En ny, ekstremt farligt cryptocurrency minearbejder infektion rent faktisk er blevet identificeret af sikkerhed og sikring forskere. den malware, hedder MSASCuiiL.exe kan inficere målsyge på en række måder. Essensen bag MSASCuiiL.exe-minearbejderen er at udnytte cryptocurrency-minearbejdsaktiviteter på computere hos syge for at få Monero-tokens til syge bekostning. Resultatet af denne minearbejder er de forhøjede strømregninger, og hvis du forlader den i længere perioder, kan MSASCuiiL.exe endda beskadige dine computersystemers elementer.
MSASCuiiL.exe: distributionssystemer Metoder
Det MSASCuiiL.exe malware bruger to foretrukne teknikker, som bruges til at inficere computermål:
- Nyttelast Levering ved hjælp af kendte Infektioner. Hvis en ældre MSASCuiiL.exe malware frigives på de syge systemer, kan den øjeblikkeligt opgradere sig selv eller downloade en nyere version. Dette er muligt gennem den integrerede opgradering kommando, som opnår frigivelse. Dette gøres ved at linke til en specifik foruddefineret hacker-styret webserver, som tilbyder malware-koden. Den downloadede infektion vil få navnet på en Windows-tjeneste samt blive sat i “%systemet% temp” placere. Vigtige bolig- eller kommercielle ejendomme og også data om operativsystemarrangementer transformeres for at tillade en konsekvent og tavs infektion.
- Software sårbarhed udnytter. Den nyeste variant af MSASCuiiL.exe malware har faktisk vist sig at være udløst af nogle ventures, bredt anerkendt for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. De overgreb er automatiseret af en hacker-kontrollerede rammer, som ser op, hvis porten er åben. Hvis dette problem er opfyldt, vil det helt sikkert tjekke tjenesten og også hente information om det, bestående af enhver version og konfigurationsdata. Udnyttelse såvel som populære brugernavne og adgangskoder kan udføres. Når manipulationen er sat i gang i forhold til den tilbøjelige kode, vil minearbejderen helt sikkert blive frigivet sammen med bagdøren. Dette vil præsentere en dobbelt infektion.
Ud over disse teknikker kan der også anvendes andre tilgange. Minearbejdere kan spredes af phishing-e-mails, der sendes engros på en SPAM-lignende måde, og som er afhængige af social engineering-metoder for at pusle ofrene lige til at tro, at de faktisk har fået en besked fra en lovlig tjeneste eller et firma. Virusfilerne kan enten være direkte forbundet eller placeres i kroppens indhold i multimedieindhold eller tekstweblinks.
Lovbryderne kan også producere destruktive landingswebsider, der kan efterligne leverandørens downloadwebsider, websteder til download af softwareprogrammer samt andre steder, der ofte tilgås. Når de bruger et domæne, der kan sammenlignes med velrenommerede adresser og også sikkerhedscertifikater, kan kunderne blive presset direkte til at kommunikere med dem. I nogle tilfælde blot at åbne dem kan forårsage minearbejder infektion.
En anden strategi ville helt sikkert være at bruge udbydere af transporttjenester, der kan spredes ud ved at bruge de ovennævnte tilgange eller via netværk til deling af dokumenter, BitTorrent er en af en af de mest fremtrædende dem. Det bruges ofte til at distribuere både velrenommeret software og data samt piratwebindhold. 2 af en af de mest foretrukne nyttelastbærere er følgende:
Forskellige andre tilgange, der kan tænkes på af skurkene, består i at bruge webbrowser hijackers -usikre plugins, som er gjort egnede med en af de mest foretrukne webbrowsere. De uploades til de relevante databaser med falske kundeudtalelser samt programmør-legitimationsoplysninger. I de fleste tilfælde resuméerne kan omfatte skærmbilleder, videoer og sofistikerede beskrivelser tiltalende fantastiske funktionsforbedringer og også effektivitetsoptimeringer. Ikke desto mindre ved installationen vil handlingerne af de berørte internetbrowsere helt sikkert ændre sig- brugere vil helt sikkert opdage, at de helt sikkert vil blive omdirigeret til en hacker-kontrolleret landingsside, ligesom deres indstillinger kan blive ændret – standard webside, internetsøgemaskine samt ny faneblad.
MSASCuiiL.exe: Analyse
MSASCuiiL.exe malware er en traditionel situation for en cryptocurrency minearbejder, som afhængigt af dens konfiguration kan forårsage en lang række skadelige handlinger. Dens primære mål er at udføre indviklede matematiske opgaver, der helt sikkert vil gøre brug af de let tilgængelige systemressourcer: CPU, GPU, hukommelse og også harddisk plads. Midlet, de opererer, er ved at linke til en unik server kaldet mining swimmingpool, hvorfra den nødvendige kode downloades og installeres. Så hurtigt som en af opgaverne er downloadet, vil den blive påbegyndt på samme tid, flere omstændigheder kan udføres så snart. Når et givet job er fuldført, vil et mere sikkert blive downloadet og installeret i stedet, ligesom løkken fortsætter, indtil computersystemet slukkes, infektionen elimineres, eller der sker en mere sammenlignelig lejlighed. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking team eller en ensom cyberpunk) direkte til deres punge.
En farlig kvalitet ved denne kategori af malware er, at prøver som denne kan tage alle systemkilder samt praktisk talt gøre målcomputersystemet ubrugeligt, indtil faren faktisk er blevet helt fjernet. De fleste af dem inkluderer en ubarmhjertig installation, som gør dem virkelig svære at fjerne. Disse kommandoer vil foretage justeringer af opstartsmuligheder, konfigurationsfiler og også Windows Registry-værdier, der helt sikkert vil få MSASCuiiL.exe-malwaren til at starte med det samme, når computersystemet tændes. Tilgængeligheden til gendannelsesfødevarevalg såvel som alternativer kan blive blokeret, hvilket giver masser af manuelle elimineringsvejledninger næsten ineffektive.
Denne specifikke infektion vil arrangementet en Windows-tjeneste for sig selv, efter den udførte beskyttelsesanalyse er der faktisk blevet observeret, at foranstaltningerne overholdes:
. Under minedriftsprocedurerne kan den tilknyttede malware oprette forbindelse til allerede kørende Windows-tjenester og også tredjepartsmonterede applikationer. Ved at gøre det kan systemadministratorerne muligvis ikke observere, at ressourcebelastningen stammer fra en anden procedure.
| Navn | MSASCuiiL.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at finde og fjerne MSASCuiiL.exe |
id =”83490″ align =”aligncenter” width =”600″]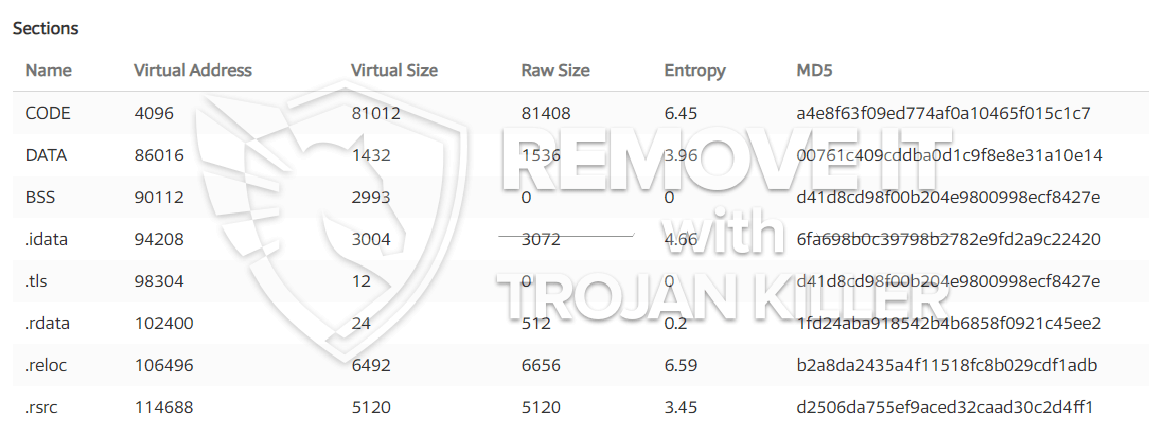 MSASCuiiL.exe
MSASCuiiL.exe
Disse slags malware-infektioner er særligt effektive til at udføre sofistikerede kommandoer, hvis de er konfigureret sådan. De er baseret på en modulær struktur, der tillader de kriminelle kontroller at koordinere alle former for usikre vaner. Blandt de populære forekomster er ændringen af registreringsdatabasen i Windows – ændringsstrenge relateret af os kan udløse store ydelsesforstyrrelser såvel som manglende adgang til Windows-løsninger. Afhængigt af omfanget af ændringer kan det desuden gøre computeren helt ubrugelig. På den anden side kan manipulation af registreringsværdier, der tilhører tredjeparts monterede applikationer, sabotere dem. Nogle applikationer kan ikke introduceres helt, mens andre uventet kan stoppe med at fungere.
Denne særlige minearbejder i sin nuværende variation er koncentreret om at udvinde Monero-kryptovalutaen, der indeholder en modificeret variation af XMRig CPU-minemotoren. Hvis kampagnerne viser sig effektive, kan fremtidige versioner af MSASCuiiL.exe introduceres i fremtiden. Da malware bruger sårbarheder i software til at inficere target værter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Fjernelse af MSASCuiiL.exe anbefales stærkt, fordi du tager chancen for ikke kun en stor strømudgift, hvis den virker på din COMPUTER, men minearbejderen kan også udføre forskellige andre uønskede opgaver på den og endda beskadige din pc permanent.
MSASCuiiL.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne MSASCuiiL.exe
TRIN 5. MSASCuiiL.exe er fjernet!
Video guide: Sådan bruger du GridinSoft Anti-Malware til at fjerne MSASCuiiL.exe
Hvordan undgår din pc fra at blive inficeret med “MSASCuiiL.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “MSASCuiiL.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “MSASCuiiL.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “MSASCuiiL.exe”.








