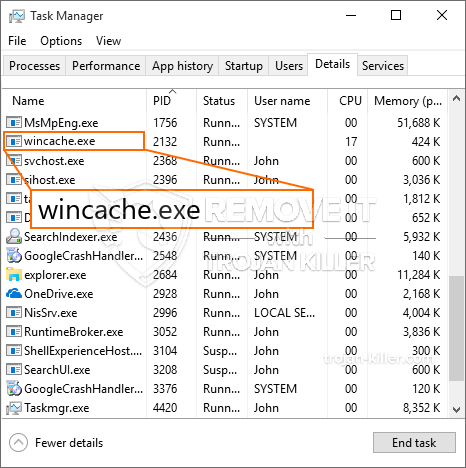
En ny, meget usikker cryptocurrency minearbejder infektion rent faktisk er blevet spottet af sikkerhedsmæssige forskere. den malware, hedder Wincache.exe kan inficere target syge anvender et udvalg af metoder. Essensen bag Wincache.exe-minearbejderen er at anvende cryptocurrency-minearbejderopgaver på de syges computere for at erhverve Monero-symboler til ofre for omkostninger. Resultatet af denne minearbejder er de forhøjede elregninger, og hvis du lader det stå i længere tid, kan Wincache.exe endda skade dine computersystemer.
Wincache.exe: distributionssystemer Metoder
Det Wincache.exe malware gør brug af 2 fremtrædende teknikker, der bruges til at kontaminere computersystemmål:
- Payload Levering hjælp Prior Infektioner. Hvis en ældre Wincache.exe-malware frigives på de sygesystemer, kan den straks opgradere sig selv eller downloade og installere en nyere version. Dette er muligt ved hjælp af den indbyggede opgradering kommando, som får lanceringen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, der tilvejebringer den Malwarekoden. Den downloadede virus får navnet på en Windows-løsning og placeres i “%Systemet% temp” areal. Vigtige bygninger såvel som køre systemarrangementsfiler ændres for at muliggøre en konsistent og stille infektion.
- Software sårbarhed udnytter. Den seneste variant af Wincache.exe-malware er faktisk blevet opdaget at være udløst af nogle ventures, almindeligvis forstås til at blive anvendt i de ransomware strikes. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som ser op hvis porten er åben. Hvis dette problem opfyldes, vil det helt sikkert tjekke løsningen og også få oplysninger om det, bestående af enhver type variation og også arrangementsdata. Ventures og også fremtrædende brugernavn samt adgangskodeblandinger kan udføres. Når udnyttelsen er forårsaget mod den modtagelige kode, vil minearbejderen helt sikkert blive frigivet ud over bagdøren. Dette vil helt sikkert give det en dobbelt infektion.
Bortset fra disse metoder kan andre strategier også gøres brug af. Gruvearbejdere kan spredes ved phishing-e-mails, der sendes i bulk på en SPAM-lignende måde og også afhænger af sociale design-tricks for at forvirre de syge lige til at tro, at de har modtaget en meddelelse fra en legit løsning eller virksomhed. Infektionsdataene kan enten forbindes lige eller sættes i kropskomponenterne i multimediemateriale eller tekstweblink.
Forbrydere kan på samme måde fremstille ondsindede destinationswebsider, der kan udvise sælgerens download og installation af websider, softwareprogrammer downloader portaler og andre områder med regelmæssigt adgang. Når de bruger sammenlignelige vises domænenavne til legit adresser såvel som sikkerheds- og sikkerhedscertifikater, tvinges brugerne ret til at kommunikere med dem. Nogle gange blot åbne dem kan modregne minearbejder infektion.
En yderligere teknik ville bestemt være at gøre brug af tjenesteudbydere af nyttelast, der kan spredes ved hjælp af disse teknikker eller gennem fildelingsnetværk, BitTorrent er blot en af de mest foretrukne dem. Det bruges regelmæssigt til at sprede både legitim softwareapplikation såvel som data såvel som piratmateriale. To af en af de mest populære træk udbydere er følgende:
Andre tilgange, som lovovertræderne kan tage i betragtning, inkluderer anvendelse af browserkaprere - farlige plugins, der er gjort kompatible med de mest populære internetbrowsere. De sendes til de relevante databaser med falske kundevurderinger og desuden designerkvalifikationer. Oftentimes oversigter kan omfatte skærmbilleder, videoklip og sofistikerede beskrivelser, der lover fremragende funktionsforbedringer såvel som præstationsoptimeringer. Ikke desto mindre vil de berørte browsers vaner bestemt ændre sig ved afbetaling- enkeltpersoner vil helt sikkert opdage, at de vil blive omdirigeret til en hacker-kontrolleret destinationswebside, og også deres opsætninger kan blive ændret – standard startside, online søgemaskine og også nye faneblade.

Wincache.exe: Analyse
Wincache.exe-malware er et traditionelt tilfælde af en kryptovaluta-minearbejder, som afhængigt af dens arrangement kan skabe en række farlige handlinger. Dets primære mål er at udføre komplekse matematiske job, der helt sikkert vil udnytte de tilgængelige systemressourcer: CPU, GPU, hukommelse og harddisk plads. Den metode, de bruger, er ved at oprette forbindelse til en speciel webserver kaldet minedrift, hvorfra den nødvendige kode downloades og installeres. Så snart blandt opgaverne er downloadet, begynder den med det samme, flere omstændigheder kan køres på en gang. Når en bestemt opgave er afsluttet, vil en helt sikkert blive downloadet og installeret på dens placering, og sløjfen vil helt sikkert fortsætte, indtil computersystemet er slukket, infektionen elimineres, eller der opstår en yderligere lignende lejlighed. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres budgetter.
En usikker kvalitet ved denne klassificering af malware er, at eksempler som denne kan tage alle systemkilder og næsten gøre offerets computersystem meningsløst, indtil faren faktisk er fuldstændig elimineret. De fleste af dem inkluderer en konsekvent opsætning, der gør dem virkelig svære at eliminere. Disse kommandoer vil helt sikkert foretage justeringer også muligheder, arrangement filer og også Windows registreringsdatabase værdier, der helt sikkert vil gøre Wincache.exe malware begynder automatisk, når computeren er tændt. Adgang til gendannelse af valg af fødevarer og alternativer kan blive blokeret, hvilket giver mange praktiske fjernelsesvejledninger næsten ineffektive.
Denne særlige infektion vil sætte en Windows-løsning for sig selv, fulgt en politik med gennemførte sikkerhed og evaluering sikkerhed ther følgende handlinger rent faktisk er blevet observeret:
. Under minearbejdsprocedurerne kan den tilknyttede malware oprette forbindelse til allerede kørende Windows-tjenester og installerede applikationer fra tredjepart. Ved at gøre det opdager systemadministratorerne muligvis ikke, at ressourcetonnerne kommer fra en separat proces.
| Navn | Wincache.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at opdage og fjerne Wincache.exe |

Denne form for malwareinfektioner er særligt effektive til at udføre sofistikerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær ramme, der gør det muligt for de kriminelle kontrollere at orkestrere al slags skadelig adfærd. Et af de foretrukne eksempler er ændringen af Windows-registreringsdatabasen – justeringsstrenge relateret til operativsystemet kan udløse store effektivitetsforstyrrelser og også manglen på evne til at få adgang til Windows-tjenester. At stole på omfanget af justeringer kan det ligeledes gøre computeren helt ubrugelig. På den anden side kan justering af Registry-værdier, der kommer fra tredjepartsmonterede applikationer, underminere dem. Nogle applikationer kan muligvis ikke frigive helt, mens andre uventet kan stoppe med at arbejde.
Denne bestemte minearbejder i sin nuværende version er fokuseret på at udtrække Monero-kryptovalutaen, der indeholder en ændret variation af XMRig CPU-minedriftmotoren. Hvis projekterne viser sig at være vellykkede, kan fremtidige versioner af Wincache.exe lanceres i fremtiden. Da malware bruger softwaresårbarheder til at inficere målværter, det kan være bestanddel af en usikker co-infektion med ransomware samt trojanske heste.
Fjernelse af Wincache.exe anbefales stærkt, da du risikerer ikke kun store strømomkostninger, hvis den kører på din COMPUTER, men minearbejderen kan også udføre forskellige andre uønskede aktiviteter på den såvel som endda skade din pc permanent.
Fjernelse af Wincache.exe
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knap for at fjerne Wincache.exe
TRIN 5. Wincache.exe fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne Wincache.exe
Hvordan undgår din pc fra at blive inficeret med “Wincache.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Wincache.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Wincache.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Wincache.exe”.







