dbheuPYTtA.exe is a malicious file, which is also a running process. It is related to System Repair scam. This program is a serious virus that attacks many computers all over the world today. System Repair trojan is a fake system optimization and hard drive defragmentation utility that acts very aggressively in reaching its many evil purposes. The primary goal of this hoax, of course, is to make money for its developers. dbheuPYTtA.exe is the core process of this malware. The problem is that it cannot be easily terminated with Task Manager, for example. The rogue blocks its launching. In addition, it also hides the majority of your files, such as documents, pictures, desktop icons, etc. This is done by adding the hidden attribute to the majority of such files and folders and by relocating them to the Temp directory, which is hidden likewise. To get rid of System Repair malware and to restore your hidden files please follow the guidelines below.
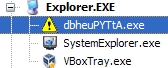
How dbheuPYTtA.exe process looks like:
In order to remove System Repair malware from your PC it is strongly recommended that you first run GridinSoft Trojan Killer. Use Win + E” hotkey combination to open “My Computer” window. From this stage (in the address field) you may insert the address of GridinSoft Trojan Killer’s site https://trojan-killer.net and download our recommended software. Install and update it, run the scan and remove all threats it finds. Then download two additional free applications called Unhider.exe and restore.exe . The download links are as follows:
- GridinSoft Unhider https://trojan-killer.net/download/unhider.exe
- GridinSoft Restore https://trojan-killer.net/download/restore.exe
Run both of them and reboot your PC. Good luck!
System Repair automatic remover:
Similar removal video at YouTube:
System Repair manual remover:
Delete System Repair files:
%AppData%\Microsoft\Internet Explorer\Quick Launch\System_Repair.lnk
%Desktopdir%\System_Repair.lnk
%Programs%\System Repair\System Repair.lnk
%Programs%\System Repair\Uninstall System Repair.lnk
%CommonAppData%\[rnd_0].exe
%CommonAppData%\[rnd_1]
%CommonAppiData%\[rnd_1].exe
Delete System Repair registry entries:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\[rnd_0].exe %CommonAppData%\[rnd_0].exe
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system\DisableTaskMgr 0
