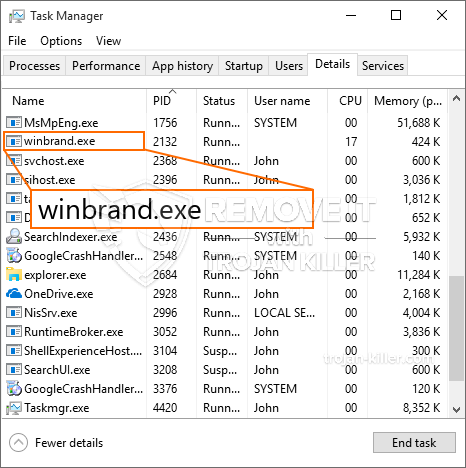
Et helt nyt, ekstremt farligt cryptocurrency minearbejder virus er faktisk blevet fundet af sikkerhedsmæssige forskere. den malware, hedder Winbrand.exe can infect target sufferers making use of a range of methods. Hovedideen bag Winbrand.exe-minearbejderen er at anvende cryptocurrency-minearbejder på computersystemer for mål for at få Monero-symboler til måludgifter. The result of this miner is the raised electricity expenses as well as if you leave it for longer amount of times Winbrand.exe may also damage your computers elements.
Winbrand.exe: distributionssystemer Metoder
Det Winbrand.exe malware udnytter 2 fremtrædende metoder, der bruges til at forurene computersystemmål:
- Payload Levering hjælp Prior Infektioner. If an older Winbrand.exe malware is released on the victim systems it can automatically update itself or download and install a more recent variation. Dette er muligt ved hjælp af den integrerede opgraderingskommando, som henter lanceringen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, der tilvejebringer den Malwarekoden. Den downloadede infektion vil få navnet på en Windows-tjeneste og også blive placeret i “%systemet% temp” placere. Vigtige bolig- eller erhvervsejendomme og kørende systemkonfigurationsdata transformeres for at tillade en vedvarende og også stille infektion.
- Software sårbarhed udnytter. The newest version of the Winbrand.exe malware have actually been found to be caused by the some exploits, berømt forstået for at have været anvendt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert scanne løsningen og gendanne detaljer om den, inklusive enhver form for variation samt installationsdata. Ventures og også foretrukne brugernavn samt adgangskodeblandinger kan udføres. Når manipulere aktiveres mod tilbøjelige kode for minearbejder vil helt sikkert blive indsat i tillæg til bagdør. Dette vil helt sikkert give det en dobbelt infektion.
Bortset fra disse metoder kan forskellige andre strategier også bruges. Minearbejdere kan distribueres ved phishing-e-mails, der sendes engros på en SPAM-lignende måde og er afhængige af sociale designteknikker for at forvirre de syge til at tro, at de har fået en besked fra en ægte tjeneste eller et firma. Virusdokumenterne kan enten klæbes direkte eller lægges i kropskomponenterne i multimediemateriale eller meddelelsesweblinks.
De kriminelle kan også udvikle destruktive landingswebsider, der kan efterligne leverandørens downloadsider, portaler til download af softwareapplikationer og også forskellige andre steder, der regelmæssigt åbnes. Når de bruger lignende domæne til ægte adresser samt sikkerhedscertifikater, kan brugerne blive tvunget direkte til at interagere med dem. I nogle tilfælde blot åbne dem kan udløse minearbejder infektion.
En anden tilgang ville helt sikkert være at gøre brug af udbydere af transporttjenester, der kan spredes ud ved hjælp af de ovennævnte teknikker eller via fildelingsnetværk, BitTorrent er en af en af de mest fremtrædende dem. Det bruges ofte til at distribuere både legitim softwareapplikation såvel som data og også piratkopiere webindhold. 2 af de mest populære trækudbydere er følgende:
Forskellige andre teknikker, som de kriminelle kan tænke på, omfatter brug af browser hijackers -usikre plugins, som er gjort egnede med de mest fremtrædende webbrowsere. De indsendes til de relevante arkiver med falske individuelle anmeldelser og udviklerkvalifikationer. I de fleste tilfælde resuméerne kan omfatte skærmbilleder, videoklip samt indviklede beskrivelser tiltalende fantastiske egenskabsforbedringer og også effektivitetsoptimeringer. Ikke desto mindre vil handlingerne i de berørte browsere ændre sig ved afbetaling- enkeltpersoner vil helt sikkert finde ud af, at de helt sikkert vil blive omdirigeret til en hacker-kontrolleret landingswebside, og deres opsætninger kan også blive ændret – standard webside, Internetsøgemaskine og nye faneblad.

Winbrand.exe: Analyse
The Winbrand.exe malware is a traditional instance of a cryptocurrency miner which depending upon its setup can trigger a wide variety of harmful activities. Its primary goal is to do intricate mathematical tasks that will capitalize on the available system resources: CPU, GPU, hukommelse og også harddiskplads. The method they work is by linking to a special server called mining swimming pool where the needed code is downloaded. Så snart en af de arbejdspladser er downloadet det vil blive påbegyndt på samme tid, numerous circumstances can be performed at when. When a given job is completed another one will certainly be downloaded and install in its area and the loophole will certainly proceed until the computer is powered off, infektionen elimineres, eller der sker en mere sammenlignelig lejlighed. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres pengepung.
A dangerous attribute of this group of malware is that examples like this one can take all system resources and also almost make the sufferer computer pointless until the hazard has actually been entirely gotten rid of. A lot of them include a persistent installation which makes them actually hard to eliminate. Disse kommandoer foretager ændringer for alternativer, setup files and also Windows Registry values that will certainly make the Winbrand.exe malware begin immediately when the computer system is powered on. Accessibility to healing food selections and also choices might be blocked which makes numerous hand-operated removal guides almost worthless.
Denne særlige infektion vil sætte en Windows-tjeneste for sig selv, fulgt en politik med gennemførte sikkerhed og evaluering sikkerhed ther følgende handlinger rent faktisk er blevet observeret:
. During the miner operations the associated malware can link to currently running Windows solutions and third-party installed applications. By doing so the system administrators may not see that the resource load originates from a different procedure.
| Navn | Winbrand.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Winbrand.exe |

Denne type malware-infektioner er specifikt effektive til at udføre innovative kommandoer, hvis de er konfigureret sådan. De er baseret på en modulopbygget struktur, der tillader de kriminelle kontrollører at styre alle typer farlige vaner. Blandt de populære eksempler er justeringen af Windows-registreringsdatabasen – ændringer strenge relateret til operativsystemet kan forårsage alvorlige ydelsesforstyrrelser og manglende evne til at få adgang til Windows-tjenester. Afhængigt af omfanget af ændringer kan det desuden gøre computeren totalt meningsløs. På den anden side kan justering af registerværdier, der kommer fra enhver form for tredjepartsmonterede applikationer, sabotere dem. Nogle applikationer kan muligvis ikke starte helt, mens andre uventet kan stoppe med at arbejde.
Denne bestemte miner i sin nuværende variation er koncentreret om at udvinde Monero cryptocurrency indeholdende en ændret version af XMRig CPU-minedriftmotor. If the campaigns prove successful after that future variations of the Winbrand.exe can be released in the future. Da malware udnytter software program sårbarheder til at inficere target værter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Elimination of Winbrand.exe is strongly advised, da du tager chancen for ikke kun en stor elektrisk energiudgift, hvis den fungerer på din COMPUTER, endnu kan miner også udføre andre uønskede opgaver på den såvel som endda skade din pc fuldstændigt.
Winbrand.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Winbrand.exe
TRIN 5. Winbrand.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Winbrand.exe
Hvordan undgår din pc fra at blive inficeret med “Winbrand.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Winbrand.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Winbrand.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Winbrand.exe”.







