhalten der betroffenen Internetbrowser jedoch sicherlich ändern- Einzelpersonen werden feststellen, dass sie auf eine von Hackern kontrollierte Zielseite umgeleitet werden und ihre Einstellungen möglicherweise geändert werden – die Standard-Startseite, Internet-Suchmaschine und neue Registerkarten Webseite.

Emulation.exe: Analyse
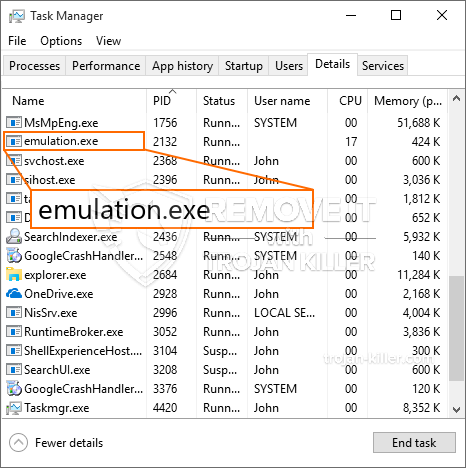
Die Malware Emulation.exe ist eine klassische Situation eines Kryptowährungs-Miners, der je nach Anordnung eine Vielzahl unsicherer Aktionen auslösen kann. Sein Hauptziel besteht darin, komplizierte mathematische Aufgaben auszuführen, die sicherlich die leicht verfügbaren Systemressourcen nutzen: Zentralprozessor, GPU, Speicher sowie Festplattenspeicher. Sie funktionieren, indem sie an einen speziellen Webserver namens Mining Swimming Pool angeschlossen werden, von dem der erforderliche Code heruntergeladen und installiert wird. Sobald bei den Arbeitsplätzen heruntergeladen wird es sicherlich gleichzeitig begonnen werden,, Es können mehrere Instanzen ausgeführt werden, sobald. Wenn eine bereitgestellte Aufgabe abgeschlossen ist, wird eine andere heruntergeladen und in ihrem Bereich installiert und die Lücke wird fortgesetzt, bis das Computersystem ausgeschaltet wird, die Infektion entfernt wird oder ein zusätzliches vergleichbares Ereignis eintritt. Kryptowährung werden zu den kriminellen Controller belohnt (Hacker-Gruppe oder ein einsames cyber) direkt an ihre Budgets.
Ein gefährliches Merkmal dieser Malware-Gruppe ist, dass Beispiele wie dieses alle Systemquellen nehmen und den betroffenen Computer fast unbrauchbar machen können, bis das Risiko vollständig beseitigt ist. Die meisten von ihnen verfügen über eine einheitliche Einrichtung, die von ihnen wirklich eine Herausforderung, um loszuwerden, macht. Diese Befehle werden sicherlich Anpassungen Boot-Optionen machen, Arrangement-Dateien sowie Windows-Registrierungswerte, die dazu führen, dass die Emulation.exe-Malware sofort nach dem Einschalten des Computers beginnt. Der Zugriff auf Wiederherstellungsmenüs sowie auf Alternativen kann behindert sein, was viele manuelle Eliminierungsübersichten fast nutzlos macht.
Diese besondere Infektion wird sicherlich Konfiguration eine Windows-Lösung für sich, die Einhaltung der durchgeführten Sicherheits- und Bewertung der Sicherheit von ther haben folgende Aktionen tatsächlich beobachtet worden:
. Während des miner Verfahrens können die zugehörigen Malware befestigen bereits mit Windows-Lösungen und Fremd Set up-Anwendungen. so dass die Systemadministratoren entdecken möglicherweise nicht, dass die Quelle Belastung stammt aus einer anderen Prozedur, indem Sie.
| Name | Emulation.exe |
|---|---|
| Kategorie | Trojan |
| Unterkategorie | Kryptowährung Miner |
| Gefahren | Hohe CPU-Auslastung, Internet Geschwindigkeitsreduzierung, PC stürzt ab und gefriert und etc. |
| Hauptzweck | Um Geld für Cyber-Kriminelle zu machen |
| Verteilung | Torrents, Gratis Spiele, Cracked Apps, Email, fragwürdige Websites, Abenteuer |
| Entfernung | Installieren GridinSoft Anti-Malware Emulation.exe erkennen und entfernen |

Diese Art von Malware-Infektionen sind besonders zuverlässig bei der Ausführung anspruchsvoller Befehle, wenn sie so eingerichtet sind. Sie basieren auf einem modularen Rahmen, der es den kriminellen Kontrolleuren ermöglicht, alle Arten von gefährlichen Handlungen zu verwalten. Eines der bevorzugten Fällen ist die Änderung der Windows-Registrierung – betriebssystembedingte Modifikationszeichenfolgen können zu erheblichen Effizienzeinbußen und auch zum Ausfall des Zugriffs auf Windows-Lösungen führen. Unter Berufung auf den Bereich der Modifikationen kann es auch der Computer machen völlig sinnlos. Auf der anderen Seite kann die Manipulation von Registry-Werten, die von jeder Art von installierten Anwendungen von Drittanbietern stammen, diese sabotieren. Einige Anwendungen werden möglicherweise nicht vollständig eingeführt, während andere unerwartet nicht mehr funktionieren.
Dieser spezielle Miner in seiner aktuellen Variante konzentriert sich auf das Extrahieren der Monero-Kryptowährung, die aus einer modifizierten Version der XMRig-CPU-Mining-Engine besteht. Wenn die Kampagnen erfolgreich sind, können in Zukunft zukünftige Variationen der Emulation.exe eingeführt werden. Da die Malware nutzt Software-Schwachstellen Ziel-Hosts zu infizieren, es kann Teil eines schädlichen Koinfektion mit Ransomware und Trojanern auch.
Das Entfernen von Emulation.exe wird dringend empfohlen, da Sie nicht nur eine hohe Stromrechnung riskieren, wenn es auf Ihrem COMPUTER läuft, Der Miner kann jedoch zusätzlich verschiedene andere unerwünschte Aktivitäten ausführen und Ihren COMPUTER sogar dauerhaft beschädigen.
Emulation.exe Entfernungsprozess
SCHRITT 1. Zuerst, Sie müssen GridinSoft Anti-Malware herunterladen und installieren.
SCHRITT 2. Dann sollten Sie wählen “Schneller Scan” oder “Kompletter Suchlauf”.
SCHRITT 3. Führen Sie Ihren Computer scannen
SCHRITT 4. Nachdem der Scan abgeschlossen, Sie müssen klicken Sie auf “Sich bewerben” Schaltfläche zum Entfernen von Emulation.exe
SCHRITT 5. Emulation.exe entfernt!
Video Guide: So verwenden Sie GridinSoft Anti-Malware zum Entfernen von Emulation.exe
Wie Sie Ihren PC vor einer reinfected mit verhindern “Emulation.exe” in der Zukunft.
Eine leistungsstarke Antivirus-Lösung, und Block dateilosen Malware erkennen kann, ist, was Sie brauchen! Herkömmliche Lösungen erkennen Malware auf Basis von Virendefinitionen, und daher können sie oft nicht erkennen, “Emulation.exe”. GridinSoft Anti-Malware bietet Schutz gegen alle Arten von Malware, einschließlich dateilosen Malware wie “Emulation.exe”. GridinSoft Anti-Malware bietet Cloud-basierten Verhaltensanalysators alle unbekannten Dateien einschließlich Zero-Day-Malware zu blockieren. Eine solche Technologie kann erkennen und vollständig entfernen “Emulation.exe”.







