Et helt nyt, virkelig usikker kryptokurverminerinfektion er blevet opdaget af beskyttelsesforskere. den malware, hedder Bvhost.exe kan forurene målrettet ved hjælp af en række metoder. The essence behind the Bvhost.exe miner is to use cryptocurrency miner activities on the computer systems of targets in order to obtain Monero symbols at sufferers expenditure. The result of this miner is the raised electrical power expenses and also if you leave it for longer amount of times Bvhost.exe might even harm your computers parts.
Bvhost.exe: distributionssystemer Metoder
Det Bvhost.exe malware udnytter 2 preferred techniques which are made use of to infect computer targets:
- Payload Levering hjælp Prior Infektioner. If an older Bvhost.exe malware is released on the target systems it can instantly upgrade itself or download and install a newer variation. Dette er muligt ved hjælp af den integrerede opdateringskommando, der erhverver frigivelsen. Dette gøres ved at knytte sig til en specifik foruddefineret hacker-styret webserver, som tilbyder malware-koden. The downloaded virus will acquire the name of a Windows service and be positioned in the “%systemet% temp” areal. Essential properties and running system arrangement documents are transformed in order to allow a relentless and silent infection.
- Software sårbarhed udnytter. The latest variation of the Bvhost.exe malware have been located to be caused by the some ventures, kendt for at være brugt i ransomware-strejker. Infektionerne er færdig ved at målrette åbne tjenester ved hjælp af TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som opsøger hvis porten er åben. If this condition is satisfied it will scan the solution and also recover details regarding it, herunder enhver form for version, og også arrangement oplysninger. Udnytter og også foretrukne brugernavn og adgangskode blandinger kan gøres. When the manipulate is set off versus the at risk code the miner will be released together with the backdoor. Dette vil præsentere en dobbelt infektion.
Apart from these approaches various other techniques can be utilized also. Miners can be dispersed by phishing emails that are sent wholesale in a SPAM-like fashion as well as rely on social design tricks in order to perplex the sufferers right into thinking that they have obtained a message from a legit solution or business. The infection documents can be either directly attached or inserted in the body components in multimedia material or text web links.
The crooks can likewise create destructive landing pages that can impersonate vendor download web pages, software program download sites and also other often accessed areas. When they use comparable seeming domain names to genuine addresses and also protection certificates the users may be pushed right into engaging with them. Nogle gange kan blot åbning af dem forårsage minerinfektionen.
Another method would certainly be to utilize haul carriers that can be spread making use of those methods or by means of data sharing networks, BitTorrent er blandt en af de mest fremtrædende dem. It is regularly utilized to disperse both reputable software program and also documents and pirate web content. 2 of the most prominent payload carriers are the following:
Various other methods that can be taken into consideration by the lawbreakers consist of the use of web browser hijackers -hazardous plugins which are made compatible with the most popular internet browsers. They are uploaded to the appropriate repositories with phony user reviews and designer credentials. I mange tilfælde resuméerne kan omfatte skærmbilleder, videos and elaborate summaries encouraging excellent function improvements and performance optimizations. Nonetheless upon installment the actions of the influenced browsers will certainly transform- customers will find that they will certainly be redirected to a hacker-controlled landing page and their setups might be altered – standard webside, online søgemaskine samt helt nye faner webside.

Bvhost.exe: Analyse
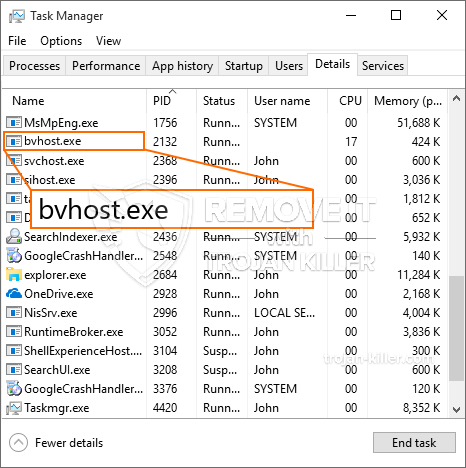
The Bvhost.exe malware is a classic case of a cryptocurrency miner which depending upon its configuration can trigger a variety of harmful actions. Dets primære mål er at udføre indviklede matematiske opgaver, der vil drage fordel af de tilgængelige systemkilder: CPU, GPU, hukommelse samt harddisk område. Den måde, de fungerer på, er ved at tilslutte sig en speciel server kaldet mining pool, hvor den nødvendige kode downloades. Så snart der er downloadet af opgaverne, startes det på samme tid, flere forhold kan køres på, så snart. Når en opgave er fuldført, vil en anden blive downloadet på dens placering, og løkken vil helt sikkert fortsætte, indtil computeren slukkes, infektionen elimineres, eller der finder en anden sammenlignelig lejlighed sted. Cryptocurrency vil blive tildelt de kriminelle controllere (hacking team eller en ensom hacker) direkte til deres pengepung.
En farlig egenskab ved denne klassificering af malware er, at prøver svarende til denne kan tage alle systemressourcer og også praktisk talt gøre ofrets computer ubrugelig, indtil faren er helt elimineret. Mange af dem inkluderer en ensartet installation, som gør dem faktisk svære at slippe af med. Disse kommandoer vil foretage ændringer til at starte alternativer, arrangement data and also Windows Registry values that will make the Bvhost.exe malware start automatically as soon as the computer system is powered on. Adgang til helbredende madvalg såvel som alternativer kan blive blokeret, hvilket gør adskillige manuelle elimineringsvejledninger praktisk talt ubrugelige.
Denne specifikke infektion vil helt sikkert sætte en Windows-tjeneste for sig selv, i overensstemmelse med den udførte sikkerhedsanalyse, er følgende handlinger faktisk blevet observeret:
. I løbet af minearbejder procedurer den tilhørende malware kan oprette forbindelse til i øjeblikket kører Windows-tjenester og også tredjeparts installerede applikationer. Ved at gøre det kan systemadministratorerne muligvis ikke observere, at ressourcepartierne stammer fra en separat proces.
| Navn | Bvhost.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware to detect and remove Bvhost.exe |

Disse slags malware infektioner er specielt pålidelige på at udføre avancerede kommandoer hvis det er konfigureret, så. De er baseret på en modulær ramme, der giver de kriminelle controllere at orkestrere alle former for skadelige vaner. Blandt de populære forekomster er ændringen af registreringsdatabasen i Windows – modifikationer strenge forbundet af OS kan udløse betydelige afbrydelser ydeevne samt den manglende evne til tilgængelighed Windows-tjenester. Afhængig af omfanget af ændringer det kan ligeledes gøre computeren helt ubrugelig. På den anden side manipulation af Registry worths kommer fra enhver form for tredjepart monteret programmer kan sabotere dem. Nogle programmer kan mislykkes at frigive helt, mens andre kan lige pludselig afslutte arbejdet.
Denne specifikke minearbejder i sin nuværende variation er koncentreret om minedrift Monero cryptocurrency herunder en tilpasset variation af XMRig CPU minedrift motor. If the projects verify successful then future variations of the Bvhost.exe can be introduced in the future. Da malware gør brug af software program sårbarheder til at forurene mål værter, det kan være en del af et farligt co-infektion med ransomware samt trojanske heste.
Removal of Bvhost.exe is strongly recommended, da du risikerer ikke kun en stor elektrisk strøm regningen, hvis det fungerer på din computer, endnu minearbejder kan derudover udføre forskellige andre uønskede opgaver på det såvel som også skade din computer helt.
Bvhost.exe removal process
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” button to remove Bvhost.exe
TRIN 5. Bvhost.exe Removed!
Video guide: How to use GridinSoft Anti-Malware for remove Bvhost.exe
Hvordan undgår din pc fra at blive inficeret med “Bvhost.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “Bvhost.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “Bvhost.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “Bvhost.exe”.







