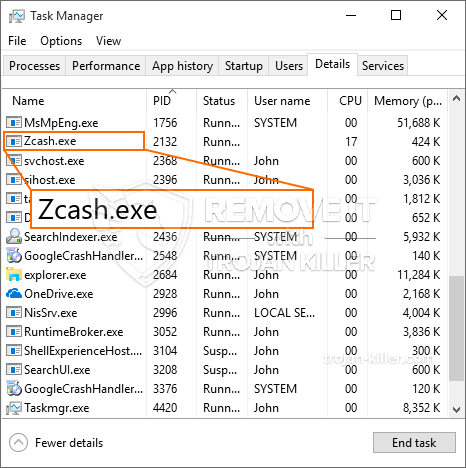
Et helt nyt, ekstremt skadelig kryptokurrencyminerinfektion er blevet opdaget af beskyttelsesforskere. den malware, hedder Zcash.exe kan forurene målramte ved hjælp af et udvalg af metoder. Essensen bag Zcash.exe-minearbejderen er at anvende cryptocurrency-minearbejderopgaver på de syges computere for at erhverve Monero-symboler til målpris. The outcome of this miner is the raised power costs and if you leave it for longer periods of time Zcash.exe may even harm your computer systems parts.
Zcash.exe: distributionssystemer Metoder
Det Zcash.exe malware gør brug af 2 popular methods which are made use of to contaminate computer system targets:
- Payload Levering via Prior Infektioner. If an older Zcash.exe malware is released on the target systems it can instantly upgrade itself or download a more recent variation. This is feasible by means of the built-in upgrade command which gets the release. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, som leverer malware kode. The downloaded and install virus will get the name of a Windows solution and also be positioned in the “%systemet% temp” Beliggenhed. Vital properties and also running system setup documents are altered in order to allow a consistent as well as quiet infection.
- Software sårbarhed udnytter. The latest variation of the Zcash.exe malware have actually been found to be triggered by the some exploits, widely recognized for being used in the ransomware strikes. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Angrebene automatiseres af en hacker-kontrolleret struktur, der ser op, hvis porten er åben. If this problem is satisfied it will certainly scan the solution and also obtain information regarding it, consisting of any version and setup data. Udnyttelse såvel som foretrukne brugernavn og også adgangskodeblandinger kan udføres. When the make use of is set off against the prone code the miner will be released in addition to the backdoor. Dette vil bestemt præsentere en dobbelt infektion.
Aside from these approaches other methods can be utilized too. Miners can be distributed by phishing e-mails that are sent wholesale in a SPAM-like fashion as well as depend on social engineering techniques in order to puzzle the targets into believing that they have obtained a message from a reputable solution or firm. The infection documents can be either directly connected or placed in the body components in multimedia material or message links.
The lawbreakers can likewise develop harmful touchdown web pages that can pose supplier download web pages, software program download websites and other frequently accessed locations. When they utilize similar sounding domain names to legitimate addresses and also protection certifications the individuals may be pushed right into connecting with them. I nogle tilfælde kan blot åbning af dem aktivere minerinfektionen.
An additional approach would be to use haul service providers that can be spread out making use of the above-mentioned approaches or through data sharing networks, BitTorrent er blot en af en af de mest populære dem. It is often used to distribute both legitimate software and files and pirate material. 2 af en af de mest prominente udbydere af nyttelasttjenester er følgende:
Various other approaches that can be taken into consideration by the lawbreakers include the use of web browser hijackers -unsafe plugins which are made compatible with one of the most popular web internet browsers. They are posted to the relevant databases with fake user testimonials and also designer credentials. Ofte kan beskrivelserne bestå af skærmbilleder, video clips and also sophisticated descriptions promising great feature enhancements and also efficiency optimizations. However upon installation the actions of the impacted internet browsers will certainly transform- individuals will certainly locate that they will be redirected to a hacker-controlled touchdown page and also their settings may be changed – standard startside, søgemaskine og også nye faner side.

Zcash.exe: Analyse
The Zcash.exe malware is a traditional situation of a cryptocurrency miner which depending on its arrangement can cause a wide range of harmful activities. Its main objective is to carry out complicated mathematical tasks that will take advantage of the offered system resources: CPU, GPU, hukommelse samt harddisk plads. The means they function is by connecting to a special web server called mining pool from where the called for code is downloaded. Så hurtigt som blandt opgaverne bliver downloadet det vil blive startet samtidigt, flere omstændigheder kan køres på en gang. When an offered job is completed another one will certainly be downloaded and install in its place as well as the loophole will certainly proceed till the computer system is powered off, the infection is removed or another similar occasion occurs. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking team eller en enkelt cyberpunk) direkte til deres tegnebøger.
An unsafe attribute of this classification of malware is that samples such as this one can take all system resources and virtually make the target computer unusable up until the hazard has actually been totally eliminated. A lot of them feature a persistent installation which makes them truly difficult to get rid of. Disse kommandoer vil helt sikkert foretage justeringer også muligheder, setup data and Windows Registry values that will make the Zcash.exe malware start instantly as soon as the computer system is powered on. Access to recuperation menus and choices may be obstructed which renders numerous manual elimination guides virtually useless.
Denne særlige infektion vil konfigurationshåndtering en Windows-tjeneste for sig selv, following the carried out security evaluation ther complying with activities have been observed:
. During the miner operations the linked malware can connect to already running Windows services and also third-party mounted applications. By doing so the system managers might not discover that the resource lots originates from a different procedure.
| Navn | Zcash.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Zcash.exe |

Denne type malware infektioner er specielt effektiv til varetagelse innovative kommandoer, hvis sat op, så. De er baseret på en modulær struktur tillader de kriminelle controllere til at koordinere alle slags skadelige vaner. Blandt de populære forekomster er justeringen af Windows-registreringsdatabasen – justeringer strenge forbundet af operativsystemet kan udløse alvorlige effektivitet forstyrrelser og også den manglende adgang Windows-løsninger. Afhængig af omfanget af ændringer det kan også gøre computersystemet helt meningsløst. På de forskellige gengæld manipulation af Registry worths tilhører nogen form for tredjeparts oprettet programmer kan sabotere dem. Nogle applikationer kan falde kort for at frigive helt, mens andre kan pludselig stoppe arbejdsdag.
Denne vis minearbejder i sin eksisterende variation er fokuseret på at udvinde den Monero cryptocurrency herunder en modificeret version af XMRig CPU minedrift motor. If the campaigns show successful after that future versions of the Zcash.exe can be launched in the future. Da de malware gør brug af software program susceptabilities at inficere target værter, det kan være en del af en usikker co-infektion med ransomware og trojanske heste.
Elimination of Zcash.exe is highly advised, betragtning af, at du tager chancen for ikke bare en kæmpe elektrisk strøm omkostninger, hvis det fungerer på din pc, men minearbejder kan ligeledes udføre forskellige andre uønskede aktiviteter på det og også skade din computer helt.
Zcash.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Zcash.exe
TRIN 5. Zcash.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Zcash.exe
Hvordan undgår din pc fra at blive inficeret med “Zcash.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Zcash.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Zcash.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Zcash.exe”.







