Et helt nyt, virkelig farlig kryptokurrency minearbejde er faktisk blevet set af sikkerhedsforskere. den malware, hedder Time.exe can infect target sufferers utilizing a variety of means. Hovedideen bag Time.exe-minearbejderen er at udnytte cryptocurrency-minearbejdere på syges computersystemer for at få Monero-symboler på ofrenes bekostning. The outcome of this miner is the elevated power bills and if you leave it for longer time periods Time.exe may even damage your computers components.
Time.exe: distributionssystemer Metoder
Det Time.exe malware bruger to populære metoder, der anvendes til forurene edb-system mål:
- Payload Levering gennem Prior Infektioner. If an older Time.exe malware is released on the target systems it can instantly update itself or download a newer variation. Dette er muligt via den integrerede opdateringskommando, som henter udgivelsen. Dette gøres ved at knytte sig til en specifik foruddefineret hacker-styret webserver, som tilbyder malware-koden. Den downloadede og installere infektion vil helt sikkert få navnet på en Windows-tjeneste og også blive sat i “%systemet% temp” Beliggenhed. Væsentlige boligejendomme og også kørende systemkonfigurationsdata transformeres for at tillade en vedvarende og også stille infektion.
- Software Application sårbarhed udnytter. The most current version of the Time.exe malware have actually been discovered to be brought on by the some exploits, populært forstået for at blive brugt i ransomware strejker. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Overgrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis dette problem er opfyldt, vil det scanne løsningen samt hente information om det, inklusive enhver form for version samt opsætningsdata. Udnyttelse og fremtrædende brugernavn og også adgangskodeblandinger kan udføres. Når manipulationen udløses mod den tilbøjelige kode, vil minearbejderen blive indsat ud over bagdøren. Dette vil helt sikkert give det en dobbelt infektion.
Ud over disse teknikker kan forskellige andre metoder også bruges. Minearbejdere kan spredes ved phishing-e-mails, der sendes ud i bulk på en SPAM-lignende måde og er afhængige af sociale design-tricks for at pusle ofrene lige til at tro, at de har fået en besked fra en legitim tjeneste eller virksomhed. Infektionsfilerne kan enten forbindes direkte eller lægges i kropskomponenterne i multimedieindhold eller tekstweblinks.
De lovovertrædere kan desuden oprette ondsindede landingswebsider, der kan udgøre leverandørens download- og installationssider, websteder til download af software og forskellige andre hyppigt tilgåede områder. Når de bruger lignende domænenavne til ægte adresser samt sikkerhedscertificeringer, kan brugerne blive skubbet til at oprette forbindelse til dem. Nogle gange kan blot åbning af dem forårsage minerinfektionen.
En anden metode ville helt sikkert være at gøre brug af udbydere af transporttjenester, der kan spredes ved hjælp af de ovennævnte teknikker eller ved hjælp af fildelingsnetværk, BitTorrent er blandt en af de mest populære. Det bliver ofte brugt til at sprede både velrenommeret software og dokumenter samt piratindhold. To af de mest fremtrædende nyttelastudbydere er følgende:
Andre teknikker, der kan tænkes over af synderne, består i at gøre brug af browser hijackers - farlige plugins, som er gjort kompatible med de mest populære webbrowsere. De sendes til de relevante depoter med falske kundeanmeldelser samt designerlegitimationsoplysninger. I mange tilfælde resuméerne kan bestå af screenshots, videoer samt smarte resuméer, der tilskynder til fantastiske funktionsforbedringer og ydeevneoptimeringer. Men ved installationen vil vanerne for de berørte webbrowsere helt sikkert ændre sig- kunder vil helt sikkert opdage, at de helt sikkert vil blive omdirigeret til en hacker-kontrolleret landingsside, og deres opsætninger kan også blive ændret – standard startside, online søgemaskine samt helt nye faner side.

Time.exe: Analyse
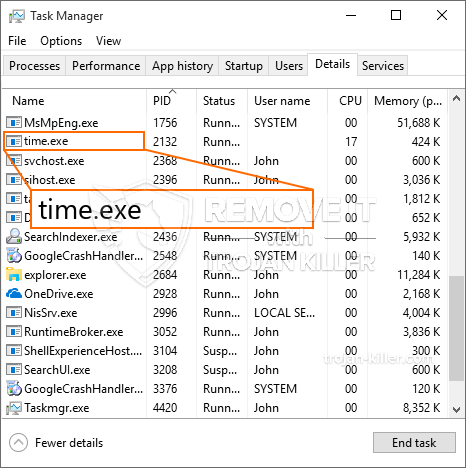
The Time.exe malware is a traditional situation of a cryptocurrency miner which depending on its configuration can trigger a variety of harmful actions. Its major objective is to perform complex mathematical jobs that will take advantage of the available system resources: CPU, GPU, hukommelse og harddisk plads. The means they function is by attaching to a special server called mining swimming pool where the called for code is downloaded. Så hurtigt som et af job downloades, startes det samtidig, flere tilfælde kan køres på en gang. When a given job is completed another one will certainly be downloaded and install in its place and also the loophole will continue up until the computer is powered off, infektionen fået fjernet eller en mere ens lejlighed sker. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres pengepung.
A hazardous feature of this classification of malware is that examples like this one can take all system sources and also almost make the target computer system pointless up until the threat has actually been completely eliminated. Most of them include a consistent installment which makes them truly tough to eliminate. Disse kommandoer vil helt sikkert gøre ændringer også valg, configuration documents as well as Windows Registry values that will certainly make the Time.exe malware beginning instantly as soon as the computer system is powered on. Accessibility to healing food selections as well as choices may be blocked which provides many manual removal guides practically ineffective.
Denne særlige infektion vil sætte en Windows-løsning for sig selv, adhering to the performed security evaluation ther following actions have been observed:
. During the miner procedures the connected malware can connect to currently running Windows services and third-party set up applications. By doing so the system administrators might not see that the resource load originates from a different procedure.
| Navn | Time.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Time.exe |

These kind of malware infections are particularly effective at carrying out sophisticated commands if configured so. They are based upon a modular structure enabling the criminal controllers to orchestrate all sort of hazardous actions. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – modifications strings related by the operating system can create significant efficiency interruptions and the inability to gain access to Windows solutions. Depending on the scope of changes it can also make the computer completely unusable. On the various other hand manipulation of Registry values belonging to any kind of third-party installed applications can sabotage them. Some applications may fail to release altogether while others can unexpectedly quit working.
This specific miner in its current version is focused on mining the Monero cryptocurrency having a modified version of XMRig CPU mining engine. If the campaigns verify effective then future variations of the Time.exe can be launched in the future. Da malware anvender softwareprogramsårbarheder til at forurene målværter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Elimination of Time.exe is strongly recommended, given that you run the risk of not only a large power expense if it is working on your COMPUTER, yet the miner might additionally execute various other unwanted tasks on it and also harm your PC permanently.
Time.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Time.exe
TRIN 5. Time.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Time.exe
Hvordan undgår din pc fra at blive inficeret med “Time.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Time.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Time.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Time.exe”.







