En ny, Virkelig skadelig kryptovaluta-minearbejdervirus er blevet fundet af forskere inden for sikkerhed og sikkerhed. den malware, hedder Iostream.exe kan forurene måloffer, der bruger et udvalg af måder. Hovedpointen bag Iostream.exe-minearbejderen er at anvende cryptocurrency-minearbejde på målsystemers computersystemer for at erhverve Monero-symboler til målpris. Resultatet af denne minearbejder er de forhøjede elektricitetsudgifter, og også hvis du forlader det i længere tid, kan Iostream.exe endda beskadige dine computersystemkomponenter.
Iostream.exe: distributionssystemer Metoder
Det Iostream.exe malware udnytter 2 fremtrædende teknikker, der bruges til at forurene computersystemmål:
- Payload Levering via Prior Infektioner. Hvis en ældre Iostream.exe-malware frigives på offersystemerne, kan den automatisk opdatere sig selv eller downloade og installere en nyere version. Dette er muligt ved hjælp af den integrerede opgraderingskommando, der opnår frigivelsen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den downloadede og installere infektion vil få navnet på en Windows-løsning og også blive placeret i “%systemet% temp” placere. Vigtige hjem og opsætningsfiler til operativsystemet ændres for at tillade en konsekvent såvel som tavs infektion.
- Software sårbarhed udnytter. Den seneste version af Iostream.exe-malwaren er faktisk blevet lokaliseret til at være forårsaget af nogle udnyttelser, kendt for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Overgrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis denne betingelse er opfyldt, vil den helt sikkert kontrollere løsningen samt hente detaljer om den, bestående af eventuelle variations- og opsætningsdata. Udnyttelse og fremtrædende brugernavn og adgangskodekombinationer kan udføres. Når brugen af er udløst i forhold til risikokoden, vil minearbejderen helt sikkert blive indsat i tillæg til bagdøren. Dette vil give den en dobbelt infektion.
Bortset fra disse metoder kan forskellige andre strategier også bruges. Minearbejdere kan distribueres ved hjælp af phishing-e-mails, der sendes ud i engros på en SPAM-lignende måde og også er afhængige af sociale designmetoder for at pusle ofrene til at tro, at de har modtaget en besked fra en legitim tjeneste eller et firma. The infection documents can be either straight affixed or put in the body materials in multimedia web content or text links.
The crooks can also produce destructive touchdown pages that can pose vendor download and install pages, websteder til download af softwareapplikationer og forskellige andre ofte tilgængelige steder. When they utilize similar sounding domain to legit addresses and safety and security certificates the customers may be coerced right into connecting with them. Nogle gange blot åbne dem kan modregne minearbejder infektion.
An additional method would be to use haul service providers that can be spread out utilizing the above-mentioned methods or using data sharing networks, BitTorrent er blot en af de mest populære. It is often made use of to distribute both reputable software as well as files as well as pirate material. To af en af de mest prominente nyttelast luftfartsselskaber er følgende:
Forskellige andre tilgange, der kan tages i betragtning af de onde, inkluderer brug af internetbrowser hijackers - usikre plugins, som er gjort egnede med en af de mest foretrukne web-internetbrowsere. De offentliggøres til de relevante databaser med falske kundeanmeldelser og også designerkvalifikationer. I mange tilfælde resuméerne kan omfatte skærmbilleder, videoer og også omfattende beskrivelser, der tilskynder til vidunderlige funktionsforbedringer og effektivitetsoptimeringer. Men ved afbetaling vil vanerne for de påvirkede webbrowsere ændre sig- brugere vil opdage, at de vil blive omdirigeret til en hacker-styret touchdown-side, og deres indstillinger kan blive ændret – standard startside, internetsøgemaskine og splinterny faner-webside.

Iostream.exe: Analyse
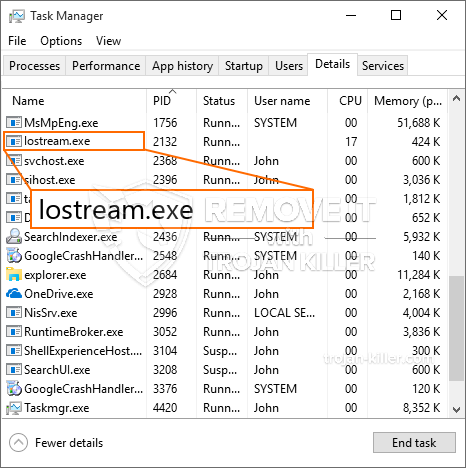
Iostream.exe malware er en klassisk situation for en cryptocurrency minearbejder, som afhængigt af dens konfiguration kan skabe en bred vifte af skadelige handlinger. Dets hovedmål er at udføre indviklede matematiske opgaver, der helt sikkert vil gøre brug af de tilbudte systemressourcer: CPU, GPU, hukommelse samt harddisk plads. Midlet, de fungerer, er ved at linke til en speciel server kaldet mining swimmingpool, hvorfra den nødvendige kode downloades og installeres. Så snart et af jobs er downloadet, vil det helt sikkert blive påbegyndt samtidigt, flere forhold kan køres på én gang. Når et tilbudt job er fuldført, vil endnu et blive downloadet og installeret i stedet, ligesom smuthullet vil fortsætte, indtil computeren slukkes, infektionen fået fjernet eller en anden tilsvarende begivenhed finder sted. Cryptocurrency vil blive kompenseret for de kriminelle controllere (hacking team eller en enkelt cyberpunk) direkte til deres tegnebøger.
Et farligt kendetegn ved denne gruppe af malware er, at prøver som denne kan tage alle systemkilder og praktisk talt gøre ofrets computersystem ubrugeligt, indtil truslen faktisk er blevet fuldstændig fjernet. De fleste af dem inkluderer en vedvarende installation, som gør dem faktisk udfordrende at slippe af med. Disse kommandoer vil helt sikkert foretage ændringer i opstartsmuligheder, konfigurationsdokumenter samt værdier i Windows registreringsdatabasen, der helt sikkert vil få Iostream.exe-malwaren til at starte automatisk, så snart computeren tændes. Tilgængeligheden til valg og muligheder for nyttiggørelse af fødevarer kan blive blokeret, hvilket gør masser af praktiske elimineringsoversigter praktisk talt meningsløse.
Denne særlige infektion vil arrangere en Windows-løsning for sig selv, overholdelse af den udførte sikkerhedsevaluering, og overholdelse af aktiviteter er faktisk blevet observeret:
. Under minedriftsprocedurerne kan den tilknyttede malware linke til aktuelt kørende Windows-løsninger og også installerede tredjepartsapplikationer. Ved at gøre det kan systemadministratorerne muligvis ikke se, at kildepartierne kommer fra en anden proces.
| Navn | Iostream.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at finde og fjerne Iostream.exe |

Disse former for malware-infektioner er særligt effektive til at udføre innovative kommandoer, hvis de er konfigureret sådan. De er baseret på en modulopbygget ramme, der tillader de kriminelle kontroller at håndtere alle typer usikre vaner. Et af de fremtrædende tilfælde er ændringen af Windows-registreringsdatabasen – justeringsstrenge forbundet af operativsystemet kan skabe alvorlige effektivitetsforstyrrelser og også manglen på mulighed for tilgængelighed til Windows-løsninger. Afhængigt af omfanget af justeringer kan det ligeledes gøre computersystemet helt meningsløst. På den anden side kan manipulation af registreringsværdier, der kommer fra tredjepartsmonterede applikationer, sabotere dem. Nogle applikationer holder muligvis op med at fungere helt for at introducere, mens andre uventet kan holde op med at arbejde.
Denne bestemte minearbejder i sin eksisterende variant er fokuseret på at udvinde Monero-kryptovalutaen bestående af en tilpasset variation af XMRig CPU-minemotoren. Hvis kampagnerne viser sig effektive efter det, kan fremtidige versioner af Iostream.exe introduceres i fremtiden. Da malware bruger sårbarheder i software til at inficere target værter, det kan være bestanddel af en farlig co-infektion med ransomware samt trojanske heste.
Fjernelse af Iostream.exe anbefales stærkt, fordi du tager chancen for ikke bare en stor el-udgifter, hvis den kører på din COMPUTER, alligevel kan minearbejderen også udføre forskellige andre uønskede opgaver på den samt endda ødelægge din pc fuldstændigt.
Iostream.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne Iostream.exe
TRIN 5. Iostream.exe er fjernet!
Video guide: Sådan bruger du GridinSoft Anti-Malware til at fjerne Iostream.exe
Hvordan undgår din pc fra at blive inficeret med “Iostream.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Iostream.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Iostream.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Iostream.exe”.







