Das Unternehmen sagte, dass eine unbekannte Gruppe von Cyber-Kriminellen in realen Angriffen bereits dieses Sicherheitsproblem aktiv ausgenutzt.
The vulnerability received an identifier CVE-2019-27296, und, nach der Skala CVSS, sie empfangen 9.8 weist darauf hin, von 10.„Aufgrund der Schwere dieser Sicherheitsanfälligkeit, Oracle empfiehlt Kunden Updates so bald wie möglich anzuwenden“, - warnen in Oracle.
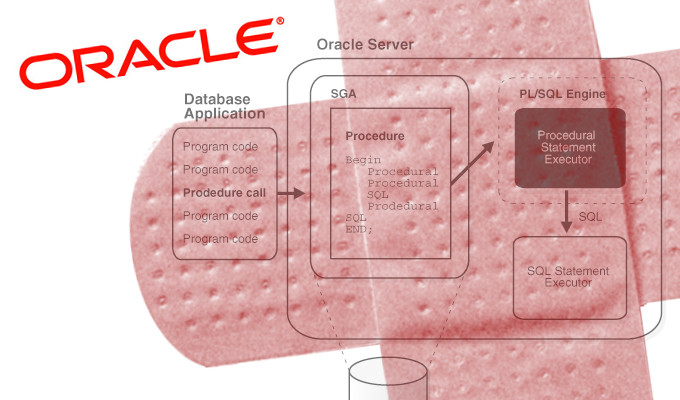
The breach is described as a deserialization problem in Oracle WebLogic Server Web Services via XMLDecoder, allowing a remote unauthorized attacker to execute arbitrary code on the victim’s server. This results in complete control over the attacked server.
lesen Sie auch: Angreifer Exploits aktiv zuvor entdeckte Schwachstelle in Oracle WebLogic
“The vulnerability of remote code execution can be exploited without having to go through the authentication process. Somit, an attacker can use a security problem without having username or password,“ – said in the Oracle notification.
Company also noted connection of this vulnerability with a previously unmentioned problem of deserialization under the identifier CVE-2019-2725. She was also present at Oracle WebLogic Server, Aber was patched in April of this year.
Quelle: https://www.oracle.com
