Et helt nyt, meget skadelig kryptovaluta minearbejder er faktisk blevet set af beskyttelsesforskere. den malware, hedder CONH0ST.EXE can contaminate target sufferers utilizing a selection of means. Hovedidéen bag CONH0ST.EXE minearbejderen er at anvende cryptocurrency minearbejderopgaver på ofrenes computere for at få Monero-tokens til syge bekostning. The outcome of this miner is the raised electrical energy bills and also if you leave it for longer periods of time CONH0ST.EXE might even damage your computer systems components.
CONH0ST.EXE: distributionssystemer Metoder
Det CONH0ST.EXE malware utilizes two prominent methods which are made use of to contaminate computer system targets:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older CONH0ST.EXE malware is deployed on the target systems it can immediately update itself or download a more recent variation. Dette er muligt ved hjælp af den integrerede opgraderingskommando, der opnår frigivelsen. This is done by attaching to a particular predefined hacker-controlled web server which offers the malware code. The downloaded infection will certainly acquire the name of a Windows solution and also be positioned in the “%systemet% temp” Beliggenhed. Crucial buildings and operating system setup data are changed in order to allow a relentless and also quiet infection.
- Software Application sårbarhed udnytter. The most current version of the CONH0ST.EXE malware have been discovered to be brought on by the some exploits, widely understood for being used in the ransomware assaults. Infektionerne er færdig ved at målrette åbne tjenester via TCP port. Strejkerne er automatiseret af en hacker-kontrolleret struktur, som søger efter hvis porten er åben. If this problem is satisfied it will scan the solution and also fetch details about it, inklusive eventuelle versions- og arrangementsdata. Ventures såvel som populære brugernavn og adgangskodeblandinger kan udføres. When the make use of is activated against the prone code the miner will be deployed along with the backdoor. Dette vil helt sikkert præsentere en dobbelt infektion.
In addition to these techniques various other approaches can be made use of too. Miners can be dispersed by phishing e-mails that are sent in bulk in a SPAM-like fashion as well as depend on social design techniques in order to perplex the victims right into thinking that they have gotten a message from a legitimate solution or firm. The infection documents can be either directly attached or put in the body components in multimedia web content or message web links.
The wrongdoers can likewise develop destructive landing pages that can pose vendor download pages, software download sites and various other regularly accessed areas. When they utilize similar sounding domain to legit addresses and protection certificates the individuals might be coerced right into connecting with them. Nogle gange blot at åbne dem kan aktivere minearbejder infektion.
An additional method would be to make use of haul carriers that can be spread using the above-mentioned methods or via data sharing networks, BitTorrent er en af de mest fremtrædende dem. It is regularly used to disperse both legit software program and also data and pirate content. Two of the most popular payload service providers are the following:
Other approaches that can be thought about by the crooks include using web browser hijackers -harmful plugins which are made suitable with the most preferred internet browsers. They are published to the relevant databases with phony user evaluations and programmer credentials. I mange tilfælde beskrivelserne kan bestå af screenshots, video clips and fancy summaries encouraging terrific attribute improvements and also efficiency optimizations. However upon installation the habits of the influenced web browsers will alter- customers will locate that they will certainly be rerouted to a hacker-controlled touchdown page and also their setups may be modified – standard startside, online søgemaskine samt helt nye faner webside.

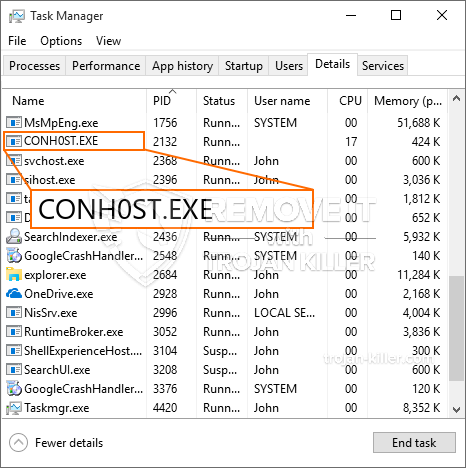
CONH0ST.EXE: Analyse
The CONH0ST.EXE malware is a traditional case of a cryptocurrency miner which relying on its configuration can cause a wide array of unsafe actions. Its main objective is to carry out complicated mathematical jobs that will certainly benefit from the readily available system sources: CPU, GPU, hukommelse og også harddisk værelse. The means they function is by connecting to a special web server called mining pool from where the required code is downloaded and install. As quickly as among the tasks is downloaded it will be begun at the same time, flere forekomster kan køres på én gang. When an offered task is completed another one will certainly be downloaded in its location and also the loop will proceed till the computer is powered off, infektionen er sluppet af med eller en yderligere sammenlignelig begivenhed sker. Cryptocurrency vil blive belønnet for de kriminelle controllere (hacking team eller en ensom cyberpunk) direkte til deres pengepung.
A hazardous quality of this group of malware is that samples such as this one can take all system sources and also almost make the sufferer computer system pointless till the risk has been entirely eliminated. Most of them include a relentless installment which makes them truly tough to get rid of. Disse kommandoer vil helt sikkert gøre ændringer også valg, setup data and Windows Registry values that will make the CONH0ST.EXE malware beginning automatically when the computer system is powered on. Access to recovery menus as well as options might be blocked which makes numerous manual removal overviews almost useless.
Denne specifikke infektion vil arrangementet en Windows-tjeneste for sig selv, overholdelse af den udførte sikkerhedsevaluering og overholdelse af handlinger er blevet observeret:
. During the miner procedures the associated malware can link to currently running Windows services and also third-party set up applications. By doing so the system administrators may not observe that the resource tons comes from a separate procedure.
| Navn | CONH0ST.EXE |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove CONH0ST.EXE |

These kind of malware infections are specifically efficient at carrying out advanced commands if configured so. They are based on a modular framework permitting the criminal controllers to manage all type of dangerous behavior. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – adjustments strings related by the operating system can trigger major performance interruptions and also the failure to access Windows services. Afhængig af omfanget af tilpasninger, som den kan ligeledes gøre computeren helt meningsløst. On the other hand adjustment of Registry worths coming from any type of third-party set up applications can undermine them. Some applications might fall short to introduce entirely while others can all of a sudden stop working.
This certain miner in its current variation is focused on mining the Monero cryptocurrency having a changed version of XMRig CPU mining engine. If the campaigns prove effective after that future versions of the CONH0ST.EXE can be introduced in the future. Da malware bruger softwarefølsomhed til at inficere målværter, det kan være bestanddel af en farlig co-infektion med ransomware og trojanske heste.
Removal of CONH0ST.EXE is strongly advised, given that you take the chance of not only a huge electrical power expense if it is working on your PC, however the miner may likewise execute other unwanted activities on it as well as also harm your COMPUTER completely.
CONH0ST.EXE removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove CONH0ST.EXE
TRIN 5. CONH0ST.EXE Removed!
Video guide: How to use GridinSoft Anti-Malware for remove CONH0ST.EXE
Hvordan undgår din pc fra at blive inficeret med “CONH0ST.EXE” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “CONH0ST.EXE”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “CONH0ST.EXE”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “CONH0ST.EXE”.







