En ny, meget farligt cryptocurrency minearbejder infektion rent faktisk er blevet fundet af sikkerhedsmæssige forskere. den malware, hedder Cex9.exe kan inficere ofre mål udnytte et udvalg af midler. Essensen bag Cex9.exe-minearbejderen er at anvende cryptocurrency-minearbejder på computersystemer for mål for at erhverve Monero-symboler til målomkostninger. The outcome of this miner is the raised power bills as well as if you leave it for longer periods of time Cex9.exe might also harm your computers parts.
Cex9.exe: distributionssystemer Metoder
Det Cex9.exe malware anvendelser 2 foretrukne tilgange, der bruges til at forurene computermål:
- Payload Levering hjælp Prior Infektioner. If an older Cex9.exe malware is released on the victim systems it can immediately update itself or download and install a newer variation. This is feasible using the built-in upgrade command which obtains the release. Dette gøres ved at linke til en bestemt foruddefineret hacker-styret webserver, der leverer malware-koden. The downloaded infection will get the name of a Windows service as well as be positioned in the “%systemet% temp” placere. Vital homes and running system setup files are changed in order to allow a relentless and quiet infection.
- Software sårbarhed udnytter. The most current version of the Cex9.exe malware have been located to be caused by the some exploits, populært forstået for at blive brugt i ransomware strejker. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Overgrebene er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. If this problem is satisfied it will check the solution and recover information about it, bestående af enhver version samt konfigurationsdata. Ventures and preferred username and password mixes might be done. Når brugen af udløses i forhold til den sårbare kode, vil minearbejderen helt sikkert blive indsat som supplement til bagdøren. Dette vil helt sikkert give en dobbelt infektion.
Aside from these approaches various other strategies can be made use of too. Miners can be dispersed by phishing emails that are sent out in bulk in a SPAM-like way and rely on social design techniques in order to perplex the sufferers into thinking that they have actually received a message from a genuine solution or business. The infection documents can be either straight connected or placed in the body components in multimedia material or message links.
The bad guys can additionally create malicious landing pages that can pose supplier download and install pages, websteder til download af softwareprogrammer samt forskellige andre ofte tilgængelige steder. When they utilize comparable appearing domain to legit addresses as well as safety and security certificates the users might be persuaded right into communicating with them. Nogle gange bare åbne dem kan aktivere minearbejder infektion.
One more method would certainly be to make use of haul providers that can be spread out utilizing those techniques or via file sharing networks, BitTorrent er blot en af de mest foretrukne dem. It is often used to distribute both genuine software program and also documents and pirate content. 2 af de mest foretrukne nyttelast udbydere er følgende:
Various other techniques that can be considered by the bad guys consist of making use of internet browser hijackers -hazardous plugins which are made compatible with the most popular internet browsers. They are posted to the appropriate repositories with fake individual reviews and also designer credentials. I mange tilfælde beskrivelserne kan bestå af screenshots, videos and intricate descriptions appealing excellent attribute improvements and efficiency optimizations. Nevertheless upon installment the habits of the affected web browsers will change- individuals will discover that they will certainly be rerouted to a hacker-controlled touchdown page and also their settings could be modified – standard webside, online søgemaskine og helt nye faner webside.
Cex9.exe: Analyse
The Cex9.exe malware is a traditional situation of a cryptocurrency miner which depending on its configuration can create a wide variety of harmful activities. Its main goal is to do complicated mathematical jobs that will certainly make use of the offered system sources: CPU, GPU, hukommelse samt harddisk plads. The means they function is by connecting to an unique server called mining swimming pool where the required code is downloaded and install. Så snart blandt de opgaver, der er downloadet det vil helt sikkert blive begyndt på en gang, flere omstændigheder kan være væk, når. When a given job is completed one more one will be downloaded and install in its location and the loophole will certainly continue till the computer system is powered off, infektionen elimineres eller en supplerende lignende arrangement finder sted. Cryptocurrency vil helt sikkert blive belønnet for de kriminelle controllere (hacking gruppe eller en ensom hacker) direkte til deres punge.
An unsafe feature of this group of malware is that examples such as this one can take all system resources and practically make the sufferer computer system pointless until the threat has actually been completely gotten rid of. A lot of them include a consistent setup that makes them truly challenging to eliminate. Disse kommandoer vil foretage ændringer også muligheder, setup files as well as Windows Registry values that will certainly make the Cex9.exe malware start immediately when the computer is powered on. Accessibility to healing food selections and options may be blocked which makes several hands-on removal overviews practically pointless.
Denne særlige infektion vil bestemt konfigurere en Windows-tjeneste for sig selv, efter den udførte sikkerhedsanalyse ther følgende aktiviteter er blevet observeret:
. During the miner procedures the linked malware can attach to currently running Windows services as well as third-party set up applications. By doing so the system administrators may not observe that the source load originates from a separate process.
| Navn | Cex9.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Cex9.exe |
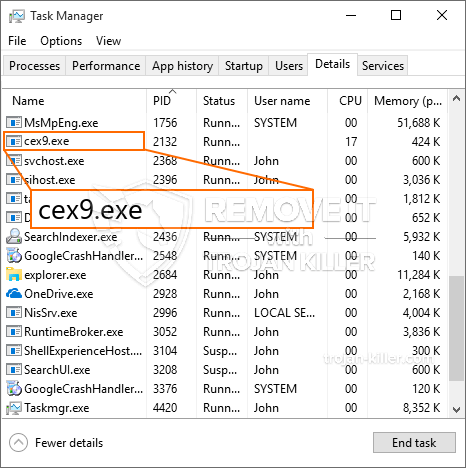
id =”82919″ align =”aligncenter” width =”600″] Cex9.exe
Cex9.exe
Denne type malwareinfektioner er især effektive til at udføre sofistikerede kommandoer, hvis de er konfigureret således. De er baseret på en modulær struktur, der gør det muligt for de kriminelle kontrollere at styre alle slags farlige handlinger. Blandt de prominente tilfælde er ændringen af registreringsdatabasen i Windows – ændringer strenge forbundet med operativsystemet kan udløse alvorlige ydelsesforstyrrelser såvel som manglende evne til tilgængelighed Windows-tjenester. Afhængigt af omfanget af ændringer kan det desuden gøre computersystemet helt meningsløst. På den anden side kan kontrol af registreringsværdier, der kommer fra enhver form for installerede tredjepartsapplikationer, underminere dem. Nogle applikationer kan være korte til at introducere fuldstændigt, mens andre pludselig kan stoppe med at arbejde.
Denne bestemte minearbejder i sin nuværende version er fokuseret på at udvinde Monero-kryptovalutaen inklusive en tilpasset variation af XMRig CPU-minedriftmotoren. If the projects show effective then future variations of the Cex9.exe can be released in the future. Da malware bruger software susceptabilities forurene mål værter, det kan være en del af en skadelig co-infektion med ransomware og trojanere.
Removal of Cex9.exe is highly recommended, i betragtning af at du ikke kun risikerer store elomkostninger, hvis den fungerer på din COMPUTER, men minearbejderen kan også udføre andre uønskede opgaver på den og også endda beskadige din pc fuldstændigt.
Cex9.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Cex9.exe
TRIN 5. Cex9.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Cex9.exe
Hvordan undgår din pc fra at blive inficeret med “Cex9.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Cex9.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Cex9.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Cex9.exe”.