Et helt nyt, meget farlig cryptocurrency minearbejder infektion er blevet identificeret af forskere beskyttelse. den malware, hedder Wlanext.exe kan inficere målramte ved at bruge en række måder. Essensen bag Wlanext.exe minearbejder er at udnytte cryptocurrency minearbejder aktiviteter på edb-systemerne i mål med henblik på at erhverve Monero tokens på syge bekostning. Resultatet af denne minearbejder er de forhøjede elregninger, og hvis du forlader den i længere perioder, kan Wlanext.exe også beskadige dine computersystemkomponenter.
Wlanext.exe: distributionssystemer Metoder
Det Wlanext.exe malware udnytter 2 fremtrædende metoder, som bliver brugt til at forurene computermål:
- Payload Levering hjælp Prior Infektioner. Hvis en ældre Wlanext.exe malware er implementeret på målsystemerne, kan den øjeblikkeligt opgradere sig selv eller downloade og installere en nyere variant. Dette er muligt ved hjælp af den integrerede opgradering kommando, som erhverver udgivelsen. Dette gøres ved at tilslutte sig en bestemt foruddefineret hacker-styret server, som tilbyder malware-koden. Den downloadede og installerede infektion vil helt sikkert få navnet på en Windows-løsning og blive placeret i “%systemet% temp” areal. Vigtige bolig- eller erhvervsejendomme samt kørende systemkonfigurationsdokumenter transformeres for at tillade en vedvarende såvel som tavs infektion.
- Software programmet sårbarhed udnytter. Den nyeste variant af Wlanext.exe-malwaren er faktisk blevet lokaliseret til at blive udløst af nogle udnyttelser, populært kendt for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert tjekke tjenesten samt hente information om den, herunder enhver version samt arrangementsoplysninger. Udnyttelse og fremtrædende brugernavn og adgangskodekombinationer kan udføres. Når brugen af er modregnet i forhold til den tilbøjelige kode, vil minearbejderen helt sikkert blive indsat sammen med bagdøren. Dette vil danne en dobbelt infektion.
Ud over disse tilgange kan andre metoder også gøres brug af. Minearbejdere kan spredes af phishing-e-mails, der sendes engros på en SPAM-lignende måde og er afhængige af sociale designteknikker for at forvirre målene til at tro, at de har fået en besked fra en ægte løsning eller et firma. Virusfilerne kan enten anbringes direkte eller placeres i kroppens materialer i multimediewebindhold eller tekstweblinks.
De kriminelle kan ligeledes oprette destruktive landingswebsider, der kan gøre det muligt for leverandøren at downloade og installere websider, software ansøgning downloade portaler samt andre ofte adgang placeringer. Når de bruger lignende domæne til velrenommerede adresser og beskyttelsescertifikater, kan personerne blive tvunget til at kommunikere med dem. I nogle tilfælde bare åbne dem kan modregne minearbejder infektion.
En yderligere strategi ville være at bruge udbydere af transporttjenester, der kan spredes ved hjælp af disse tilgange eller via datadelingsnetværk, BitTorrent er en af en af de mest foretrukne dem. Det bliver ofte brugt til at distribuere både ægte softwareapplikationer samt filer og piratwebindhold. 2 af en af de mest foretrukne nyttelast tjenesteydere er følgende:
Forskellige andre metoder, der kan tænkes over af lovovertræderne, består af brugen af internetbrowser hijackers -usikre plugins, som er gjort kompatible med en af de mest fremtrædende internetbrowsere. De uploades til de relevante databaser med falske kundeanmeldelser og også udviklerlegitimationsoplysninger. Ofte resuméer kan omfatte skærmbilleder, videoklip og sofistikerede beskrivelser, der lover fantastiske funktionsforbedringer og ydeevneoptimeringer. Ikke desto mindre vil handlingerne fra de berørte internetbrowsere ændre sig ved installationen- kunder vil opdage, at de vil blive omdirigeret til en hacker-styret touchdown-webside, og deres opsætninger kan også blive ændret – standard webside, søgemaskine og splinternye faneblad.

Wlanext.exe: Analyse
Wlanext.exe-malwaren er et tidløst tilfælde af en cryptocurrency-minearbejder, som ved at stole på dens opsætning kan skabe en lang række farlige handlinger. Dets hovedmål er at udføre komplekse matematiske opgaver, der helt sikkert vil drage fordel af de let tilgængelige systemkilder: CPU, GPU, hukommelse og også harddiskplads. Den måde, de fungerer på, er ved at knytte sig til en speciel webserver kaldet mining swimmingpool, hvor den krævede kode downloades og installeres. Så hurtigt som et af jobene downloades, vil det helt sikkert blive startet på én gang, adskillige omstændigheder kan køres på én gang. Når en tilbudt opgave er afsluttet, downloades en yderligere en på sin plads, og smuthulet fortsætter helt sikkert, indtil computeren er slukket, infektionen elimineres, eller en yderligere lignende begivenhed forekommer. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres pengepung.
Et farligt træk ved denne klassificering af malware er, at eksempler som denne kan tage alle systemkilder samt praktisk talt gøre målcomputeren ubrugelig, indtil risikoen er blevet fjernet fuldstændigt. De fleste af dem har en vedvarende installation, der gør dem virkelig udfordrende at fjerne. Disse kommandoer foretager ændringer i startindstillinger, konfigurationsfiler og også værdier i Windows registreringsdatabasen, der vil få Wlanext.exe-malwaren til at starte med det samme, når computeren er tændt. Tilgængelighed til helbredende valg af fødevarer såvel som alternativer kan blokeres, hvilket gør adskillige håndbetjente fjernelsesoversigter næsten værdiløse.
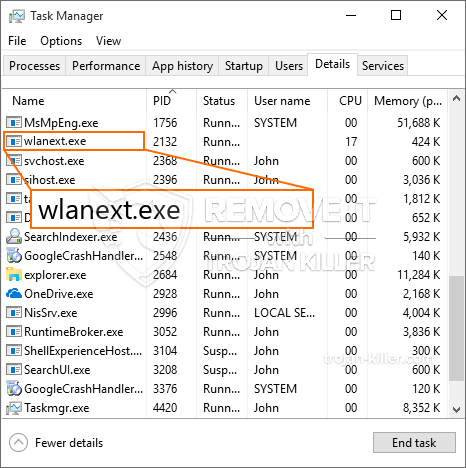
Denne bestemte infektion vil bestemt arrangere en Windows-tjeneste for sig selv, efter den udførte sikkerhedsanalyse er de følgende aktiviteter faktisk blevet observeret:
. Under gruvearbejderdriften kan den tilknyttede malware oprette forbindelse til aktuelt kørende Windows-tjenester såvel som installerede applikationer fra tredjepart. Dermed bemærker systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden procedure.
| Navn | Wlanext.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at finde og fjerne Wlanext.exe |

Denne type malwareinfektioner er særligt effektive til at udføre innovative kommandoer, hvis de er konfigureret således. De er baseret på en modulær ramme, der giver de kriminelle kontrollere mulighed for at orkestrere alle former for farlige handlinger. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – modifikationsstrenge forbundet med operativsystemet kan forårsage alvorlige forstyrrelser i ydeevnen såvel som manglende adgang til Windows-løsninger. At stole på omfanget af ændringer kan det også gøre computeren helt meningsløs. På den anden side kan manipulation af registerværdier, der tilhører tredjepartsinstallerede applikationer, sabotere dem. Nogle applikationer mangler muligvis helt, mens andre uventet kan stoppe med at arbejde.
Denne specifikke minearbejder i sin eksisterende variation er koncentreret om at udvinde Monero-kryptovalutaen, der består af en ændret version af XMRig CPU-minedriftmotoren. Hvis kampagnerne efter det bekræftes, at de er effektive, kan fremtidige varianter af Wlanext.exe lanceres i fremtiden. Da malware anvender softwarefølsomhed til at forurene målværter, det kan være en del af en usikker co-infektion med ransomware samt trojanske heste.
Fjernelse af Wlanext.exe anbefales kraftigt, i betragtning af at du risikerer ikke kun en stor strømudgift, hvis den fungerer på din pc, men minearbejderen kan også udføre forskellige andre uønskede aktiviteter på den og også endda skade din COMPUTER permanent.
Wlanext.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne Wlanext.exe
TRIN 5. Wlanext.exe er fjernet!
Video guide: Sådan bruger du GridinSoft Anti-Malware til at fjerne Wlanext.exe
Hvordan undgår din pc fra at blive inficeret med “Wlanext.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Wlanext.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Wlanext.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Wlanext.exe”.







