Et helt nyt, ekstremt farligt cryptocurrency minearbejder virus er blevet opdaget af sikkerhed og sikring forskere. den malware, hedder Scsktsvc.exe kan inficere target syge ved hjælp af forskellige måder. The main point behind the Scsktsvc.exe miner is to employ cryptocurrency miner tasks on the computer systems of targets in order to obtain Monero tokens at sufferers expenditure. The result of this miner is the elevated electrical power costs and also if you leave it for longer amount of times Scsktsvc.exe might also damage your computers parts.
Scsktsvc.exe: distributionssystemer Metoder
Det Scsktsvc.exe malware udnytter 2 prominente tilgange, som anvendes til at forurene edb-mål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Scsktsvc.exe malware is released on the sufferer systems it can instantly upgrade itself or download a more recent variation. Dette er muligt ved hjælp af den indbyggede opdateringskommando, som får frigivelsen. Dette gøres ved at binde til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. The downloaded and install infection will get the name of a Windows service as well as be put in the “%systemet% temp” areal. Essential homes and also operating system configuration data are transformed in order to allow a relentless as well as quiet infection.
- Software Application sårbarhed udnytter. The latest version of the Scsktsvc.exe malware have been discovered to be triggered by the some ventures, widely understood for being utilized in the ransomware assaults. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Angrebene automatiseres af en hacker-kontrolleret struktur, der ser op, hvis porten er åben. If this problem is satisfied it will certainly check the service and obtain information regarding it, bestående af enhver form for versionen samt konfigurationsdata. Udnyttelser og fremtrædende brugernavn og også adgangskodeblandinger kan gøres. When the exploit is triggered against the at risk code the miner will certainly be released along with the backdoor. Dette vil helt sikkert give det en dobbelt infektion.
Apart from these methods various other strategies can be utilized as well. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like manner and also rely on social engineering tricks in order to confuse the sufferers into thinking that they have gotten a message from a legitimate service or firm. The infection files can be either straight affixed or placed in the body components in multimedia content or message web links.
The criminals can additionally create malicious landing pages that can pose vendor download and install web pages, software download sites and also other often accessed places. When they use comparable seeming domain names to genuine addresses as well as security certificates the users may be persuaded right into interacting with them. I mange tilfælde blot åbne dem kan modregne minearbejder infektion.
One more approach would certainly be to make use of haul providers that can be spread using the above-mentioned techniques or via documents sharing networks, BitTorrent er blandt en af de mest populære. It is regularly utilized to disperse both reputable software application and files and also pirate content. To af en af de mest foretrukne leverandører af nyttelast er følgende:
Other techniques that can be taken into consideration by the crooks consist of making use of web browser hijackers -hazardous plugins which are made suitable with the most preferred web browsers. They are uploaded to the appropriate databases with fake customer evaluations and designer qualifications. Ofte kan beskrivelserne bestå af skærmbilleder, video clips as well as elaborate summaries appealing fantastic feature enhancements and also efficiency optimizations. However upon installation the habits of the influenced web browsers will change- customers will locate that they will be rerouted to a hacker-controlled touchdown web page and also their settings may be altered – standard webside, online søgemaskine og nye faner side.
Scsktsvc.exe: Analyse
The Scsktsvc.exe malware is a timeless instance of a cryptocurrency miner which relying on its configuration can create a wide range of harmful activities. Its main objective is to do intricate mathematical jobs that will certainly make the most of the readily available system sources: CPU, GPU, hukommelse og også harddisk område. The means they function is by attaching to a special server called mining swimming pool from where the called for code is downloaded. Så hurtigt som blandt opgaverne bliver downloadet det vil blive startet på en gang, flere omstændigheder kan være væk én gang. When an offered task is finished an additional one will be downloaded in its place and the loop will continue till the computer system is powered off, infektionen elimineres, eller der opstår en yderligere lignende lejlighed. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking team eller en enkelt hacker) direkte til deres punge.
A hazardous feature of this classification of malware is that samples similar to this one can take all system sources and practically make the sufferer computer system pointless till the threat has actually been completely removed. Most of them feature a persistent setup that makes them really challenging to remove. Disse kommandoer vil helt sikkert foretage ændringer også alternativer, setup data and Windows Registry values that will certainly make the Scsktsvc.exe malware begin instantly once the computer is powered on. Accessibility to recovery menus and options might be obstructed which makes lots of manual elimination overviews practically ineffective.
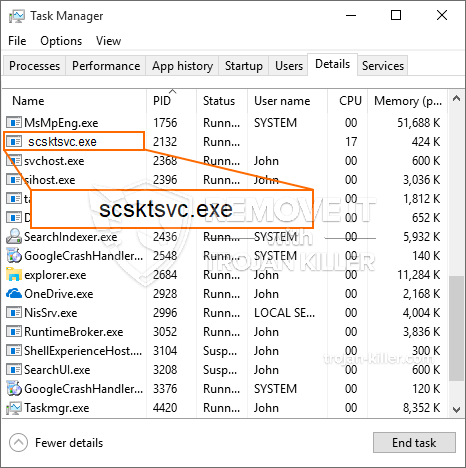
Denne specifikke infektion vil arrangementet en Windows løsning for sig selv, following the performed protection analysis ther complying with actions have actually been observed:
. During the miner operations the connected malware can hook up to currently running Windows solutions and third-party installed applications. By doing so the system administrators may not notice that the source tons originates from a different process.
| Navn | Scsktsvc.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Scsktsvc.exe |
id =”81504″ align =”aligncenter” width =”600″]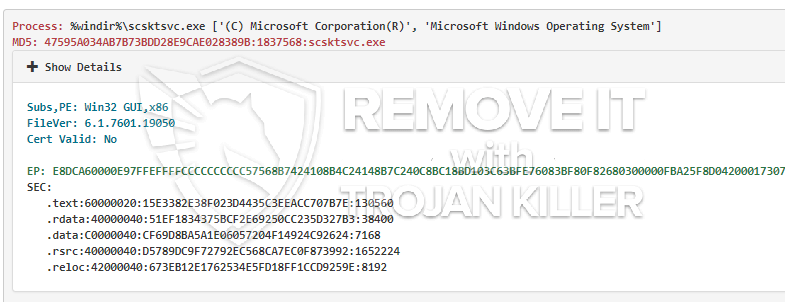 Scsktsvc.exe
Scsktsvc.exe
Denne form for malware-infektioner er især effektive til at udføre innovative kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der gør det muligt for de kriminelle controllere at orkestrere alle former for usikre handlinger. Blandt de populære eksempler er justeringen af Windows-registreringsdatabasen – ændringer strenge forbundet med operativsystemet kan udløse alvorlige effektivitetsforstyrrelser og også manglende evne til at få adgang til Windows-løsninger. Afhængig af rækkevidden af justeringer kan det ligeledes gøre computeren helt ubrugelig. På de forskellige gengæld justering af Registry worths kommer fra en hvilken som helst tredjepart kan installerede programmer underminere dem. Nogle applikationer kan undlade at frigive helt, mens andre pludselig kan stoppe med at arbejde.
Denne særlige minearbejder i sin nuværende variation er koncentreret om at udvinde Monero-kryptovalutaen, der indeholder en modificeret variation af XMRig CPU-minedriftmotoren. If the campaigns verify successful after that future versions of the Scsktsvc.exe can be launched in the future. Da malware bruger softwareapplikationssårbarheder til at inficere målværter, det kan være en del af en farlig co-infektion med ransomware og trojanske heste.
Removal of Scsktsvc.exe is strongly recommended, i betragtning af at du ikke kun risikerer enorme elektriske energiomkostninger, hvis den fungerer på din COMPUTER, alligevel kan minearbejderen også gøre forskellige andre uønskede aktiviteter på den og også endda skade din COMPUTER fuldstændigt.
Scsktsvc.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Scsktsvc.exe
TRIN 5. Scsktsvc.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Scsktsvc.exe
Hvordan undgår din pc fra at blive inficeret med “Scsktsvc.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Scsktsvc.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Scsktsvc.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Scsktsvc.exe”.