En ny, meget skadelig kryptokurrency-minearbejdervirus er faktisk blevet set af sikkerhedsforskere. den malware, hedder IdlenessBuddyService.exe can infect target sufferers utilizing a variety of means. Essensen bag IdlenessBuddyService.exe-minearbejderen er at udnytte cryptocurrency-minearbejderopgaver på computersystemer for syge for at få Monero-tokens på ofrets bekostning. The outcome of this miner is the raised power bills and also if you leave it for longer periods of time IdlenessBuddyService.exe may also harm your computers parts.
IdlenessBuddyService.exe: distributionssystemer Metoder
Det IdlenessBuddyService.exe malware gør brug af 2 foretrukne teknikker, som anvendes til at forurene edb-system mål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older IdlenessBuddyService.exe malware is released on the target systems it can automatically upgrade itself or download a more recent version. Dette er muligt ved hjælp af den integrerede opgraderingskommando, der opnår lanceringen. Dette gøres ved at forbinde til en specifik foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. Den downloadede virus får bestemt navnet på en Windows-tjeneste og placeres også i “%systemet% temp” placere. Afgørende huse og konfigurationsdokumenter til operativsystemet ændres for at muliggøre en konsistent og også lydløs infektion.
- Software sårbarhed udnytter. The most recent version of the IdlenessBuddyService.exe malware have actually been discovered to be caused by the some ventures, ofte forstået for at blive brugt i ransomware-strejkerne. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. De overgreb er automatiseret af en hacker-kontrollerede rammer, som ser op, hvis porten er åben. Hvis dette problem er opfyldt, vil det kontrollere løsningen og hente detaljer om det, bestående af enhver type variation og opsætningsdata. Udnyttelse såvel som foretrukne brugernavn og adgangskodeblandinger kan udføres. Når udnyttelsen udløses mod den modtagelige kode, frigives minearbejderen sammen med bagdøren. Dette vil bestemt præsentere en dobbelt infektion.
Bortset fra disse teknikker kan der også anvendes andre metoder. Minearbejdere kan spredes ved phishing-e-mails, der sendes engros på en SPAM-lignende måde og er afhængige af social designteknikker for at forvirre ofrene til at tro, at de har modtaget en besked fra en ægte tjeneste eller virksomhed. Infektionsdataene kan enten direkte vedhæftes eller indsættes i kropskomponenterne i multimediemateriale eller tekstweblink.
Crooks kan desuden udvikle ondsindede destinationswebsider, der kan udgøre leverandørens download og installere sider, softwareprogrammets downloadsteder og også andre steder, der ofte er tilgængelige. Når de bruger lignende klodende domæne som ægte adresser såvel som beskyttelsescertificeringer, kan kunderne blive tvunget til at engagere sig med dem. I nogle tilfælde kan blot åbning af dem forårsage minearbejdsinfektion.
En anden fremgangsmåde ville være at anvende transportfirmaer, der kan spredes ved hjælp af ovennævnte metoder eller gennem netværk til deling af dokumenter, BitTorrent er en af de mest foretrukne dem. Det bruges ofte til at sprede både ægte software såvel som filer og piratmateriale. To af de mest populære distancer udbydere er følgende:
Andre tilgange, som de kriminelle kan tage i betragtning, inkluderer anvendelse af internetbrowser-kaprere - farlige plugins, der er gjort egnede til de mest foretrukne internetbrowsere. De indsendes til de relevante databaser med falske kundevurderinger og også programmereroplysninger. Oftentimes oversigter kan omfatte skærmbilleder, videoklip og sofistikerede resume, der tilskynder til store funktionsforbedringer og ydeevneoptimeringer. Ikke desto mindre ændres vanerne hos de påvirkede browsere ved afbetaling- brugere vil finde, at de bestemt vil blive omdirigeret til en hacker-kontrolleret touchdown-side, og deres indstillinger kan blive ændret – standard startside, online søgemaskine og også helt nye faner webside.

IdlenessBuddyService.exe: Analyse
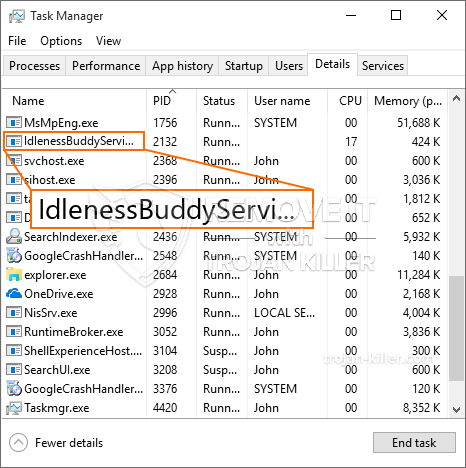
The IdlenessBuddyService.exe malware is a classic situation of a cryptocurrency miner which relying on its setup can trigger a wide range of dangerous activities. Its major objective is to carry out complicated mathematical tasks that will capitalize on the offered system sources: CPU, GPU, hukommelse og også harddisk plads. The method they work is by linking to a special web server called mining swimming pool from where the needed code is downloaded and install. As quickly as among the tasks is downloaded it will certainly be begun simultaneously, flere tilfælde kan være væk for en gangs skyld. When an offered job is finished another one will be downloaded in its place and also the loophole will continue till the computer system is powered off, infektionen fået fjernet eller en mere sammenlignelige lejlighed sker. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres pengepung.
A hazardous quality of this category of malware is that examples like this one can take all system sources as well as practically make the victim computer system pointless until the hazard has been completely removed. The majority of them feature a relentless installation which makes them actually tough to eliminate. Disse kommandoer vil foretage justeringer også alternativer, arrangement files and also Windows Registry values that will make the IdlenessBuddyService.exe malware begin automatically as soon as the computer system is powered on. Accessibility to healing food selections and also options may be blocked which renders lots of manual removal guides practically pointless.
Denne specifikke infektion vil helt sikkert konfigurationshåndtering en Windows-tjeneste for sig selv, following the carried out protection evaluation ther complying with activities have been observed:
. During the miner procedures the associated malware can connect to currently running Windows solutions as well as third-party set up applications. By doing so the system administrators might not notice that the resource tons comes from a different procedure.
| Navn | IdlenessBuddyService.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove IdlenessBuddyService.exe |

These type of malware infections are particularly efficient at executing advanced commands if set up so. They are based on a modular framework allowing the criminal controllers to orchestrate all type of harmful habits. Blandt de foretrukne eksempler er justeringen af registreringsdatabasen i Windows – modifications strings connected by the operating system can cause major efficiency disturbances and also the lack of ability to gain access to Windows services. Depending upon the range of adjustments it can also make the computer system completely unusable. På den anden side kan justering af registreringsværdier, der hører til tredjeparts opsatte applikationer, sabotere dem. Nogle applikationer kan muligvis ikke starte helt, mens andre pludselig kan stoppe med at arbejde.
This specific miner in its present variation is concentrated on extracting the Monero cryptocurrency consisting of a customized variation of XMRig CPU mining engine. If the campaigns prove successful then future variations of the IdlenessBuddyService.exe can be launched in the future. Da malware bruger sårbarheder i software til at inficere target værter, det kan være del af en skadelig co-infektion med ransomware og også trojanske heste.
Elimination of IdlenessBuddyService.exe is strongly suggested, because you take the chance of not just a huge electrical power expense if it is working on your COMPUTER, yet the miner might likewise execute other undesirable tasks on it and also harm your COMPUTER permanently.
IdlenessBuddyService.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove IdlenessBuddyService.exe
TRIN 5. IdlenessBuddyService.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove IdlenessBuddyService.exe
Hvordan undgår din pc fra at blive inficeret med “IdlenessBuddyService.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “IdlenessBuddyService.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “IdlenessBuddyService.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “IdlenessBuddyService.exe”.







