En ny, virkelig farligt cryptocurrency minearbejder infektion rent faktisk er blevet spottet af sikkerhedsmæssige forskere. den malware, hedder UcSvc.exe kan forurene målsyge ved brug af en række midler. Hovedideen bag UcSvc.exe-minearbejderen er at bruge cryptocurrency-minearbejderopgaver på ofrenes computere for at få Monero-symboler til målomkostninger. The end result of this miner is the raised electricity expenses as well as if you leave it for longer amount of times UcSvc.exe might also harm your computer systems parts.
UcSvc.exe: distributionssystemer Metoder
Det UcSvc.exe malware gør brug af 2 popular methods which are made use of to contaminate computer system targets:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older UcSvc.exe malware is released on the sufferer systems it can instantly update itself or download and install a newer version. This is possible through the integrated update command which gets the release. Dette gøres ved at oprette forbindelse til en bestemt foruddefineret hackerstyret server, der tilbyder malware-koden. The downloaded and install virus will certainly acquire the name of a Windows solution and be positioned in the “%Systemet% temp” Beliggenhed. Important homes and also running system arrangement documents are altered in order to allow a relentless and also silent infection.
- Software sårbarhed udnytter. The latest version of the UcSvc.exe malware have actually been located to be brought on by the some exploits, populært anerkendt for at blive udnyttet i ransomware overfald. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som søger efter hvis porten er åben. If this problem is fulfilled it will scan the service as well as get information about it, consisting of any kind of variation as well as setup data. Ventures såvel som populære kombinationer af brugernavn og adgangskode kan udføres. When the make use of is activated versus the vulnerable code the miner will be released together with the backdoor. Dette vil helt sikkert give en dobbelt infektion.
Aside from these techniques other methods can be made use of also. Miners can be distributed by phishing e-mails that are sent out wholesale in a SPAM-like way as well as depend on social design techniques in order to perplex the sufferers right into thinking that they have obtained a message from a genuine solution or business. Virussdokumenterne kan enten være direkte påsat eller anbragt i kropsindholdet i multimediemateriale eller weblink til meddelelser.
The lawbreakers can likewise produce malicious touchdown pages that can pose supplier download and install pages, software download websites as well as various other frequently accessed locations. When they make use of similar sounding domain names to reputable addresses and also safety and security certifications the individuals may be coerced right into engaging with them. I nogle tilfælde blot at åbne dem kan modregne minearbejder infektion.
One more approach would be to utilize payload carriers that can be spread using the above-mentioned methods or by means of documents sharing networks, BitTorrent er en af en af de mest fremtrædende dem. It is frequently used to disperse both legitimate software as well as data as well as pirate content. 2 af en af de mest foretrukne nyttelast tjenesteydere er følgende:
Various other techniques that can be thought about by the lawbreakers include making use of web browser hijackers -harmful plugins which are made compatible with the most prominent internet browsers. They are published to the appropriate repositories with fake individual evaluations and also programmer qualifications. In many cases the summaries may consist of screenshots, videos and sophisticated summaries promising fantastic attribute improvements and also performance optimizations. Nevertheless upon installation the habits of the influenced web browsers will alter- customers will certainly find that they will be rerouted to a hacker-controlled touchdown web page and also their setups may be modified – standard webside, online søgemaskine og også helt nye side faner.

UcSvc.exe: Analyse
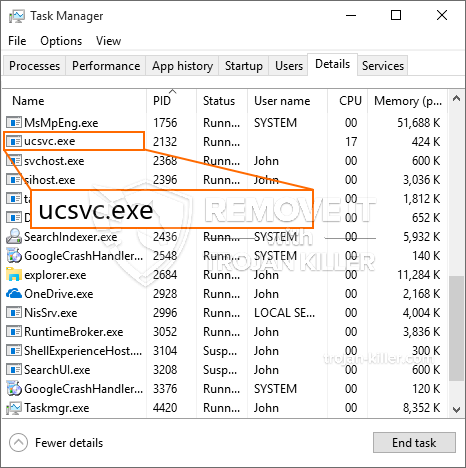
The UcSvc.exe malware is a traditional situation of a cryptocurrency miner which relying on its arrangement can create a wide range of harmful activities. Its major goal is to do intricate mathematical tasks that will certainly benefit from the available system resources: CPU, GPU, hukommelse såvel som harddiskområdet. The method they work is by connecting to a special web server called mining swimming pool where the called for code is downloaded. As quickly as one of the jobs is downloaded it will be begun simultaneously, flere forekomster kan køres på én gang. When a given task is finished an additional one will certainly be downloaded and install in its place as well as the loophole will certainly continue until the computer is powered off, infektionen fået fjernet eller en mere sammenlignelige lejlighed sker. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres punge.
A harmful characteristic of this classification of malware is that examples like this one can take all system sources as well as virtually make the sufferer computer unusable until the danger has actually been entirely eliminated. Most of them feature a relentless installment that makes them truly tough to get rid of. Disse kommandoer foretager ændringer i startindstillinger, setup documents and also Windows Registry values that will make the UcSvc.exe malware beginning immediately when the computer system is powered on. Access to recovery food selections as well as alternatives might be obstructed which makes numerous hand-operated removal guides almost pointless.
Denne specifikke infektion vil konfigurationshåndtering en Windows-tjeneste for sig selv, complying with the carried out security evaluation ther adhering to activities have actually been observed:
. During the miner operations the connected malware can hook up to already running Windows solutions and also third-party mounted applications. By doing so the system managers may not discover that the source lots comes from a different process.
| Navn | UcSvc.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove UcSvc.exe |

Disse slags malware infektioner er særligt pålidelige på at udføre avancerede kommandoer, hvis sat op, så. De er baseret på en modulær ramme gør det muligt for kriminelle controllere at orkestrere alle former for skadelige vaner. Et af de populære eksempler er justeringen af Windows-registreringsdatabasen – justeringer strenge forbundet af operativsystemet kan udløse betydelige effektiviseringer forstyrrelser og også den manglende adgang til Windows-tjenester. Afhængig af omfanget af tilpasninger, som den kan ligeledes gøre computeren helt ubrugelig. På den anden side manipulation af Registry værdier, der kommer fra en hvilken som helst tredjepart kan installerede programmer underminere dem. Nogle programmer kan falde kort til at lancere helt, mens andre uventet kan afslutte arbejdet.
Denne særlige minearbejder i sin nuværende variation er fokuseret på at udvinde den Monero cryptocurrency har en modificeret udgave af XMRig CPU minedrift motor. If the campaigns show effective after that future versions of the UcSvc.exe can be released in the future. Da de malware gør brug af software program sårbarheder til at inficere target værter, det kan være bestanddel af en farlig co-infektion med ransomware og trojanske heste.
Removal of UcSvc.exe is strongly suggested, fordi du tager chancen for ikke blot en enorm elektrisk strøm regningen, hvis det kører på din computer, endnu minearbejder kan også udføre forskellige andre uønskede opgaver på det og også skade din computer permanent.
UcSvc.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove UcSvc.exe
TRIN 5. UcSvc.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove UcSvc.exe
Hvordan undgår din pc fra at blive inficeret med “UcSvc.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “UcSvc.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “UcSvc.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “UcSvc.exe”.







