Et helt nyt, meget skadeligt cryptocurrency minearbejder infektion har faktisk blevet fundet af sikkerhed og sikring forskere. den malware, hedder Ntoskrn.exe kan inficere målofre ved hjælp af en række metoder. Hovedpointen bag Ntoskrn.exe-minearbejderen er at udnytte cryptocurrency-minearbejderopgaver på de syges computere for at få Monero-tokens til målomkostninger. The end result of this miner is the elevated electricity expenses and also if you leave it for longer periods of time Ntoskrn.exe may even damage your computer systems parts.
Ntoskrn.exe: distributionssystemer Metoder
Det Ntoskrn.exe malware udnytter 2 preferred techniques which are made use of to contaminate computer targets:
- Payload Levering gennem Prior Infektioner. If an older Ntoskrn.exe malware is released on the target systems it can automatically update itself or download and install a newer version. This is possible through the integrated update command which acquires the release. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, som giver malware kode. The downloaded and install infection will acquire the name of a Windows solution and also be positioned in the “%systemet% temp” placere. Essential residential or commercial properties as well as running system setup files are altered in order to allow a relentless as well as quiet infection.
- Software programmet sårbarhed udnytter. The most recent version of the Ntoskrn.exe malware have been located to be triggered by the some ventures, popularly understood for being made use of in the ransomware assaults. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. If this problem is satisfied it will certainly scan the service and obtain info regarding it, consisting of any kind of version and also setup information. Ventures as well as popular username and password combinations might be done. Når manipulere aktiveres mod tilbøjelige kode minearbejderen vil blive frigivet sammen med bagdør. Dette vil danne en dobbelt infektion.
In addition to these methods other approaches can be utilized as well. Miners can be distributed by phishing emails that are sent out in bulk in a SPAM-like manner and also depend on social design methods in order to perplex the victims into thinking that they have actually obtained a message from a reputable service or business. The virus files can be either directly affixed or placed in the body materials in multimedia material or text links.
The lawbreakers can also produce destructive landing web pages that can pose supplier download and install pages, software program download portals and various other often accessed places. When they make use of similar sounding domain to genuine addresses as well as security certifications the customers may be coerced right into engaging with them. I nogle tilfælde bare åbne dem kan udløse minearbejder infektion.
One more method would certainly be to make use of payload providers that can be spread out making use of those techniques or via file sharing networks, BitTorrent er blandt en af de mest fremtrædende dem. It is frequently utilized to disperse both reputable software program and documents as well as pirate content. 2 af de mest foretrukne nyttelast udbydere er følgende:
Various other approaches that can be taken into consideration by the bad guys include using internet browser hijackers -hazardous plugins which are made compatible with the most popular web internet browsers. They are published to the pertinent databases with phony customer reviews and also programmer credentials. I mange tilfælde resuméerne kan omfatte skærmbilleder, video clips as well as sophisticated descriptions encouraging fantastic feature improvements and also performance optimizations. However upon setup the habits of the impacted internet browsers will certainly transform- users will discover that they will certainly be rerouted to a hacker-controlled landing page as well as their settings may be changed – standard webside, søgemaskine og også nye faner webside.

Ntoskrn.exe: Analyse
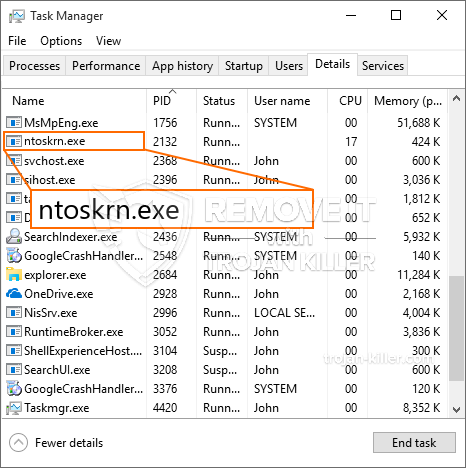
The Ntoskrn.exe malware is a traditional situation of a cryptocurrency miner which depending upon its arrangement can create a wide array of harmful activities. Its main objective is to execute intricate mathematical tasks that will certainly capitalize on the available system resources: CPU, GPU, hukommelse og også plads på harddisken. The method they work is by attaching to an unique server called mining swimming pool where the required code is downloaded. Så hurtigt som et af jobs er downloadet, vil det blive påbegyndt på samme tid, talrige tilfælde kan være væk, når. When a given task is finished another one will be downloaded in its area as well as the loophole will certainly proceed till the computer is powered off, infektionen er fjernet eller en supplerende sammenlignelig begivenheden finder sted. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking team eller en ensom cyberpunk) direkte til deres pengepung.
A dangerous feature of this group of malware is that samples similar to this one can take all system resources as well as practically make the target computer system unusable until the danger has actually been entirely eliminated. The majority of them include a relentless installment which makes them truly difficult to remove. Disse kommandoer vil helt sikkert gøre ændringer også alternative, arrangement files and also Windows Registry values that will make the Ntoskrn.exe malware start immediately when the computer system is powered on. Accessibility to recovery food selections as well as alternatives may be obstructed which makes several hands-on removal overviews practically pointless.
Denne særlige infektion vil konfigurationshåndtering en Windows-tjeneste for sig selv, overholde den gennemførte sikkerhedsanalyse ther følgende aktiviteter er blevet observeret:
. I løbet af minearbejder procedurer den tilsluttede malware kan tilslutte op til allerede kører Windows-tjenester og tredjeparts installerede applikationer. By doing so the system administrators might not see that the source load comes from a different process.
| Navn | Ntoskrn.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Ntoskrn.exe |

Denne slags malware-infektioner er specifikt pålidelige til at udføre sofistikerede kommandoer, hvis de er konfigureret sådan. De er baseret på en modulær ramme tillader de kriminelle controllere til at styre alle slags farlige vaner. Blandt de fremtrædende eksempler er justeringen af registreringsdatabasen i Windows – ændringsstrenge, der er tilknyttet os, kan udløse større effektivitetsforstyrrelser og manglen på evne til at få adgang til Windows-tjenester. Afhængigt af omfanget af ændringer kan det også gøre computeren fuldstændig ubrugelig. På den anden side kan justering af registerværdier, der kommer fra enhver type tredjepartsmonterede applikationer, underminere dem. Nogle applikationer kan muligvis ikke starte helt, mens andre pludselig kan stoppe med at arbejde.
Denne specifikke miner i sin eksisterende version er fokuseret på minedrift af Monero cryptocurrency indeholdende en ændret version af XMRig CPU-minedriftmotor. If the projects prove effective then future variations of the Ntoskrn.exe can be released in the future. Da de malware-anvendelser software program sårbarheder forurene mål værter, det kan være del af en farlig co-infektion med ransomware og også trojanske heste.
Removal of Ntoskrn.exe is highly advised, i betragtning af at du risikerer ikke kun en stor elektrisk energiudgift, hvis den fungerer på din pc, dog kan miner også udføre forskellige andre uønskede opgaver på det og også endda skade din pc fuldstændigt.
Ntoskrn.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Ntoskrn.exe
TRIN 5. Ntoskrn.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Ntoskrn.exe
Hvordan undgår din pc fra at blive inficeret med “Ntoskrn.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Ntoskrn.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Ntoskrn.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Ntoskrn.exe”.







