Et helt nyt, virkelig farligt cryptocurrency minearbejder virus er blevet identificeret af sikkerhedseksperter. den malware, hedder Find.exe kan forurene målramte ved hjælp af et udvalg af metoder. Hovedidéen bag den Find.exe minearbejder er at ansætte cryptocurrency minearbejder aktiviteter på computere mål for at få Monero poletter på syge’ koste. Resultatet af denne minearbejder er de øgede elektriske energiomkostninger, og hvis du forlader den i længere perioder, kan Find.exe endda skade dit computersystems komponenter.
Find.exe: distributionssystemer Metoder
Det Find.exe malware anvendelser 2 foretrukne fremgangsmåder, der anvendes til kontaminere computer mål:
- Nyttelast Levering ved hjælp af kendte Infektioner. Hvis en ældre Find.exe malware er implementeret på de syge systemer, kan den øjeblikkeligt opgradere sig selv eller downloade og installere en nyere variant. Dette er muligt gennem den indbyggede opgraderingskommando, der opnår frigivelsen. Dette gøres ved at linke til en bestemt foruddefineret hacker-styret server, der giver malware-koden. Den downloadede infektion får helt sikkert navnet på en Windows-tjeneste og placeres i “%systemet% temp” Beliggenhed. Vitale boliger eller kommercielle ejendomme og også kørende systemarrangementsdokumenter ændres for at muliggøre en ubarmhjertig og også lydløs infektion.
- Software programmet sårbarhed udnytter. Den mest aktuelle variant af Find.exe-malwaren er blevet fundet for at blive anlagt af nogle ventures, berømt kendt for at blive brugt i ransomware-angrebene. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som søger efter hvis porten er åben. Hvis dette problem er opfyldt, vil det kontrollere løsningen og også hente detaljer om det, inklusive enhver type version og også konfigurationsoplysninger. Ventures og populære brugernavn og adgangskodeblandinger kan gøres. Når manipuleringen er forårsaget mod den sårbare kode, udlægges minearbejderen sammen med bagdøren. Dette vil danne en dobbelt infektion.
Bortset fra disse teknikker kan andre tilgange også bruges. Minearbejdere kan spredes ved phishing-e-mails, der sendes engros på en SPAM-lignende måde og stole på sociale designmetoder for at forvirre målene til at tro, at de rent faktisk har fået en besked fra en legitim løsning eller virksomhed. Virusdokumenterne kan enten forbindes direkte eller indsættes i kropsmaterialerne i multimediemateriale eller tekstlinks.
Forbrydere kan også producere destruktive destinationssider, der kan udgøre download og installation af websider, websteder til download af softwareprogrammer samt forskellige andre ofte tilgængelige steder. Når de bruger lignende tilsyneladende domænenavne til legitime adresser og også sikkerhedscertifikater, kan kunderne blive skubbet lige ind i at interagere med dem. I mange tilfælde bare åbne dem kan forårsage minearbejder infektion.
En yderligere tilgang ville helt sikkert være at bruge trækudbydere, der kan spredes ved hjælp af disse metoder eller ved hjælp af fildelingsnetværk, BitTorrent er blot en af de mest foretrukne dem. Det bruges regelmæssigt til at distribuere både velrenommeret softwareprogram og også filer og piratwebindhold. 2 af en af de mest fremtrædende haul udbydere er følgende:
Forskellige andre tilgange, der kan tages i betragtning af de onde, inkluderer brug af browserkapere - usikre plugins, der er velegnet med en af de mest foretrukne internetbrowsere. De uploades til de relevante databaser med falske individuelle anmeldelser og også designeroplysninger. I de fleste tilfælde beskrivelserne kan bestå af screenshots, videoklip og også sofistikerede beskrivelser, der lover fremragende attributforbedringer og også ydeevneoptimeringer. Ikke desto mindre ændres adfærden hos de påvirkede webbrowsere ved afdrag bestemt- enkeltpersoner vil helt sikkert finde ud af, at de vil blive omdirigeret til en hackerstyret touchdown-side, såvel som deres indstillinger kan ændres – standard webside, søgemaskine samt helt nye side faner.
Find.exe: Analyse
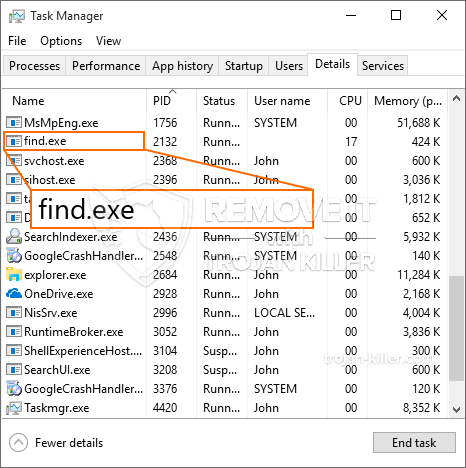
Find.exe malware er en tidløs situation for en cryptocurrency minearbejder, som afhængigt af dens arrangement kan udløse en lang række farlige handlinger. Dets vigtigste mål er at gøre komplicerede matematiske opgaver, der vil udnytte de udbudte systemressourcer: CPU, GPU, hukommelse samt harddisk plads. Den måde, de arbejder er ved at forbinde til en særlig server kaldet minedrift swimmingpool, hvorfra den krævede kode er downloadet og installere. Så hurtigt som blandt opgaverne bliver downloadet det vil blive påbegyndt på en gang, talrige tilfælde kan køres på en gang. Når en tilbudt opgave er færdig endnu en vil blive hentet og installere på sin plads og sløjfen vil helt sikkert fortsætte, indtil computeren er slukket, infektionen fået fjernet eller sker en anden lignende arrangement. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking team eller en ensom cyberpunk) direkte til deres punge.
En usikker karakteristisk for denne kategori af malware er, at eksemplerne som denne kan tage alle system ressourcer og også stort set gøre målcomputeren meningsløst indtil faren faktisk er blevet fuldstændig elimineret. De fleste af dem har en ensartet installation, der gør dem virkelig udfordrende at eliminere. Disse kommandoer vil helt sikkert gøre ændringer boot alternativer, konfigurationsfiler og Windows Registry-værdier, der vil få Find.exe-malwaren til at starte automatisk, når computersystemet er tændt. Tilgængelighed til rekreation mad valg samt valg muligvis blokeret som giver masser af manuelle fjernelse oversigter praktisk meningsløse.
Denne særlige infektion vil helt sikkert konfigurationshåndtering en Windows løsning for sig selv, efter den gennemførte beskyttelse analyse ther følgende handlinger er blevet observeret:
. Under minearbejder operationer den tilknyttede malware kan knytte til i øjeblikket kører Windows-tjenester og tredjeparts oprettet applikationer. Ved at gøre så systemet ledere kan ikke se, at kilden belastningen kommer fra en anden procedure.
| Navn | Find.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware for at finde og fjerne Find.exe |
id =”82513″ align =”aligncenter” width =”600″] Find.exe
Find.exe
Disse slags malware infektioner er specielt pålidelige på udførelse af sofistikerede kommandoer, hvis konfigureret så. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontroller at styre alle typer skadelige handlinger. Blandt de fremtrædende eksempler er ændringen af registreringsdatabasen i Windows – ændringsstrenge, der er relateret til OS, kan udløse store effektivitetsforstyrrelser og manglende adgang til Windows-tjenester. Afhængigt af omfanget af ændringer kan det desuden gøre computersystemet helt meningsløst. På den anden side kan manipulation af registreringsværdier, der tilhører tredjeparts installerede applikationer, underminere dem. Nogle applikationer kan komme til kort at introducere helt, mens andre uventet kan stoppe med at fungere.
Denne specifikke minearbejder i sin nuværende version er koncentreret om at udvinde Monero cryptocurrency med en ændret version af XMRig CPU-minemotoren. Hvis kampagnerne bekræfter succesfulde, kan fremtidige varianter af Find.exe blive introduceret i fremtiden. Da de malware gør brug af software program susceptabilities at inficere target værter, det kan være en del af en usikker co-infektion med ransomware og også trojanske heste.
Fjernelse af Find.exe anbefales stærkt, da du risikerer ikke bare en enorm elektrisk energi regningen, hvis det fungerer på din computer, dog kan minearbejderen desuden udføre andre uønskede aktiviteter på den samt endda skade din pc permanent.
Find.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne Find.exe
TRIN 5. Find.exe er fjernet!
Video guide: Sådan bruger du GridinSoft Anti-Malware til at fjerne Find.exe
Hvordan undgår din pc fra at blive inficeret med “Find.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Find.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Find.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Find.exe”.