En ny, virkelig farlig cryptocurrency minervirus er identificeret af sikkerhedsforskere. den malware, hedder EC.exe kan forurene målrettet ved hjælp af en række metoder. Hovedideen bag EC.exe-miner er at bruge cryptocurrency miner-opgaver på computersystemer for mål for at få Monero-tokens til målpris. The end result of this miner is the raised electrical power costs and also if you leave it for longer time periods EC.exe may even damage your computers parts.
EC.exe: distributionssystemer Metoder
Det EC.exe malware makes use of two prominent techniques which are utilized to contaminate computer targets:
- Payload Levering gennem Prior Infektioner. If an older EC.exe malware is deployed on the sufferer systems it can automatically update itself or download and install a newer version. This is feasible using the built-in upgrade command which gets the release. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede server, som leverer malware kode. The downloaded virus will certainly get the name of a Windows service and be put in the “%systemet% temp” placere. Important properties and running system setup data are changed in order to allow a relentless and also quiet infection.
- Software programmet sårbarhed udnytter. The latest variation of the EC.exe malware have actually been found to be caused by the some exploits, almindeligvis forstået for at blive brugt i ransomware-angreb. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. If this condition is fulfilled it will scan the service as well as retrieve info about it, consisting of any kind of version as well as arrangement data. Exploits and also preferred username and password combinations might be done. When the make use of is activated versus the vulnerable code the miner will be released along with the backdoor. Dette vil danne en dobbelt infektion.
Aside from these techniques other techniques can be made use of too. Miners can be distributed by phishing emails that are sent in bulk in a SPAM-like way and depend upon social engineering tricks in order to perplex the targets into thinking that they have actually received a message from a legit solution or business. The infection documents can be either directly affixed or put in the body materials in multimedia web content or text web links.
The bad guys can likewise produce malicious touchdown web pages that can impersonate vendor download pages, software application download portals and also other frequently accessed areas. When they utilize similar appearing domain to legit addresses as well as safety certificates the customers might be coerced right into engaging with them. I nogle tilfælde kan blot åbning af dem forårsage minearbejdsinfektion.
One more technique would be to utilize payload carriers that can be spread out utilizing those methods or using data sharing networks, BitTorrent er blandt en af de mest populære. It is regularly used to distribute both reputable software program as well as data and pirate material. To af de mest populære transportfirmaer er følgende:
Various other techniques that can be considered by the criminals include using internet browser hijackers -harmful plugins which are made suitable with one of the most preferred internet browsers. They are submitted to the relevant databases with phony customer testimonials and developer credentials. Oftentimes oversigter kan omfatte skærmbilleder, video clips as well as intricate summaries promising wonderful function enhancements and efficiency optimizations. Nonetheless upon installment the behavior of the influenced internet browsers will certainly transform- individuals will locate that they will be rerouted to a hacker-controlled touchdown page and their setups may be changed – standard startside, online search engine as well as new tabs page.

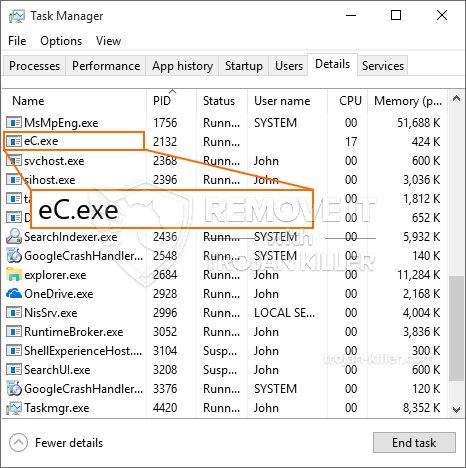
EC.exe: Analyse
The EC.exe malware is a timeless situation of a cryptocurrency miner which depending upon its configuration can cause a wide array of unsafe activities. Dens primære formål er at udføre komplicerede matematiske opgaver, der vil gøre brug af de tilgængelige systemressourcer: CPU, GPU, hukommelse og harddiskplads. Midlerne de fungerer, er ved at linke til en særlig web-server kaldet minedrift pulje, hvorfra den nødvendige kode er downloadet og installere. Så snart blandt de arbejdspladser downloades det vil helt sikkert blive påbegyndt samtidigt, flere forekomster kan være væk, så snart. Når en forudsat opgave er fuldført en anden vil helt sikkert blive hentet på sin plads, og det smuthul vil fortsætte indtil computeren er slukket, infektionen fået fjernet eller en mere ens begivenhed indtræffer. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres budgetter.
En farlig træk ved denne gruppe af malware er, at prøver som denne kan tage alle systemets kilder og også praktisk gøre målcomputeren meningsløst, indtil truslen er fjernet helt. Mange af dem har et vedholdende opsætning, der gør dem virkelig svært at fjerne. Disse kommandoer vil foretage ændringer også muligheder, configuration files and also Windows Registry values that will make the EC.exe malware beginning immediately as soon as the computer system is powered on. Adgang til healing fødevarer markeringer og også alternativer kan blive blokeret som giver flere hands-on fjernelse oversigter praktisk værdiløse.
Denne særlige infektion vil arrangement en Windows-tjeneste for sig selv, overholde den gennemførte sikkerhedsanalyse ther følgende aktiviteter er blevet observeret:
. Under minearbejder operationer den tilknyttede malware kan oprette forbindelse til i øjeblikket kører Windows løsninger og tredjeparts oprettet applikationer. Ved at gøre dette systemets ledere ikke kan observere, at de ressourcemæssige tons stammer fra en særskilt procedure.
| Navn | EC.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove EC.exe |

Disse slags malware infektioner er særligt effektive til at udføre avancerede kommandoer, hvis sat op, så. They are based on a modular framework allowing the criminal controllers to orchestrate all kinds of harmful actions. Blandt de fremtrædende eksempler er justeringen af registreringsdatabasen i Windows – modifications strings connected by the os can cause major performance disruptions and also the inability to accessibility Windows solutions. Relying on the range of adjustments it can additionally make the computer system totally unusable. On the various other hand adjustment of Registry values belonging to any kind of third-party set up applications can sabotage them. Some applications may stop working to launch completely while others can unexpectedly quit working.
This particular miner in its existing version is focused on mining the Monero cryptocurrency consisting of a customized version of XMRig CPU mining engine. If the projects show effective then future variations of the EC.exe can be introduced in the future. Da malware bruger softwareapplikationssårbarheder til at inficere målværter, det kan være en del af en usikker co-infektion med ransomware og også trojanske heste.
Removal of EC.exe is highly suggested, because you run the risk of not just a huge electrical power costs if it is running on your PC, however the miner may likewise execute various other unwanted tasks on it as well as also harm your PC completely.
EC.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove EC.exe
TRIN 5. EC.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove EC.exe
Hvordan undgår din pc fra at blive inficeret med “EC.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “EC.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “EC.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “EC.exe”.







