Et helt nyt, virkelig usikker cryptocurrency minearbejder infektion er blevet opdaget af sikkerhedseksperter. den malware, hedder Vmicsvc.exe kan forurene målrettet på forskellige måder. Essensen bag Vmicsvc.exe minearbejder er at udnytte cryptocurrency minearbejder opgaver på computerne af ofre for at opnå Monero poletter på ofrene omkostninger. The result of this miner is the elevated electrical energy costs and also if you leave it for longer periods of time Vmicsvc.exe may also harm your computers parts.
Apart from these approaches other methods can be used too. Miners can be dispersed by phishing emails that are sent out wholesale in a SPAM-like way as well as rely on social design techniques in order to confuse the victims into thinking that they have obtained a message from a genuine solution or company. The virus documents can be either directly connected or placed in the body materials in multimedia material or message web links.
The offenders can likewise develop destructive landing pages that can impersonate supplier download and install web pages, software applikation downloade portaler og forskellige andre ofte adgang placeringer. When they utilize comparable seeming domain to legit addresses and also security certificates the users might be persuaded into communicating with them. Nogle gange kan bare åbning af dem udløse minearbejderinfektionen.
Another strategy would be to use haul providers that can be spread out utilizing the above-mentioned methods or by means of file sharing networks, BitTorrent er blot en af en af de mest foretrukne dem. It is frequently made use of to distribute both legitimate software application and data and also pirate content. To af en af de mest prominente nyttelast udbydere er følgende:
Other techniques that can be considered by the wrongdoers include making use of internet browser hijackers -unsafe plugins which are made compatible with the most prominent web browsers. They are published to the pertinent repositories with fake customer reviews as well as designer qualifications. I mange tilfælde kan resuméerne bestå af skærmbilleder, video clips and also fancy summaries promising excellent feature enhancements as well as efficiency optimizations. Nonetheless upon installation the habits of the affected web browsers will certainly alter- individuals will find that they will certainly be rerouted to a hacker-controlled landing web page and their setups may be modified – standard startside, søgemaskine på internettet samt nye faner webside.

Vmicsvc.exe: Analyse
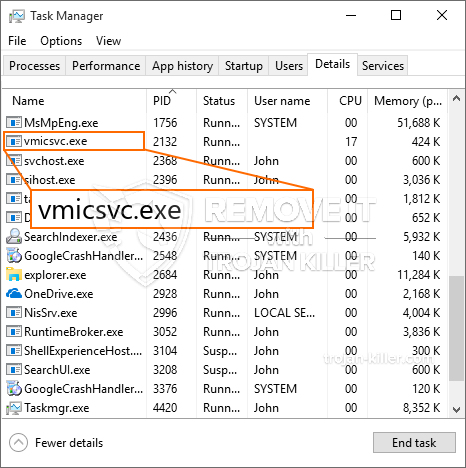
The Vmicsvc.exe malware is a classic case of a cryptocurrency miner which depending upon its setup can create a wide array of hazardous activities. Dens hovedformål er at udføre indviklede matematiske opgaver, der vil drage fordel af de let tilgængelige systemressourcer: CPU, GPU, hukommelse og også harddisk værelse. Midlet, de fungerer, er ved at linke til en unik server kaldet mining pool, hvorfra den nødvendige kode downloades og installeres. Så hurtigt som blandt jobs er downloadet, vil det helt sikkert blive startet med det samme, flere tilfælde kan være væk for en gangs skyld. Når et tilbudt job er fuldført, vil et ekstra job helt sikkert blive downloadet og installeret i dets område, og smuthullet vil helt sikkert fortsætte indtil computersystemet slukkes, infektionen fjernes, eller der sker en anden lignende hændelse. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres pengepung.
Et usikkert træk ved denne klassificering af malware er, at eksempler, der ligner denne, kan tage alle systemkilder og også næsten gøre målcomputersystemet ubrugeligt, indtil risikoen er fuldstændig fjernet. De fleste af dem inkluderer en vedvarende opsætning, der gør dem virkelig svære at fjerne. Disse kommandoer vil foretage ændringer også muligheder, setup data and Windows Registry values that will make the Vmicsvc.exe malware start immediately when the computer is powered on. Adgang til udvælgelse af genopretningsfødevarer og alternativer kan være blokeret, hvilket gør adskillige håndbetjente elimineringsoversigter praktisk talt ineffektive.
Denne specifikke infektion vil arrangementet en Windows-tjeneste for sig selv, efter den udførte sikkerhedsanalyse er følgende handlinger blevet observeret:
. Under minedriftsprocedurerne kan den tilknyttede malware linke til aktuelt kørende Windows-tjenester og også installerede tredjepartsapplikationer. Dermed observerer systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en separat procedure.
| Navn | Vmicsvc.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Vmicsvc.exe |

These type of malware infections are specifically reliable at performing innovative commands if configured so. They are based upon a modular structure permitting the criminal controllers to manage all type of harmful behavior. Et af de fremtrædende tilfælde er ændringen af Windows-registreringsdatabasen – modifications strings connected by the operating system can create serious performance interruptions and the inability to accessibility Windows solutions. Relying on the extent of changes it can likewise make the computer system entirely pointless. På den anden side kan manipulation af registreringsværdier, der tilhører tredjeparts installerede applikationer, underminere dem. Some applications may stop working to launch completely while others can suddenly stop working.
This certain miner in its current version is concentrated on mining the Monero cryptocurrency having a customized version of XMRig CPU mining engine. If the projects show effective after that future versions of the Vmicsvc.exe can be released in the future. Da malware udnytter software program susceptabilities at inficere target værter, det kan være en del af en usikker co-infektion med ransomware og også trojanske heste.
Elimination of Vmicsvc.exe is strongly recommended, because you run the risk of not just a huge electrical power bill if it is working on your PC, but the miner may also carry out other undesirable tasks on it and also damage your PC permanently.
Vmicsvc.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Vmicsvc.exe
TRIN 5. Vmicsvc.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Vmicsvc.exe
Hvordan undgår din pc fra at blive inficeret med “Vmicsvc.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Vmicsvc.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Vmicsvc.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Vmicsvc.exe”.







