En ny, virkelig usikker cryptocurrency miner infektion er faktisk blevet fundet af sikkerhedsforskere. den malware, hedder BRTSvc.exe kan forurene mållidende ved hjælp af en række metoder. Essensen bag BRTSvc.exe-miner er at bruge cryptocurrency miner-opgaver på computersystemerne for mål for at få Monero-symboler til de ramte omkostninger.. Slutresultatet af denne minearbejder er de rejste udgifter til elektrisk strøm, og også hvis du forlader det i længere perioder, kan BRTSvc.exe endda skade dine computersystemkomponenter.
BRTSvc.exe: distributionssystemer Metoder
Det BRTSvc.exe malware gør brug af 2 foretrukne fremgangsmåder, der anvendes til kontaminere computer mål:
- Payload Levering via Prior Infektioner. Hvis en ældre BRTSvc.exe malware er installeret på de syge systemer, kan den automatisk opdatere sig selv eller downloade en nyere variation. Dette er muligt gennem den indbyggede opgradering kommando, som får frigivelsen. Dette gøres ved at linke til en bestemt foruddefineret hacker-kontrollerede webserver, der tilvejebringer den Malwarekoden. Den hentet og installere infektion vil helt sikkert erhverve navnet på en Windows-løsning og også være placeret i “%systemet% temp” areal. Vitale boliger samt operativsystem arrangement data transformeres for at muliggøre en vedvarende samt tavse infektion.
- Software Application sårbarhed udnytter. Den seneste version af malware BRTSvc.exe har faktisk vist sig at være forårsaget af nogle ventures, bredt forstået for at blive udnyttet i de ransomware angreb. Infektionerne er færdig ved at målrette åbne løsninger gennem TCP port. Strejkerne er automatiseret af en hacker-kontrolleret ramme som søger efter hvis porten er åben. Hvis problemet er opfyldt, vil skanne løsningen og få også oplysninger om det, herunder enhver form for ændring samt konfigurationsinformation. Ventures og populære brugernavn og også adgangskoder kan gøres. Når gøre brug af er forårsaget versus den sårbare kode for minearbejder vil blive frigivet sammen med bagdør. Dette vil helt sikkert give det en dobbelt infektion.
Ud over disse metoder forskellige andre tilgange kan gøres brug af for. Minearbejdere kan distribueres af phishing e-mails, der sendes ud gros i et SPAM-lignende måde, samt afhænge af sociale design teknikker for at forvirre de mål lige til at tro, at de har modtaget en besked fra en ægte service eller virksomhed. De virus filer kan enten lige fastgjort eller indsat i kroppen komponenter i multimedie materiale eller besked links.
De slyngler kan ligeledes producere ondsindede touchdown websider, der kan efterligner leverandør downloade websider, software ansøgning downloade portaler samt forskellige andre ofte adgang steder. Når de bruger lignende klingende domæne til ægte adresser samt sikkerhedscertifikater kunderne kunne blive skubbet ind i dialog med dem. I nogle tilfælde bare åbne dem kan udløse minearbejder infektion.
Endnu en metode ville være at bruge distancer udbydere, der kan spredes ud ved hjælp af ovennævnte teknikker eller via dokumenter deler netværk, BitTorrent er blot en af de mest foretrukne dem. Det er ofte brugt til at distribuere både velrenommeret software program samt dokumenter samt pirat materiale. 2 af en af de mest foretrukne nyttelast tjenesteydere er følgende:
Forskellige andre teknikker, der kan tages i betragtning ved de kriminelle består i at gøre brug af browser flykaprere -hazardous plugins, der er lavet i overensstemmelse med den mest foretrukne web internet-browsere. De er indsendt til relevante databaser med falske brugerkonti Begejstring og også designer legitimationsoplysninger. I mange tilfælde beskrivelserne kan omfatte skærmbilleder, videoer samt udarbejde resuméer lovende vidunderlige funktion forbedringer og ydeevne optimeringer. Ikke desto mindre efter installation handlinger de berørte webbrowsere vil helt sikkert ændre- brugere vil opleve, at de vil blive omdirigeret til en hacker-kontrolleret landing webside og deres opsætninger kunne ændres – standard webside, søgemaskine samt helt nye faner webside.

BRTSvc.exe: Analyse
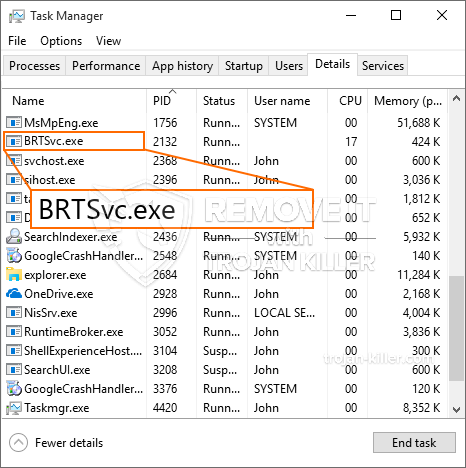
BRTSvc.exe-malware er en tidløs situation for en cryptocurrency-miner, der afhængigt af dens arrangement kan forårsage en lang række farlige aktiviteter. Dets hovedmål er at udføre komplicerede matematiske opgaver, der helt sikkert vil gøre brug af de tilbudte systemkilder: CPU, GPU, hukommelse og harddiskområde. Metoden, de arbejder, er ved at linke til en speciel webserver kaldet mining pool, hvorfra den kaldte kode downloades og installeres. Så snart blandt de arbejdspladser downloades det vil helt sikkert blive påbegyndt samtidigt, adskillige tilfælde kan køres på når. Når et angivet job er afsluttet, downloades et andet i sit område, så lænken fortsætter, indtil computeren er slukket, infektionen elimineres, eller en anden sammenlignelig begivenhed forekommer. Cryptocurrency vil blive kompenseret for de kriminelle controllere (hacking gruppe eller en enkelt cyberpunk) direkte til deres tegnebøger.
En skadelig egenskab ved denne gruppe malware er, at eksempler som denne kan tage alle systemkilder og også næsten gøre den syge computer meningsløs, indtil truslen faktisk er blevet fjernet. Mange af dem inkluderer en ensartet installation, der gør dem virkelig udfordrende at fjerne. Disse kommandoer vil helt sikkert foretage ændringer også muligheder, installationsdata og Windows-registerværdier, der helt sikkert får BRTSvc.exe malware til at starte automatisk, når computeren er tændt. Tilgængeligheden til helbredende menuer og valg kan blive blokeret, hvilket gør adskillige manuelle eliminationsvejledninger næsten værdiløse.
Denne særlige infektion vil helt sikkert arrangement en Windows løsning for sig selv, overholdelse af den udførte sikkerhedsanalyse er der fulgt handlinger:
. I løbet af mineroperationer kan den tilknyttede malware knyttes til aktuelt kørende Windows-tjenester og opsætningsapplikationer fra tredjepart. Dermed observerer systemadministratorerne muligvis ikke, at kildepartierne stammer fra en anden procedure.
| Navn | BRTSvc.exe |
|---|---|
| Kategori | Trojan |
| Sub-kategori | Cryptocurrency Miner |
| farer | Høj CPU-forbrug, reduktion Internet hastighed, PC nedbrud og fryser og etc. |
| Hovedformål | For at tjene penge til cyberkriminelle |
| Fordeling | Torrents, Gratis spil, Cracked apps, E-mail, tvivlsomme hjemmesider, udnytter |
| Fjernelse | Installere GridinSoft Anti-Malware til at registrere og fjerne BRTSvc.exe |

Denne type malware-infektioner er især effektive til at udføre avancerede kommandoer, hvis de er konfigureret sådan. De er baseret på en modulopbygget ramme, der gør det muligt for de kriminelle kontrollører at koordinere alle typer farlige vaner. Et af de foretrukne eksempler er modifikationen af Windows-registreringsdatabasen – justeringer strenge relateret til operativsystemet kan udløse alvorlige effektivitetsforstyrrelser og manglende evne til at få adgang til Windows-tjenester. Afhængig af omfanget af justeringer kan det desuden gøre computeren helt meningsløs. På den anden side kan justering af registerværdier, der tilhører tredjeparts opsatte applikationer, underminere dem. Nogle applikationer kan komme til kort at starte helt, mens andre uventet kan stoppe med at arbejde.
Denne specifikke miner i sin nuværende variation er koncentreret om minedrift af Monero cryptocurrency, der består af en modificeret version af XMRig CPU-minedriftmotor. Hvis projekterne bekræfter succes, kan fremtidige variationer af BRTSvc.exe lanceres i fremtiden. Da malware gør brug af software program sårbarheder til at forurene mål værter, det kan være en del af et farligt co-infektion med ransomware og trojanske heste.
Fjernelse af BRTSvc.exe foreslås meget, da du ikke kun risikerer store elektricitetsomkostninger, hvis det fungerer på din COMPUTER, men minearbejderen kan desuden udføre forskellige andre uønskede opgaver på det og også skade din COMPUTER permanent.
BRTSvc.exe fjernelsesproces
TRIN 1. Først og fremmest, skal du downloade og installere GridinSoft Anti-Malware.
TRIN 2. Så skal du vælge “Hurtig scanning” eller “Fuld scanning”.
TRIN 3. Kør til at scanne din computer
TRIN 4. Når scanningen er fuldført, skal du klikke på “ansøge” knappen for at fjerne BRTSvc.exe
TRIN 5. BRTSvc.exe fjernet!
Video guide: Sådan bruges GridinSoft Anti-Malware til at fjerne BRTSvc.exe
Hvordan undgår din pc fra at blive inficeret med “BRTSvc.exe” i fremtiden.
En kraftfuld antivirus-løsning, der kan detektere og blokere fileless malware er, hvad du har brug for! Traditionelle løsninger opdage malware baseret på virusdefinitioner, og dermed de kan ofte ikke registrere “BRTSvc.exe”. GridinSoft Anti-Malware beskytter mod alle typer af malware, herunder fileless malware såsom “BRTSvc.exe”. GridinSoft Anti-Malware giver cloud-baseret adfærd analysator at blokere alle ukendte filer, herunder zero-day malware. Sådan teknologi kan opdage og helt fjerne “BRTSvc.exe”.







