Et helt nyt, extremely harmful cryptocurrency miner infection has actually been discovered by safety and security researchers. den malware, hedder CalcX.exe kan inficere målramte ved at bruge et udvalg af metoder. The main point behind the CalcX.exe miner is to employ cryptocurrency miner tasks on the computer systems of targets in order to acquire Monero symbols at targets expense. The outcome of this miner is the raised power expenses as well as if you leave it for longer periods of time CalcX.exe may also damage your computer systems components.
CalcX.exe: distributionssystemer Metoder
Det CalcX.exe malware udnytter 2 foretrukne fremgangsmåder, der er gjort brug af at inficere edb-system mål:
- Nyttelast Levering ved hjælp af kendte Infektioner. If an older CalcX.exe malware is deployed on the target systems it can instantly update itself or download and install a more recent version. Dette er muligt gennem den indbyggede opgradering kommando, som opnår frigivelse. Dette gøres ved at forbinde til en bestemt foruddefineret hacker-kontrollerede webserver, der giver malware kode. Den downloadede og installerede infektion vil helt sikkert få navnet på en Windows -løsning og også blive sat i “%systemet% temp” areal. Afgørende bolig- eller erhvervsejendomme og også filer til operativsystemarrangementer transformeres for at muliggøre en nådesløs såvel som stille infektion.
- Software programmet sårbarhed udnytter. The most current variation of the CalcX.exe malware have been found to be triggered by the some exploits, populært anerkendt for at blive udnyttet i de ransomware angreb. Infektionerne er færdig ved at målrette åbne løsninger ved hjælp af TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som opsøger hvis porten er åben. Hvis dette problem er løst, vil det scanne løsningen og også gendanne oplysninger om det, inklusive enhver form for variation og konfigurationsinformation. Ventures og også prominente brugernavn og adgangskode kombinationer kan gøres. Når udnyttelsen udløses mod den tilbøjelige kode frigives minearbejderen sammen med bagdøren. Dette vil danne en dobbelt infektion.
Ud over disse teknikker kan forskellige andre tilgange også anvendes. Minearbejdere kan distribueres ved phishing-e-mails, der sendes engros på en spam-lignende måde, samt stole på social engineering-tricks for at forvirre målene lige til at tro, at de har modtaget en besked fra en legitim service eller virksomhed. Infektionsdataene kan enten vedhæftes direkte eller sættes i kropskomponenterne i multimediewebindhold eller meddelelseslink.
De onde kan ligeledes udvikle destruktive touchdown -websider, der kan efterligne sælger download og installere websider, softwareoverførselswebsteder og også forskellige andre steder, der regelmæssigt tilgås. Når de bruger lignende tilsyneladende domæne til legitime adresser og også sikkerhedscertificeringer, kan kunderne blive skubbet direkte ind i at interagere med dem. I nogle tilfælde bare åbne dem kan forårsage minearbejder infektion.
En yderligere teknik ville helt sikkert være at udnytte nyttelastbærere, der kan spredes ved hjælp af disse metoder eller via datadelingsnetværk, BitTorrent er blot en af en af de mest foretrukne dem. Det bruges ofte til at distribuere både ægte softwareprogram og dokumenter samt piratindhold. 2 af en af de mest prominente udbydere af nyttelasttjenester er følgende:
Forskellige andre teknikker, som lovbryderne kan tænke på, omfatter brug af webbrowser -kaprere -farlige plugins, der er gjort egnede til en af de mest fremtrædende webbrowsere. De sendes til de relevante lagre med falske brugerevalueringer og designerkvalifikationer. I mange tilfælde resuméerne kan bestå af screenshots, videoer og indviklede resuméer, der tiltrækker fremragende funktionsforbedringer samt effektivitetsoptimeringer. Ikke desto mindre ved afdrag vil vanerne hos de påvirkede internetbrowsere ændre sig- brugere vil helt sikkert opdage, at de vil blive omdirigeret til en hacker-kontrolleret touchdown-webside, såvel som deres indstillinger kan blive ændret – standard startside, online søgemaskine samt helt nye faner webside.

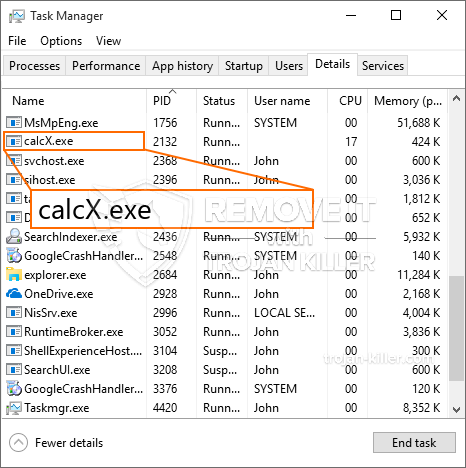
CalcX.exe: Analyse
The CalcX.exe malware is a traditional instance of a cryptocurrency miner which depending upon its configuration can cause a wide array of hazardous actions. Dets vigtigste mål er at udføre indviklede matematiske opgaver, der får mest ud af de tilbudte systemressourcer: CPU, GPU, hukommelse og også harddisk område. De midler, de arbejder, er ved at linke til en speciel webserver kaldet minedrift, hvor den kaldte kode downloades. Så snart der er downloadet af jobene, startes det samtidig, flere omstændigheder kan udføres på hvornår. Når en bestemt opgave er afsluttet, vil der blive downloadet endnu en i sit område, og smuthullet vil helt sikkert fortsætte, indtil computersystemet er slukket, infektionen fjernes, eller en yderligere lignende begivenhed finder sted. Cryptocurrency vil helt sikkert blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres punge.
En farlig egenskab ved denne gruppe af malware er, at eksempler som denne kan tage alle systemressourcer og også praktisk talt gøre den syge computer meningsløs, indtil truslen er blevet helt fjernet. De fleste af dem har en ubarmhjertig installation, der gør dem faktisk udfordrende at fjerne. Disse kommandoer gør ændringer også valg, arrangement data and also Windows Registry values that will make the CalcX.exe malware start immediately when the computer is powered on. Tilgængelighed til helbredende madvalg og valg kan være blokeret, hvilket gør masser af håndbetjente fjernelsesoversigter næsten ubrugelige.
Denne særlige infektion vil helt sikkert arrangement en Windows løsning for sig selv, overholdelse af den udførte beskyttelsesanalyse der overholdes aktiviteter er blevet observeret:
. Under minearbejder operationer den tilhørende malware kan knytte til i øjeblikket kører Windows-tjenester samt tredjeparts monteret applikationer. Ved at gøre dette kan systemadministratorerne muligvis ikke observere, at kildebelastningen kommer fra en separat procedure.
| Navn | CalcX.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove CalcX.exe |

These sort of malware infections are specifically efficient at accomplishing advanced commands if configured so. They are based on a modular structure enabling the criminal controllers to manage all type of unsafe behavior. Blandt de foretrukne eksempler er den ændring af Windows-registreringsdatabasen – alterations strings connected by the operating system can create serious efficiency disruptions as well as the failure to accessibility Windows services. Relying on the scope of changes it can likewise make the computer totally unusable. On the other hand adjustment of Registry values coming from any third-party installed applications can undermine them. Nogle programmer kan stoppe med at arbejde for at indføre helt, mens andre pludselig kan stoppe med at arbejde.
This certain miner in its present variation is focused on extracting the Monero cryptocurrency including a changed version of XMRig CPU mining engine. If the projects verify successful after that future variations of the CalcX.exe can be introduced in the future. Da malware bruger software program susceptabilities at forurene mål værter, det kan være en del af en usikker co-infektion med ransomware og trojanske heste.
Removal of CalcX.exe is strongly recommended, considering that you risk not just a big power bill if it is operating on your COMPUTER, yet the miner may also carry out other undesirable tasks on it and even harm your COMPUTER permanently.
CalcX.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove CalcX.exe
TRIN 5. CalcX.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove CalcX.exe
Hvordan undgår din pc fra at blive inficeret med “CalcX.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “CalcX.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “CalcX.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “CalcX.exe”.







