En ny, meget farlig cryptocurrency minearbejder virus er blevet opdaget af sikkerhedsmæssige forskere. den malware, hedder NiceHashMinerLegacy.exe kan inficere target syge anvender et udvalg af metoder. Hovedideen bag NiceHashMinerLegacy.exe minearbejderen er at udnytte cryptocurrency minearbejde på computersystemerne for mål for at erhverve Monero-tokens til måludgifter. The end result of this miner is the raised electrical power bills as well as if you leave it for longer amount of times NiceHashMinerLegacy.exe may also harm your computers components.
NiceHashMinerLegacy.exe: distributionssystemer Metoder
Det NiceHashMinerLegacy.exe malware gør brug af 2 popular techniques which are made use of to contaminate computer targets:
- Payload Levering via Prior Infektioner. If an older NiceHashMinerLegacy.exe malware is deployed on the victim systems it can instantly upgrade itself or download a newer variation. This is feasible using the integrated upgrade command which obtains the launch. This is done by connecting to a specific predefined hacker-controlled web server which supplies the malware code. The downloaded infection will obtain the name of a Windows service as well as be placed in the “%systemet% temp” areal. Vital residential properties as well as operating system arrangement documents are changed in order to allow a consistent as well as silent infection.
- Software programmet sårbarhed udnytter. The newest version of the NiceHashMinerLegacy.exe malware have actually been found to be brought on by the some ventures, populært anerkendt for at blive udnyttet i ransomware strikes. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Angrebene automatiseres af en hacker-kontrolleret struktur, der ser op, hvis porten er åben. If this problem is satisfied it will check the service and recover details about it, herunder enhver form for variation og også konfigurationsdata. Ventures såvel som fremtrædende kombinationer af brugernavn og adgangskode kan udføres. When the exploit is set off versus the susceptible code the miner will be deployed along with the backdoor. Dette vil danne en dobbelt infektion.
Apart from these approaches other methods can be made use of also. Miners can be dispersed by phishing e-mails that are sent out wholesale in a SPAM-like manner as well as depend upon social engineering techniques in order to confuse the sufferers right into thinking that they have received a message from a legit solution or company. The virus documents can be either straight attached or inserted in the body materials in multimedia content or text web links.
The lawbreakers can additionally produce malicious touchdown pages that can pose supplier download pages, portaler til download af software og også andre regelmæssigt tilgåede områder. When they make use of similar sounding domain to legit addresses and safety certificates the customers might be pushed right into connecting with them. I mange tilfælde blot at åbne dem kan aktivere minearbejder infektion.
An additional approach would certainly be to utilize payload providers that can be spread using those methods or by means of documents sharing networks, BitTorrent er blandt en af de mest fremtrædende dem. It is often utilized to disperse both legitimate software and also documents as well as pirate web content. 2 af de mest prominente haul luftfartsselskaber er følgende:
Other methods that can be taken into consideration by the wrongdoers include the use of internet browser hijackers -unsafe plugins which are made suitable with the most preferred internet browsers. They are posted to the appropriate databases with phony individual testimonials and also developer credentials. I mange tilfælde resuméerne kan omfatte skærmbilleder, video clips and sophisticated summaries promising excellent feature improvements as well as performance optimizations. Nonetheless upon installation the behavior of the impacted web browsers will change- customers will certainly discover that they will certainly be rerouted to a hacker-controlled touchdown page as well as their settings may be modified – standard webside, online søgemaskine og helt nye faner webside.
NiceHashMinerLegacy.exe: Analyse
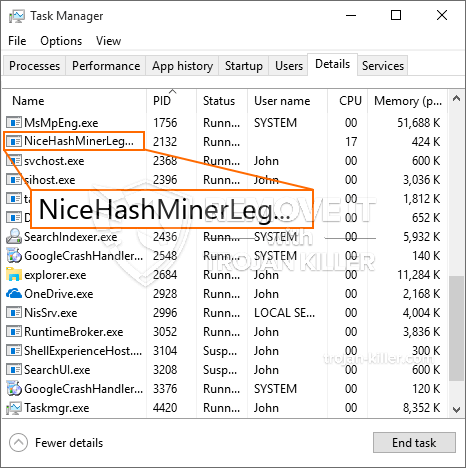
The NiceHashMinerLegacy.exe malware is a traditional case of a cryptocurrency miner which depending on its configuration can trigger a variety of dangerous actions. Its major objective is to carry out complicated mathematical tasks that will capitalize on the offered system sources: CPU, GPU, hukommelse samt harddisk plads. The way they operate is by connecting to a special server called mining pool from where the called for code is downloaded. Så snart et af jobene er downloadet, startes det helt sikkert samtidigt, talrige tilfælde kan køres på en gang. When an offered job is finished another one will certainly be downloaded and install in its place and the loophole will certainly continue up until the computer is powered off, the infection is gotten rid of or one more similar event takes place. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres punge.
A harmful feature of this category of malware is that examples like this one can take all system sources as well as almost make the victim computer system pointless till the threat has actually been totally gotten rid of. Most of them feature a relentless installment that makes them really hard to eliminate. Disse kommandoer vil helt sikkert gøre ændringer også valg, configuration documents and also Windows Registry values that will certainly make the NiceHashMinerLegacy.exe malware beginning instantly once the computer system is powered on. Accessibility to healing food selections and also choices may be obstructed which makes many manual removal guides virtually useless.
Denne vis infektion vil konfigurationshåndtering en Windows løsning for sig selv, complying with the conducted protection analysis ther complying with actions have actually been observed:
. During the miner procedures the associated malware can attach to already running Windows services as well as third-party mounted applications. By doing so the system administrators might not notice that the source lots comes from a different procedure.
| Navn | NiceHashMinerLegacy.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove NiceHashMinerLegacy.exe |
id =”82012″ align =”aligncenter” width =”600″]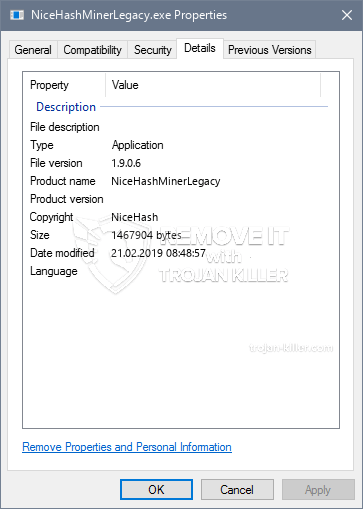 NiceHashMinerLegacy.exe
NiceHashMinerLegacy.exe
These sort of malware infections are specifically effective at performing sophisticated commands if set up so. They are based on a modular structure permitting the criminal controllers to coordinate all sort of harmful actions. Et af de fremtrædende eksempler er ændringen af Windows-registreringsdatabasen – alterations strings related by the os can cause significant performance disturbances and also the inability to gain access to Windows solutions. Depending on the scope of modifications it can also make the computer system entirely unusable. På den anden side kan kontrol af registreringsværdier, der kommer fra enhver form for tredjepartsopsætningsapplikationer, underminere dem. Nogle programmer kan stoppe med at arbejde for at frigøre helt, mens andre kan lige pludselig afslutte arbejdet.
This particular miner in its current variation is focused on mining the Monero cryptocurrency containing a modified variation of XMRig CPU mining engine. If the campaigns verify effective after that future variations of the NiceHashMinerLegacy.exe can be launched in the future. Da malware udnytter software program susceptabilities at forurene mål værter, det kan være en del af et farligt co-infektion med ransomware samt trojanske heste.
Removal of NiceHashMinerLegacy.exe is strongly recommended, given that you take the chance of not just a large power expense if it is working on your PC, however the miner might likewise do various other unwanted activities on it and even damage your COMPUTER completely.
NiceHashMinerLegacy.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove NiceHashMinerLegacy.exe
TRIN 5. NiceHashMinerLegacy.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove NiceHashMinerLegacy.exe
Hvordan undgår din pc fra at blive inficeret med “NiceHashMinerLegacy.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “NiceHashMinerLegacy.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “NiceHashMinerLegacy.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “NiceHashMinerLegacy.exe”.