Et helt nyt, meget usikker kryptokurrency-minearbejdervirus er faktisk blevet identificeret af beskyttelsesforskere. den malware, hedder Xmr-stak.exe kan inficere målgrupper ved hjælp af en række forskellige metoder. Hovedpunktet bag Xmr-stak.exe-minearbejderen er at bruge kryptovaluta-mineropgaver på syges computersystemer for at opnå Monero-symboler på mål’ udgifter. The result of this miner is the raised electrical energy costs and also if you leave it for longer time periods Xmr-stak.exe might also harm your computer’s components.
Xmr-stak.exe: distributionssystemer Metoder
Det Xmr-stak.exe malware udnytter 2 prominent methods which are used to infect computer targets:
- Payload Levering gennem Prior Infektioner. If an older Xmr-stak.exe malware is released on the sufferer systems it can immediately update itself or download and install a newer variation. This is feasible by means of the integrated upgrade command which gets the release. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. Den hentet og installere virus vil helt sikkert få navnet på en Windows service og også placeres i den “%systemet% temp” Beliggenhed. Important buildings as well as running system configuration files are changed in order to allow a consistent and silent infection.
- Software programmet sårbarhed udnytter. The latest version of the Xmr-stak.exe malware have been located to be brought on by the some ventures, famously known for being used in the ransomware strikes. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som søger efter hvis porten er åben. If this condition is fulfilled it will certainly scan the solution and also retrieve info regarding it, including any type of variation and also arrangement information. Ventures og også populære brugernavn og også adgangskode blandinger kan gøres. When the manipulate is activated against the at risk code the miner will be deployed in addition to the backdoor. Dette vil bestemt præsentere en dobbelt infektion.
Apart from these approaches various other techniques can be made use of too. Miners can be distributed by phishing emails that are sent wholesale in a SPAM-like way and rely on social engineering tricks in order to confuse the victims into believing that they have actually received a message from a reputable service or business. The infection documents can be either straight connected or inserted in the body materials in multimedia web content or text web links.
The wrongdoers can likewise create destructive landing pages that can impersonate supplier download pages, software application download websites and also various other regularly accessed places. When they use similar seeming domain names to reputable addresses and also protection certifications the individuals may be persuaded into communicating with them. I nogle tilfælde blot åbne dem kan udløse minearbejder infektion.
An additional strategy would certainly be to make use of payload service providers that can be spread out utilizing the above-mentioned methods or using file sharing networks, BitTorrent er en af en af de mest fremtrædende dem. It is frequently used to disperse both genuine software program as well as files as well as pirate web content. 2 af de mest populære trækudbydere er følgende:
Various other approaches that can be thought about by the offenders consist of making use of browser hijackers -dangerous plugins which are made suitable with the most preferred web internet browsers. They are posted to the relevant databases with fake individual testimonials and also developer qualifications. I mange tilfælde beskrivelserne kan bestå af skærmbilleder, video clips as well as elaborate descriptions promising fantastic attribute improvements and performance optimizations. Nevertheless upon installation the habits of the affected web browsers will alter- individuals will discover that they will certainly be rerouted to a hacker-controlled landing page as well as their settings might be changed – standard webside, online søgemaskine samt nye faner webside.
Xmr-stak.exe: Analyse
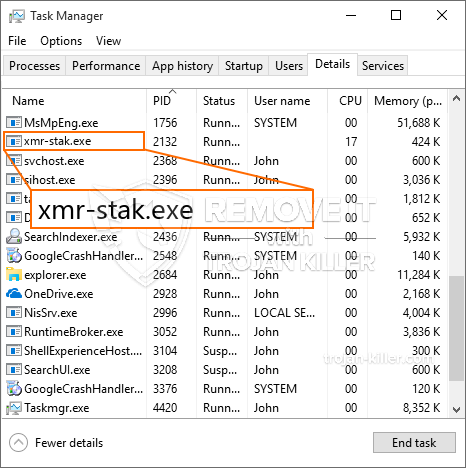
The Xmr-stak.exe malware is a classic instance of a cryptocurrency miner which depending on its arrangement can create a wide range of dangerous activities. Dets hovedmål er at udføre komplicerede matematiske job, der helt sikkert vil få mest muligt ud af de tilbudte systemressourcer: CPU, GPU, hukommelse og også harddisk område. De midler, de fungerer, er ved at tilslutte sig en unik server kaldet mineswimmingpool, hvorfra den nødvendige kode downloades og installeres. As soon as among the jobs is downloaded it will be begun simultaneously, flere forekomster kan være væk, så snart. When a given task is finished one more one will be downloaded and install in its place and also the loophole will proceed up until the computer system is powered off, infektionen er elimineret, eller der sker en mere sammenlignelig hændelse. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking team eller en enkelt cyberpunk) lige til deres budgetter.
A hazardous attribute of this group of malware is that examples such as this one can take all system sources and also almost make the sufferer computer system pointless until the hazard has actually been completely gotten rid of. The majority of them include a relentless installation which makes them truly difficult to eliminate. Disse kommandoer vil foretage ændringer til at starte alternativer, setup files and Windows Registry values that will certainly make the Xmr-stak.exe malware begin automatically when the computer is powered on. Accessibility to healing food selections as well as alternatives might be obstructed which provides many hand-operated elimination overviews almost worthless.
Denne vis infektion vil arrangementet en Windows-tjeneste for sig selv, complying with the conducted safety evaluation ther adhering to actions have actually been observed:
Under minearbejdere kan den tilknyttede malware oprette forbindelse til allerede kørende Windows-tjenester og tredjeparts opsatte applikationer. Ved at gøre det ser systemadministratorerne muligvis ikke, at kildelotterne stammer fra en anden proces.
| Navn | Xmr-stak.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Xmr-stak.exe |

Denne type malware-infektioner er især effektive til at udføre innovative kommandoer, hvis de er konfigureret. De er baseret på en modulopbygget struktur, der tillader de kriminelle kontrollører at styre alle typer farlige vaner. Et af de fremtrædende eksempler er justeringen af Windows-registreringsdatabasen – ændringsstrenge, der er forbundet med operativsystemet, kan skabe alvorlige effektivitetsafbrydelser samt den manglende evne til tilgængelighed Windows-tjenester. Afhængig af omfanget af ændringer kan det også gøre computeren helt meningsløs. På den anden side kan justering af registerværdier, der kommer fra enhver form for opsætningsapplikationer fra tredjepart, sabotere dem. Nogle applikationer kan muligvis ikke introducere helt, mens andre pludselig kan stoppe med at arbejde.
Denne specifikke miner i sin nuværende version er fokuseret på at udvinde Monero cryptocurrency indeholdende en ændret version af XMRig CPU-minedriftmotor. If the projects confirm effective then future variations of the Xmr-stak.exe can be launched in the future. Da malware udnytter sårbarheder i software til at inficere target værter, det kan være en del af en farlig co-infektion med ransomware samt trojanske heste.
Elimination of Xmr-stak.exe is highly advised, da du tager chancen for ikke kun en enorm elektrisk energiudgift, hvis den kører på din pc, men minearbejderen kan desuden udføre forskellige andre uønskede aktiviteter på det såvel som også skade din COMPUTER fuldstændigt.
Xmr-stak.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Xmr-stak.exe
TRIN 5. Xmr-stak.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Xmr-stak.exe
Hvordan undgår din pc fra at blive inficeret med “Xmr-stak.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Xmr-stak.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Xmr-stak.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Xmr-stak.exe”.







