Et helt nyt, der er fundet meget farlig cryptocurrency miner-infektion af sikkerhedsforskere. den malware, hedder Nvcpl.exe kan inficere ofre mål udnytte en række forskellige midler. Essensen bag Nvcpl.exe-miner er at bruge cryptocurrency miner-opgaver på computersystemer for syge for at få Monero-tokens på målomkostning. The result of this miner is the raised power costs and if you leave it for longer periods of time Nvcpl.exe may also harm your computers components.
Nvcpl.exe: distributionssystemer Metoder
Det Nvcpl.exe malware udnytter 2 foretrukne fremgangsmåder, der er gjort brug af at forurene computer mål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Nvcpl.exe malware is released on the target systems it can instantly update itself or download a newer version. Dette er muligt ved hjælp af den indbyggede opgraderingskommando, der får frigivelsen. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den downloadede infektion får navnet på en Windows-tjeneste og placeres i “%systemet% temp” Beliggenhed. Vigtige boligejendomme og kørende systemkonfigurationsdokumenter ændres for at tillade en vedvarende og også stille infektion.
- Software Application sårbarhed udnytter. The latest variation of the Nvcpl.exe malware have been found to be triggered by the some ventures, bredt anerkendt for at have været anvendt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. Hvis denne betingelse er opfyldt, vil den bestemt scanne tjenesten såvel som hente oplysninger om den, inklusive enhver variation og konfigurationsinformation. Udnyttelse og populære brugernavn og også adgangskodekombinationer kan udføres. Når brugen er forårsaget af den sårbare kode, bliver gruvearbejderen installeret sammen med bagdøren. Dette vil helt sikkert præsentere en dobbelt infektion.
Bortset fra disse teknikker kan andre teknikker også anvendes. Gruvearbejdere kan distribueres ved phishing-e-mails, der sendes i bulk på en SPAM-lignende måde, samt afhænge af socialtekniske tricks for at forvirre de syge til at tro, at de har fået en besked fra en legitim løsning eller virksomhed. Virusfilerne kan enten forbindes direkte eller indsættes i kropsindholdet i multimediemateriale eller tekstweblink.
Forbrydere kan ligeledes producere skadelige touchdown-websider, der kan udgøre download-sider til leverandører, software-downloadwebsteder og andre ofte tilgængelige placeringer. Når de bruger lignende klingende domænenavne som legitime adresser og sikkerheds- og sikkerhedscertifikater, kan brugerne blive skubbet ret til at engagere sig med dem. Nogle gange blot åbne dem kan modregne minearbejder infektion.
En yderligere teknik ville helt sikkert være at anvende transportudbydere, der kan spredes ved hjælp af disse fremgangsmåder eller gennem netværk til deling af dokumenter, BitTorrent er blot en af en af de mest fremtrædende dem. Det bruges regelmæssigt til at sprede både velrenommeret software og også data såvel som piratindhold. To af en af de mest prominente haul luftfartsselskaber er følgende:
Forskellige andre metoder, som de dårlige fyre kan tænke på, inkluderer brug af internetbrowser-kaprere - skadelige plugins, der er gjort kompatible med en af de mest fremtrædende internetbrowsere. De indsendes til de relevante databaser med falske brugeranmeldelser og udviklerkvalifikationer. I de fleste tilfælde beskrivelserne kan omfatte skærmbilleder, videoer og smarte resume, der lover store funktionsforbedringer og ydeevneoptimeringer. Imidlertid ændres handlingerne fra de påvirkede webbrowsere ved afbetaling- brugere vil opdage, at de vil blive omdirigeret til en hacker-kontrolleret touchdown-webside, og deres opsætninger kan blive ændret – standard startside, søgemaskine og også nye faner webside.

Nvcpl.exe: Analyse
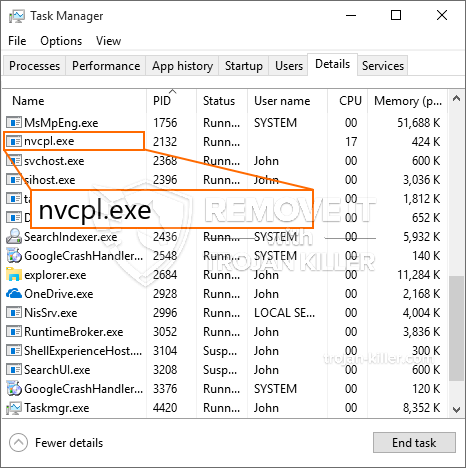
The Nvcpl.exe malware is a timeless instance of a cryptocurrency miner which depending on its configuration can trigger a variety of dangerous actions. Dets hovedmål er at udføre indviklede matematiske opgaver, der helt sikkert vil drage fordel af de tilgængelige systemkilder: CPU, GPU, hukommelse og harddisk plads. Den metode, de arbejder, er ved at oprette forbindelse til en speciel webserver kaldet minedrift, hvorfra den nødvendige kode downloades. Så snart en af opgaverne er downloadet det vil blive startet på en gang, talrige tilfælde kan udføres på en gang. Når et givent job er færdigt, vil en yderligere blive downloadet og installeret i stedet, og sløjfen fortsætter, indtil computersystemet er slukket, infektionen fjernes, eller der forekommer en yderligere sammenlignelig lejlighed. Cryptocurrency vil blive kompenseret for de kriminelle controllere (hacking team eller en enkelt hacker) lige til deres budgetter.
Et skadeligt træk ved denne klassificering af malware er, at prøver som denne kan tage alle systemressourcer samt næsten gøre offerets computersystem meningsløst, indtil faren er fjernet fuldstændigt. Mange af dem inkluderer en ubarmhjertig rate, der gør dem virkelig udfordrende at slippe af med. Disse kommandoer vil helt sikkert gøre ændringer til at starte optioner, setup documents and also Windows Registry values that will certainly make the Nvcpl.exe malware begin automatically when the computer system is powered on. Tilgængelighed til valg af rekreative fødevarer og også valg kan være hindret, hvilket gør masser af manuelle fjernelsesguider næsten meningsløse.
Denne særlige infektion konfigurerer en Windows-løsning for sig selv, overholdelse af den udførte beskyttelsesanalyse, hvor følgende aktiviteter faktisk er blevet observeret:
. Under minearbejderne kan den tilknyttede malware linke til aktuelt kørende Windows-tjenester og tredjeparts opsatte applikationer. Dermed observerer systemadministratorerne muligvis ikke, at ressourcepartierne kommer fra en anden procedure.
| Navn | Nvcpl.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Nvcpl.exe |

These kind of malware infections are especially reliable at executing sophisticated commands if set up so. They are based upon a modular framework allowing the criminal controllers to coordinate all sort of hazardous behavior. Et af de populære forekomster er justeringen af registreringsdatabasen i Windows – adjustments strings connected by the os can trigger major performance disturbances and also the inability to gain access to Windows solutions. Relying on the extent of changes it can additionally make the computer entirely pointless. On the various other hand adjustment of Registry values belonging to any kind of third-party installed applications can undermine them. Some applications might stop working to launch entirely while others can unexpectedly quit working.
This particular miner in its current variation is concentrated on mining the Monero cryptocurrency consisting of a changed version of XMRig CPU mining engine. If the projects prove effective after that future versions of the Nvcpl.exe can be released in the future. Da malware udnytter software ansøgning susceptabilities at inficere target værter, det kan være en del af et farligt co-infektion med ransomware samt trojanske heste.
Removal of Nvcpl.exe is strongly advised, because you take the chance of not only a huge electrical energy expense if it is running on your COMPUTER, however the miner might likewise execute various other unwanted tasks on it as well as even harm your COMPUTER completely.
Nvcpl.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Nvcpl.exe
TRIN 5. Nvcpl.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Nvcpl.exe
Hvordan undgår din pc fra at blive inficeret med “Nvcpl.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Nvcpl.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Nvcpl.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Nvcpl.exe”.







