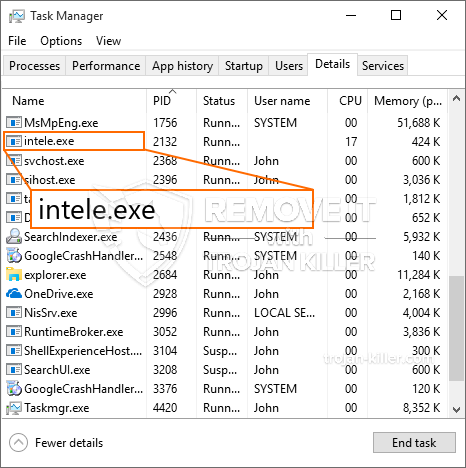
Et helt nyt, virkelig farlig kryptokurrency-minearbejdervirus er faktisk blevet opdaget af sikkerheds- og sikkerhedsforskere. den malware, hedder Intele.exe kan inficere target syge anvender et udvalg af midler. Hovedpointen bag Intele.exe-minearbejderen er at anvende cryptocurrency-minearbejderopgaver på de syges computere for at få Monero-symboler til syge udgifter. The outcome of this miner is the elevated electrical power expenses and if you leave it for longer amount of times Intele.exe might even harm your computer systems components.
Intele.exe: distributionssystemer Metoder
Det Intele.exe malware anvendelser 2 fremtrædende teknikker, som bliver brugt til at inficere computersystemmål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older Intele.exe malware is released on the victim systems it can immediately update itself or download and install a more recent version. Dette er muligt gennem den indbyggede opdateringskommando, som henter lanceringen. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. Den downloadede infektion vil helt sikkert få navnet på en Windows-tjeneste og også blive sat i “%systemet% temp” Beliggenhed. Vigtige hjem såvel som operativsystemets konfigurationsdata ændres for at tillade en ubarmhjertig og også stille infektion.
- Software sårbarhed udnytter. The latest variation of the Intele.exe malware have actually been discovered to be caused by the some exploits, populært kendt for at blive udnyttet i ransomware overfald. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Angrebene er automatiseret af en hacker-kontrollerede rammer, som søger efter, hvis porten er åben. Hvis denne betingelse er opfyldt, vil den kontrollere tjenesten og gendanne detaljer om den, inklusive enhver type version og konfigurationsdata. Udnytter samt populære brugernavn og adgangskode blandinger kan gøres. Når udnyttelsen er forårsaget versus risikokoden, vil minearbejderen helt sikkert blive indsat som supplement til bagdøren. Dette vil helt sikkert give en dobbelt infektion.
Ud over disse teknikker kan andre tilgange også gøres brug af. Minearbejdere kan distribueres ved phishing-e-mails, der sendes ud i engros på en SPAM-lignende måde og er afhængige af social engineering-teknikker for at forvirre de syge lige til at tro, at de har modtaget en besked fra en ægte tjeneste eller et firma. Virusdokumenterne kan enten anbringes direkte eller placeres i kropskomponenterne i multimedieindhold eller tekstweblinks.
Svindlerne kan ligeledes producere destruktive touchdown-sider, der kan betyde, at leverandøren downloader og installerer websider, software download portaler og også andre ofte adgang placeringer. Når de bruger lignende domæne til ægte adresser og sikkerhedscertifikater, kan brugerne blive overtalt lige til at kommunikere med dem. I nogle tilfælde kan blot åbning af dem aktivere minerinfektionen.
En anden strategi ville helt sikkert være at bruge nyttelastbærere, der kan spredes ved hjælp af disse teknikker eller via datadelingsnetværk, BitTorrent er blandt en af de mest populære. Det er ofte brugt til at sprede både legitim software og også filer samt piratindhold. To af de mest foretrukne transportudbydere er følgende:
Forskellige andre tilgange, der kan tænkes over af lovovertræderne, omfatter brugen af browser hijackers - farlige plugins, som er gjort egnede med de mest fremtrædende webbrowsere. De bliver sendt til de relevante depoter med falske kundeudtalelser og også programmørkvalifikationer. I mange tilfælde resuméerne kan omfatte skærmbilleder, videoer og omfattende resuméer, der tilskynder til vidunderlige egenskabsforbedringer og effektivitetsoptimeringer. Ikke desto mindre vil vanerne for de berørte browsere ændre sig ved afbetaling- enkeltpersoner vil finde ud af, at de helt sikkert vil blive omdirigeret til en hacker-styret touchdown-webside, og deres opsætninger kan blive ændret – standard startside, søgemaskine på internettet samt nye faner webside.

Intele.exe: Analyse
The Intele.exe malware is a traditional situation of a cryptocurrency miner which depending on its configuration can create a wide array of unsafe actions. Its main goal is to perform intricate mathematical tasks that will certainly make use of the offered system sources: CPU, GPU, hukommelse og harddisk område. Metoden, de fungerer, er ved at oprette forbindelse til en speciel webserver kaldet mining pool, hvor den krævede kode downloades og installeres. Så hurtigt som blandt opgaverne bliver downloadet det vil blive påbegyndt på en gang, flere omstændigheder kan køres når. When an offered task is finished one more one will certainly be downloaded and install in its area and the loop will proceed till the computer system is powered off, the infection is eliminated or an additional similar event happens. Cryptocurrency vil helt sikkert blive tildelt de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres pengepung.
A dangerous attribute of this category of malware is that examples similar to this one can take all system sources as well as practically make the sufferer computer system pointless until the hazard has actually been totally gotten rid of. The majority of them feature a consistent installation which makes them actually challenging to remove. Disse kommandoer vil helt sikkert gøre justeringer opstartsmuligheder, configuration data and Windows Registry values that will make the Intele.exe malware start automatically once the computer system is powered on. Accessibility to recuperation menus as well as choices might be obstructed which renders several hands-on removal guides almost pointless.
Denne specifikke infektion vil helt sikkert konfigurere en Windows -løsning til sig selv, adhering to the conducted protection analysis ther following actions have actually been observed:
. Under gruvearbejderdriften kan den tilknyttede malware kobles op til allerede kørende Windows-løsninger og også tredjeparts opsætning af applikationer. By doing so the system administrators may not discover that the resource lots originates from a different procedure.
| Navn | Intele.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Intele.exe |

These kind of malware infections are particularly effective at carrying out sophisticated commands if configured so. They are based upon a modular structure enabling the criminal controllers to orchestrate all sort of hazardous actions. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – modifications strings related by the operating system can create significant efficiency interruptions and the inability to gain access to Windows solutions. Depending on the scope of changes it can also make the computer completely unusable. On the various other hand manipulation of Registry values belonging to any kind of third-party installed applications can sabotage them. Some applications may fail to release altogether while others can unexpectedly quit working.
This specific miner in its current version is focused on mining the Monero cryptocurrency having a modified version of XMRig CPU mining engine. If the campaigns verify effective then future variations of the Intele.exe can be launched in the future. Da malware anvender softwareprogramsårbarheder til at forurene målværter, det kan være del af en skadelig co-infektion med ransomware og trojanske heste.
Elimination of Intele.exe is strongly recommended, given that you run the risk of not only a large power expense if it is working on your COMPUTER, yet the miner might additionally execute various other unwanted tasks on it and also harm your PC permanently.
Intele.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Intele.exe
TRIN 5. Intele.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Intele.exe
Hvordan undgår din pc fra at blive inficeret med “Intele.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Intele.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Intele.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Intele.exe”.







