Et helt nyt, meget usikker cryptocurrency minearbejder virus er faktisk blevet spottet af forskere beskyttelse. den malware, hedder Wineth-setup.exe kan inficere målgrupper ved hjælp af et udvalg af midler. Essensen bag Wineth-setup.exe minearbejder er at udnytte cryptocurrency minearbejder aktiviteter på computere mål for at opnå Monero tokens på mål regning. Resultatet af denne miner er de forhøjede strømudgifter, og hvis du lader det være i længere tid, kan Wineth-setup.exe endda skade dine computerkomponenter.
Wineth-setup.exe: distributionssystemer Metoder
Det Wineth-setup.exe malware bruger to foretrukne metoder, der bruges til at forurene computermål:
- Payload Levering hjælp Prior Infektioner. Hvis en ældre Wineth-setup.exe-malware frigives på de lidende systemer, kan den automatisk opgradere sig selv eller downloade en nyere version. Dette er muligt via den indbyggede opdatering kommando, som får frigivelsen. Dette gøres ved at linke til en specifik foruddefineret hacker-kontrollerede server, som leverer malware kode. Den downloadede virus får bestemt navnet på en Windows-tjeneste og placeres i “%Systemet% temp” Beliggenhed. Vitale boligejendomme såvel som opsætningsfiler til operativsystemet ændres for at muliggøre en konsekvent og også stille infektion.
- Software programmet sårbarhed udnytter. Den seneste variant af Wineth-setup.exe-malware er blevet fundet for at blive fremført af nogle ventures, populært forstået for at blive brugt i ransomware-overfald. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Overgrebene er automatiseret af en hacker-kontrolleret struktur, som ser op hvis porten er åben. Hvis dette problem er opfyldt, vil det helt sikkert scanne løsningen samt få info om det, herunder enhver form for version, og også opsætning oplysninger. Ventures såvel som fremtrædende brugernavn og også adgangskodekombinationer kan udføres. Når manipuleringen er aktiveret versus den udsatte kode, frigøres minearbejderen helt sikkert sammen med bagdøren. Dette vil præsentere en dobbelt infektion.
Bortset fra disse metoder andre strategier kan også bruges. Minearbejdere kan spredes ved hjælp af phishing-e-mails, der sendes i bulk på en SPAM-lignende måde samt stole på sociale designteknikker for at få ofrene til at tro, at de har fået en besked fra en legitim løsning eller virksomhed. Virusdokumenterne kan enten vedhæftes direkte eller indsættes i kropsindholdet i multimedieindhold eller tekstlinks.
De lovovertrædende kan ligeledes oprette skadelige destinationswebsider, der kan udgøre leverandørhentningssider, software download-websteder og også forskellige andre områder, der regelmæssigt har adgang til. Når de bruger lignende lydende domænenavne til legitime adresser såvel som sikkerhedscertificeringer, kan brugerne tvinges til at interagere med dem. I mange tilfælde blot at åbne dem kan udløse minearbejder infektion.
En anden teknik ville helt sikkert være at bruge nyttelastbærere, der kan spredes ud ved hjælp af ovennævnte metoder eller gennem fildelingsnetværk, BitTorrent er en af de mest foretrukne dem. Det bruges regelmæssigt til at distribuere både velrenommeret softwareapplikation såvel som dokumenter samt piratmateriale. To af en af de mest foretrukne leverandører af nyttelast er følgende:
Andre teknikker, der kan tages i betragtning af de skurke fyre, består i at gøre brug af internetbrowserkapere - farlige plugins, der er velegnet med en af de mest prominente internetbrowsere. De offentliggøres til de relevante arkiver med falske kundebedømmelser og også udviklerkvalifikationer. I de fleste tilfælde resuméerne kan bestå af skærmbilleder, videoklip samt indviklede beskrivelser, der appellerer til fantastiske attributforbedringer samt ydeevneoptimeringer. Imidlertid vil vanerne hos de berørte internetbrowsere ændre sig efter installationen- brugere vil helt sikkert finde ud af, at de helt sikkert vil blive omdirigeret til en hackerstyret touchdown-side, og også deres indstillinger kan ændres – standard startside, søgemaskine på internettet og også helt nye faner side.

Wineth-setup.exe: Analyse
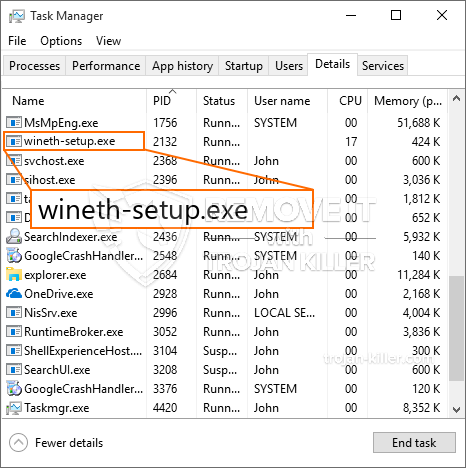
Wineth-setup.exe-malware er et klassisk tilfælde af en minearbejder, der afhænger af dens konfiguration kan forårsage en bred vifte af farlige aktiviteter. Dets primære mål er at udføre indviklede matematiske job, der får mest ud af de tilbudte systemkilder: CPU, GPU, hukommelse og også harddiskplads. De midler, de fungerer, er ved at linke til en speciel webserver kaldet minedrift, hvor den kaldte kode downloades. Så snart en af opgaverne er downloadet, startes den på samme tid, adskillige tilfælde kan køres på når. Når en tilbudt opgave er afsluttet, bliver en mere downloadet og installeret i stedet, og smuthullet vil helt sikkert fortsætte, indtil computersystemet er slukket, infektionen er fjernet eller en anden lignende lejlighed finder sted. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt hacker) direkte til deres budgetter.
Et usikkert træk ved denne klassificering af malware er, at prøver, der ligner denne, kan tage alle systemkilder og også praktisk talt gøre offerets computersystem meningsløst, indtil faren faktisk er helt elimineret. De fleste af dem inkluderer en vedvarende rate, der gør dem virkelig svære at slippe af med. Disse kommandoer vil bestemt også ændre indstillingerne, opsætningsfiler samt Windows-registreringsværdier, der får Wineth-setup.exe-malware til at begynde med det samme, når computersystemet er tændt. Adgang til helbredende menuer og også muligheder kan blive blokeret, hvilket gør adskillige manuelle fjernelsesoversigter næsten ubrugelige.
Denne specifikke infektion vil helt sikkert konfigurationshåndtering en Windows-tjeneste for sig selv, overholdelse af den udførte sikkerhedsanalyse, hvor følgende aktiviteter faktisk er blevet observeret:
. Under minearbejdere kan den tilsluttede malware vedhæfte til aktuelt kørende Windows-løsninger og installerede applikationer fra tredjepart. Ved at gøre det ser systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden proces.
| Navn | Wineth-setup.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at opdage og fjerne Wineth-setup.exe |

Denne form for malwareinfektioner er særligt effektive til at udføre avancerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der tillader kriminelle kontrollere at koordinere alle slags farlige handlinger. Blandt de prominente tilfælde er ændringen af registreringsdatabasen i Windows – justeringsstrenge tilknyttet operativsystemet kan forårsage betydelige afbrydelser i ydeevnen og manglende evne til at få adgang til Windows-løsninger. At stole på rækkevidden af ændringer kan det desuden gøre computeren helt ubrugelig. På den anden side kan justering af registreringsværdier, der hører til enhver form for tredjeparts opsatte applikationer, sabotere dem. Nogle applikationer stopper muligvis med at arbejde for at frigive helt, mens andre uventet kan stoppe med at arbejde.
Denne bestemte minearbejder i sin eksisterende variation er fokuseret på at udvinde Monero-kryptovalutaen, der indeholder en tilpasset variation af XMRig CPU-minedriftmotoren. Hvis kampagnerne viser sig effektive, kan fremtidige variationer af Wineth-setup.exe introduceres i fremtiden. Da malware bruger sårbarheder i software til at inficere target værter, det kan være bestanddel af en usikker co-infektion med ransomware og trojanske heste.
Fjernelse af Wineth-setup.exe anbefales stærkt, givet at du tager chancen for ikke kun store elomkostninger, hvis den kører på din COMPUTER, dog kan minearbejderen også udføre forskellige andre uønskede opgaver på den og også beskadige din COMPUTER permanent.
Fjernelse af Wineth-setup.exe
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knap for at fjerne Wineth-setup.exe
TRIN 5. Wineth-setup.exe fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne Wineth-setup.exe
Hvordan undgår din pc fra at blive inficeret med “Wineth-setup.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Wineth-setup.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Wineth-setup.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Wineth-setup.exe”.







