En ny, virkelig farlig kryptokurrency-minearbejdervirus er blevet identificeret af sikkerhedsforskere. den malware, hedder SystemATI can infect target victims using a range of ways. Hovedpointen bag SystemATI-minearbejderen er at bruge kryptokurrency-minearbejdsaktiviteter på syges computersystemer for at få Monero-tokens til syge udgifter. The end result of this miner is the raised power expenses and also if you leave it for longer periods of time SystemATI may also harm your computers elements.
SystemATI: distributionssystemer Metoder
Det SystemATI malware udnytter 2 populære tilgange, der bruges til at forurene computersystemmål:
- Payload Levering gennem Prior Infektioner. If an older SystemATI malware is released on the sufferer systems it can immediately update itself or download a more recent variation. Dette er muligt via den indbyggede opgraderingskommando, der får lanceringen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, som leverer malware kode. The downloaded and install virus will obtain the name of a Windows service and be positioned in the “%systemet% temp” placere. Vital residential or commercial properties and also running system arrangement documents are changed in order to allow a persistent and quiet infection.
- Software sårbarhed udnytter. The most recent version of the SystemATI malware have been located to be caused by the some ventures, berømt forstås til at blive anvendt i ransomware strikes. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Angrebene er automatiseret af en hacker-kontrollerede rammer, som søger efter, hvis porten er åben. If this condition is satisfied it will certainly scan the solution as well as recover details about it, including any type of version and arrangement information. Exploits as well as popular username and password combinations may be done. When the exploit is set off versus the vulnerable code the miner will be released along with the backdoor. Dette vil give den en dobbelt infektion.
Apart from these methods other techniques can be used also. Miners can be dispersed by phishing e-mails that are sent out wholesale in a SPAM-like way and rely on social engineering tricks in order to perplex the targets into believing that they have obtained a message from a legitimate service or business. The virus data can be either directly connected or placed in the body contents in multimedia web content or message web links.
The criminals can also produce harmful touchdown pages that can impersonate vendor download and install pages, software download portals as well as various other regularly accessed areas. When they use comparable seeming domain names to genuine addresses and safety certifications the individuals might be pushed right into connecting with them. I nogle tilfælde kan blot åbning af dem forårsage minearbejdsinfektion.
One more strategy would be to use payload service providers that can be spread making use of the above-mentioned techniques or using data sharing networks, BitTorrent er blandt en af de mest populære. It is often utilized to disperse both reputable software program and also data and also pirate content. To af de mest foretrukne nyttelastudbydere er følgende:
Various other techniques that can be considered by the lawbreakers consist of the use of web browser hijackers -unsafe plugins which are made compatible with one of the most prominent internet browsers. They are posted to the relevant repositories with fake customer testimonials and developer credentials. I mange tilfælde kan beskrivelserne bestå af skærmbilleder, video clips and also fancy summaries promising fantastic feature enhancements and also efficiency optimizations. Nevertheless upon installation the actions of the impacted internet browsers will change- individuals will discover that they will certainly be rerouted to a hacker-controlled landing page as well as their settings might be modified – standard webside, søgemaskine på internettet samt nye faner webside.
SystemATI: Analyse
The SystemATI malware is a classic case of a cryptocurrency miner which relying on its setup can cause a wide variety of hazardous activities. Its main objective is to do complex mathematical jobs that will capitalize on the available system resources: CPU, GPU, hukommelse samt harddisk plads. Den måde, de fungerer på, er ved at linke til en unik webserver kaldet mining pool, hvorfra den kaldte kode downloades og installeres. As quickly as among the tasks is downloaded it will be begun at the same time, flere omstændigheder kan køres på en gang. When an offered job is finished an additional one will certainly be downloaded in its area and also the loophole will proceed till the computer is powered off, infektionen elimineres eller sker anden sammenlignelig begivenhed. Cryptocurrency vil blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres punge.
A harmful attribute of this classification of malware is that samples such as this one can take all system sources and virtually make the sufferer computer system unusable till the hazard has been completely gotten rid of. A lot of them feature a persistent installation which makes them really challenging to get rid of. Disse kommandoer vil foretage ændringer også alternativer, configuration documents and Windows Registry values that will make the SystemATI malware begin instantly when the computer is powered on. Access to healing food selections and choices might be obstructed which renders many manual removal overviews virtually worthless.
Denne særlige infektion vil bestemt konfigurere en Windows-tjeneste for sig selv, complying with the conducted protection analysis ther adhering to activities have been observed:
. During the miner procedures the associated malware can link to already running Windows services as well as third-party installed applications. By doing so the system managers might not observe that the resource lots originates from a separate process.
| Navn | SystemATI |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove SystemATI |
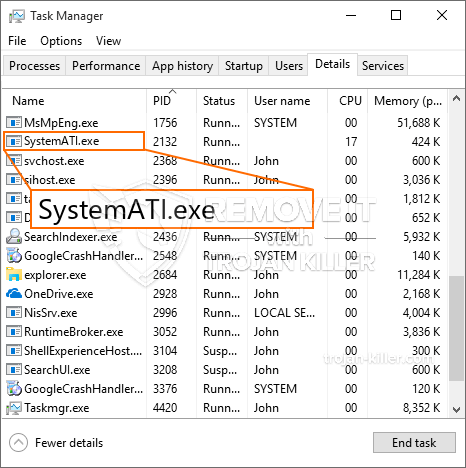
id =”82046″ align =”aligncenter” width =”600″] SystemATI
SystemATI
These sort of malware infections are specifically efficient at performing sophisticated commands if set up so. They are based on a modular framework allowing the criminal controllers to manage all type of hazardous habits. Et af de fremtrædende eksempler er ændringen af Windows-registreringsdatabasen – alterations strings associated by the operating system can cause significant efficiency disruptions and also the lack of ability to gain access to Windows services. Depending on the extent of modifications it can also make the computer completely pointless. På den anden side kan manipulation af registreringsværdier, der hører til tredjeparts opsatte applikationer, sabotere dem. Some applications may fall short to launch entirely while others can unexpectedly stop working.
This specific miner in its present version is concentrated on mining the Monero cryptocurrency containing a changed version of XMRig CPU mining engine. If the projects prove successful then future variations of the SystemATI can be released in the future. Da malware udnytter sårbarheder i software til at inficere target værter, det kan være en del af en farlig co-infektion med ransomware samt trojanske heste.
Elimination of SystemATI is strongly advised, given that you run the risk of not just a big power costs if it is operating on your PC, however the miner might also execute various other undesirable activities on it and also harm your PC completely.
SystemATI removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove SystemATI
TRIN 5. SystemATI Removed!
Video guide: How to use GridinSoft Anti-Malware for remove SystemATI
Hvordan undgår din pc fra at blive inficeret med “SystemATI” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “SystemATI”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “SystemATI”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “SystemATI”.