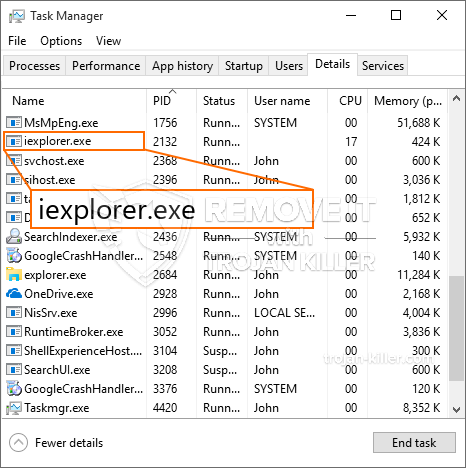
Et helt nyt, ekstremt farlig kryptokurrency minearbejde er blevet opdaget af sikkerhedsforskere. den malware, hedder Iexplorer.exe kan forurene target syge anvender et udvalg af metoder. Hovedideen bag Iexplorer.exe-minearbejderen er at bruge cryptocurrency-minearbejderaktiviteter på ofrenes computersystemer for at opnå Monero-tokens til målomkostninger. Resultatet af denne minearbejder er de øgede strømomkostninger, og hvis du forlader den i længere perioder, kan Iexplorer.exe også beskadige dine computers komponenter.
Iexplorer.exe: distributionssystemer Metoder
Det Iexplorer.exe malware bruger to foretrukne tilgange, som bruges til at forurene computermål:
- Payload Levering via Prior Infektioner. Hvis en ældre Iexplorer.exe malware er installeret på offersystemerne, kan den automatisk opgradere sig selv eller downloade en nyere version. Dette er muligt ved hjælp af den integrerede opgraderingskommando, som henter lanceringen. Dette gøres ved at linke til en bestemt foruddefineret hackerstyret server, der leverer malware-koden. Den hentet og installere infektion vil helt sikkert få navnet på en Windows-løsning og også placeres i den “%systemet% temp” placere. Vigtige bolig- eller erhvervsejendomme samt opsætningsdokumenter for operativsystemet ændres for at tillade en konsekvent såvel som tavs infektion.
- Software sårbarhed udnytter. Den seneste version af Iexplorer.exe-malwaren har faktisk vist sig at være forårsaget af nogle udnyttelser, berømt forstået for at blive udnyttet i de ransomware angreb. Infektionerne er færdig ved at målrette åbne løsninger via TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. Hvis dette problem er opfyldt, vil det helt sikkert tjekke tjenesten og også hente information om det, inklusive enhver version og også opsætningsdata. Foretagende og foretrukne brugernavn samt adgangskodeblandinger kan udføres. Når brugen af er modregnet i forhold til den sårbare kode, vil minearbejderen helt sikkert blive frigivet sammen med bagdøren. Dette vil helt sikkert give en dobbelt infektion.
Ud over disse tilgange kan der også gøres brug af forskellige andre tilgange. Minearbejdere kan spredes af phishing-e-mails, der sendes engros på en SPAM-lignende måde, såvel som afhængige af social engineering-metoder for at pusle målene lige til at tro, at de har modtaget en besked fra en ægte løsning eller virksomhed. Infektionsfilerne kan enten sættes direkte på eller lægges i kropskomponenterne i multimediewebindhold eller tekstlinks.
Svindlerne kan også oprette destruktive touchdown-websider, der kan efterligne leverandørens download og installation af websider, portaler til download af software og også andre regelmæssigt tilgåede områder. Når de bruger et domæne, der ligner velrenommerede adresser og sikkerheds- og sikkerhedscertifikater, kan brugerne blive tvunget direkte til at oprette forbindelse til dem. I nogle tilfælde bare åbne dem kan udløse minearbejder infektion.
En anden tilgang ville være at bruge transportudbydere, der kan spredes ud ved at bruge de ovennævnte teknikker eller gennem datadelingsnetværk, BitTorrent er blot en af de mest populære. Det bruges ofte til at sprede både velrenommeret softwareapplikation og filer samt piratindhold. To af en af de mest foretrukne lastbærere er følgende:
Forskellige andre teknikker, der kan tages i betragtning af forbryderne, omfatter brugen af browser hijackers - skadelige plugins, som er gjort egnede med de mest populære internetbrowsere. De offentliggøres til de relevante databaser med falske kundeevalueringer og udviklerkvalifikationer. Ofte resuméer kan omfatte skærmbilleder, videoklip og også fancy resuméer tiltalende store funktionsforbedringer og også effektivitetsoptimeringer. Ikke desto mindre vil adfærden for de berørte browsere ændre sig ved afbetaling- enkeltpersoner vil helt sikkert opdage, at de vil blive omdirigeret til en hacker-kontrolleret landingswebside, og deres indstillinger kan også blive ændret – standard startside, online søgemaskine og helt nye faner side.

Iexplorer.exe: Analyse
Iexplorer.exe malware er et traditionelt tilfælde af en cryptocurrency minearbejder, som afhængigt af dens konfiguration kan udløse en lang række skadelige aktiviteter. Dens hovedmål er at udføre indviklede matematiske opgaver, der vil gøre brug af de tilbudte systemkilder: CPU, GPU, hukommelse såvel som harddiskområdet. Metoden de bruger er ved at oprette forbindelse til en unik webserver kaldet mining pool, hvorfra den kaldede kode downloades og installeres. Så hurtigt som en af opgaverne er downloadet, vil den helt sikkert blive startet med det samme, flere omstændigheder kan udføres ved så snart. Når en opgave er færdig, vil en anden blive downloadet i sit område, og også smuthullet vil fortsætte, indtil computersystemet slukkes, infektionen er fjernet, eller der finder en anden sammenlignelig lejlighed sted. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres tegnebøger.
En farlig egenskab ved denne kategori af malware er, at eksempler som denne kan tage alle systemressourcer og også praktisk talt gøre målcomputeren meningsløs, indtil faren faktisk er blevet fuldstændig fjernet. Mange af dem inkluderer en vedvarende rate, som gør dem virkelig svære at slippe af med. Disse kommandoer vil helt sikkert foretage ændringer i bootvalg, konfigurationsdokumenter samt værdier i Windows-registreringsdatabasen, der får Iexplorer.exe-malwaren til at starte øjeblikkeligt, så snart computersystemet tændes. Tilgængeligheden til rekreationsmenuer og også alternativer kan være blokeret, hvilket giver flere manuelle fjernelsesoversigter næsten værdiløse.
Denne specifikke infektion vil konfigurationshåndtering en Windows løsning for sig selv, efter den udførte sikkerhedsanalyse er der observeret overholdelse af handlinger:
. Under minedriftsprocedurerne kan den tilsluttede malware oprette forbindelse til aktuelt kørende Windows-løsninger såvel som tredjeparts opsætningsapplikationer. Ved at gøre det opdager systemadministratorerne muligvis ikke, at kildebelastningen stammer fra en anden procedure.
| Navn | Iexplorer.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at finde og fjerne Iexplorer.exe |

Disse slags malwareinfektioner er særligt effektive til udførelse sofistikerede kommandoer, hvis konfigureret således. De er baseret på en modulær ramme, der tillader de kriminelle kontroller at håndtere alle slags farlige vaner. Et af de fremtrædende tilfælde er ændringen af Windows-registreringsdatabasen – ændringsstrenge forbundet med operativsystemet kan skabe betydelige ydeevneforstyrrelser og også manglen på mulighed for at få adgang til Windows-tjenester. Under henvisning til omfanget af forandringer, det kan desuden gøre computersystemet helt meningsløst. På den anden side kontrol af Registry worths kommer fra en hvilken som helst form for tredjepart monteret programmer kan underminere dem. Nogle programmer kan stoppe med at arbejde for at indføre helt, mens andre uventet kan stoppe med at arbejde.
Denne bestemte minearbejder i sin eksisterende variation er koncentreret om at udvinde Monero-kryptovalutaen med en modificeret version af XMRig CPU-minemotoren. Hvis projekterne viser sig effektive, kan fremtidige versioner af Iexplorer.exe frigives i fremtiden. Da malware udnytter software program susceptabilities at inficere target værter, det kan være en del af en skadelig co-infektion med ransomware samt trojanske heste.
Fjernelse af Iexplorer.exe anbefales stærkt, i betragtning af, at du risikerer ikke bare en stor elregning, hvis den virker på din COMPUTER, alligevel kan minearbejderen også udføre andre uønskede aktiviteter på den og endda skade din pc permanent.
Iexplorer.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne Iexplorer.exe
TRIN 5. Iexplorer.exe er fjernet!
Video guide: Sådan bruger du GridinSoft Anti-Malware til at fjerne Iexplorer.exe
Hvordan undgår din pc fra at blive inficeret med “Iexplorer.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Iexplorer.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Iexplorer.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Iexplorer.exe”.







