En ny, meget farlig cryptocurrency minearbejder virus er blevet identificeret af sikkerhedsforskere. den malware, hedder Chkdiskmgr.exe can infect target sufferers using a variety of ways. Essensen bag Chkdiskmgr.exe minearbejderen er at anvende cryptocurrency minearbejderopgaver på computerens mål for at erhverve Monero-symboler til målomkostninger. The result of this miner is the elevated power expenses as well as if you leave it for longer periods of time Chkdiskmgr.exe might also damage your computers parts.
Chkdiskmgr.exe: distributionssystemer Metoder
Det Chkdiskmgr.exe malware utilizes two popular techniques which are used to infect computer system targets:
- Payload Levering hjælp Prior Infektioner. If an older Chkdiskmgr.exe malware is deployed on the target systems it can immediately update itself or download and install a more recent variation. This is possible through the built-in update command which obtains the release. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den downloadede og installerede virus får navnet på en Windows-tjeneste og placeres også i “%systemet% temp” Beliggenhed. Vital homes and running system setup data are altered in order to allow a relentless and also quiet infection.
- Software programmet sårbarhed udnytter. The latest variation of the Chkdiskmgr.exe malware have actually been located to be caused by the some exploits, berømt anerkendt for at blive gjort brug af i de ransomware strejker. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Angrebene er automatiseret af en hacker-kontrolleret struktur, som opsøger hvis porten er åben. If this condition is satisfied it will check the solution and recover details concerning it, bestående af en hvilken som helst form for versionen samt konfigurationsoplysninger. Udnyttelse og fremtrædende brugernavn og adgangskodekombinationer kan udføres. When the make use of is caused against the vulnerable code the miner will certainly be released together with the backdoor. Dette vil helt sikkert give en dobbelt infektion.
Apart from these methods various other approaches can be made use of also. Miners can be distributed by phishing e-mails that are sent wholesale in a SPAM-like manner and also depend upon social engineering techniques in order to perplex the sufferers into believing that they have obtained a message from a legit service or firm. The infection documents can be either straight attached or put in the body components in multimedia material or message web links.
The bad guys can additionally produce destructive landing pages that can impersonate vendor download pages, software program download websites and also various other regularly accessed areas. When they make use of similar seeming domain to legit addresses as well as safety and security certifications the individuals might be coerced right into interacting with them. I nogle tilfælde blot at åbne dem kan modregne minearbejder infektion.
An additional approach would be to make use of payload service providers that can be spread out making use of those approaches or via documents sharing networks, BitTorrent er en af de mest fremtrædende dem. It is frequently used to distribute both reputable software program and also files as well as pirate content. 2 af en af de mest populære transportudbydere er følgende:
Other techniques that can be thought about by the lawbreakers consist of making use of internet browser hijackers -harmful plugins which are made suitable with the most popular web internet browsers. They are uploaded to the relevant databases with phony customer reviews as well as programmer credentials. I mange tilfælde beskrivelserne kan omfatte skærmbilleder, videos and also fancy descriptions promising terrific attribute improvements and efficiency optimizations. Nonetheless upon installation the actions of the impacted browsers will transform- customers will locate that they will certainly be rerouted to a hacker-controlled touchdown web page and their settings could be changed – standard webside, online søgemaskine og også ny side faner.

Chkdiskmgr.exe: Analyse
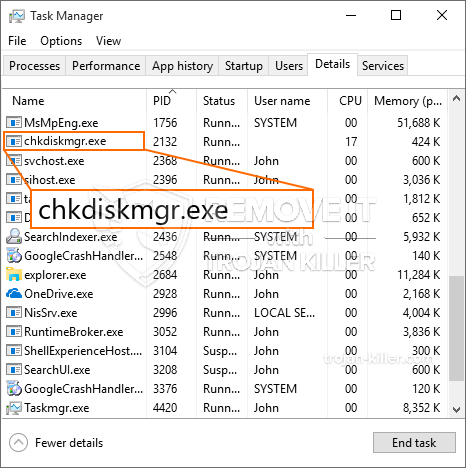
The Chkdiskmgr.exe malware is a classic situation of a cryptocurrency miner which depending upon its arrangement can cause a wide variety of harmful actions. Its major goal is to do intricate mathematical jobs that will make use of the offered system sources: CPU, GPU, hukommelse såvel som harddiskområdet. The means they function is by linking to a special server called mining swimming pool from where the called for code is downloaded. Så hurtigt som et af jobs er downloadet, vil det blive påbegyndt med det samme, flere omstændigheder kan udføres så snart. When an offered job is finished one more one will be downloaded and install in its place as well as the loophole will certainly continue till the computer system is powered off, infektionen elimineres, eller der finder en anden sammenlignelig lejlighed sted. Cryptocurrency vil blive kompenseret for de kriminelle controllere (hacking gruppe eller en ensom cyberpunk) direkte til deres punge.
A hazardous feature of this group of malware is that examples such as this one can take all system sources and practically make the victim computer system unusable till the hazard has actually been totally eliminated. A lot of them feature a persistent setup that makes them actually challenging to eliminate. Disse kommandoer vil helt sikkert foretage ændringer også alternativer, arrangement data and Windows Registry values that will certainly make the Chkdiskmgr.exe malware begin automatically once the computer is powered on. Accessibility to healing menus and also options may be blocked which renders several hand-operated elimination overviews practically ineffective.
Denne særlige infektion vil bestemt konfigurere en Windows-tjeneste for sig selv, complying with the carried out safety analysis ther following actions have been observed:
. During the miner operations the connected malware can connect to currently running Windows solutions as well as third-party set up applications. Ved at gøre dette kan systemadministratorerne muligvis ikke observere, at kildelotterne stammer fra en anden proces.
| Navn | Chkdiskmgr.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Chkdiskmgr.exe |

These sort of malware infections are particularly efficient at carrying out innovative commands if set up so. They are based on a modular framework allowing the criminal controllers to manage all type of harmful behavior. One of the prominent examples is the alteration of the Windows Registry – adjustments strings connected by the os can trigger serious performance disturbances and the inability to accessibility Windows services. Depending on the extent of adjustments it can also make the computer totally unusable. On the various other hand adjustment of Registry values coming from any third-party installed applications can sabotage them. Nogle programmer kan undlade at indføre helt, mens andre pludselig kan stoppe med at arbejde.
This particular miner in its present variation is concentrated on extracting the Monero cryptocurrency including a customized variation of XMRig CPU mining engine. If the campaigns show effective after that future versions of the Chkdiskmgr.exe can be released in the future. Da malware udnytter sårbarheder i software forurene mål værter, det kan være del af en farlig co-infektion med ransomware samt trojanske heste.
Elimination of Chkdiskmgr.exe is strongly suggested, because you run the risk of not just a large electrical power bill if it is working on your COMPUTER, yet the miner might also carry out other undesirable activities on it as well as even damage your PC permanently.
Chkdiskmgr.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Chkdiskmgr.exe
TRIN 5. Chkdiskmgr.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Chkdiskmgr.exe
Hvordan undgår din pc fra at blive inficeret med “Chkdiskmgr.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Chkdiskmgr.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Chkdiskmgr.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Chkdiskmgr.exe”.







